Overview
China's mandatory national standard "Vehicle Information Security Technical Requirements" is currently at the public comment stage.
As one of the most discussed topics in the automotive industry, cybersecurity has shifted the focus of connected and automated vehicle development from feature differentiation for L2-L4 toward the basic attribute of vehicle safety.
Implications for Plug-and-Play
The draft of the national standard contains provisions that make future plug-and-play on vehicles difficult. For example, Clause 7.3 requires prohibition of unauthorized access to external interfaces (including USB interfaces, diagnostic interfaces and other interfaces), and it also requires access control for files on devices connected via external interfaces.
The implication is that external devices will only be allowed if they have been signed or authorized in some predefined way. "Authorization" is a process label that raises several practical questions:
Key Authorization Questions
Who authorizes?
In theory, vehicle manufacturers can evaluate and sign devices themselves or rely on signatures issued by third-party evaluation bodies. End users cannot realistically perform authorization themselves.
Whether manufacturers or third parties perform authorization, the effect is that users will lose general plug-and-play convenience and will be limited to using external devices that carry a designated signature.
What does authorization involve?
Applications designated as signed will need to undergo cybersecurity evaluation.
Whether manufacturers self-evaluate and sign or trust third-party signatures, the draft national standard requires manufacturers to assume cybersecurity responsibility for the signed applications and implicitly requires manufacturers to implement effective management of signed applications.
When must authorization be completed?
Because an application can only be used after receiving a designated signature, and a vehicle can only install and run the application after verifying the signature, compliance with the new national standard implies that vehicle control software may need to be updated before new applications can be added or existing applications can be upgraded.
Risk-Based Approach
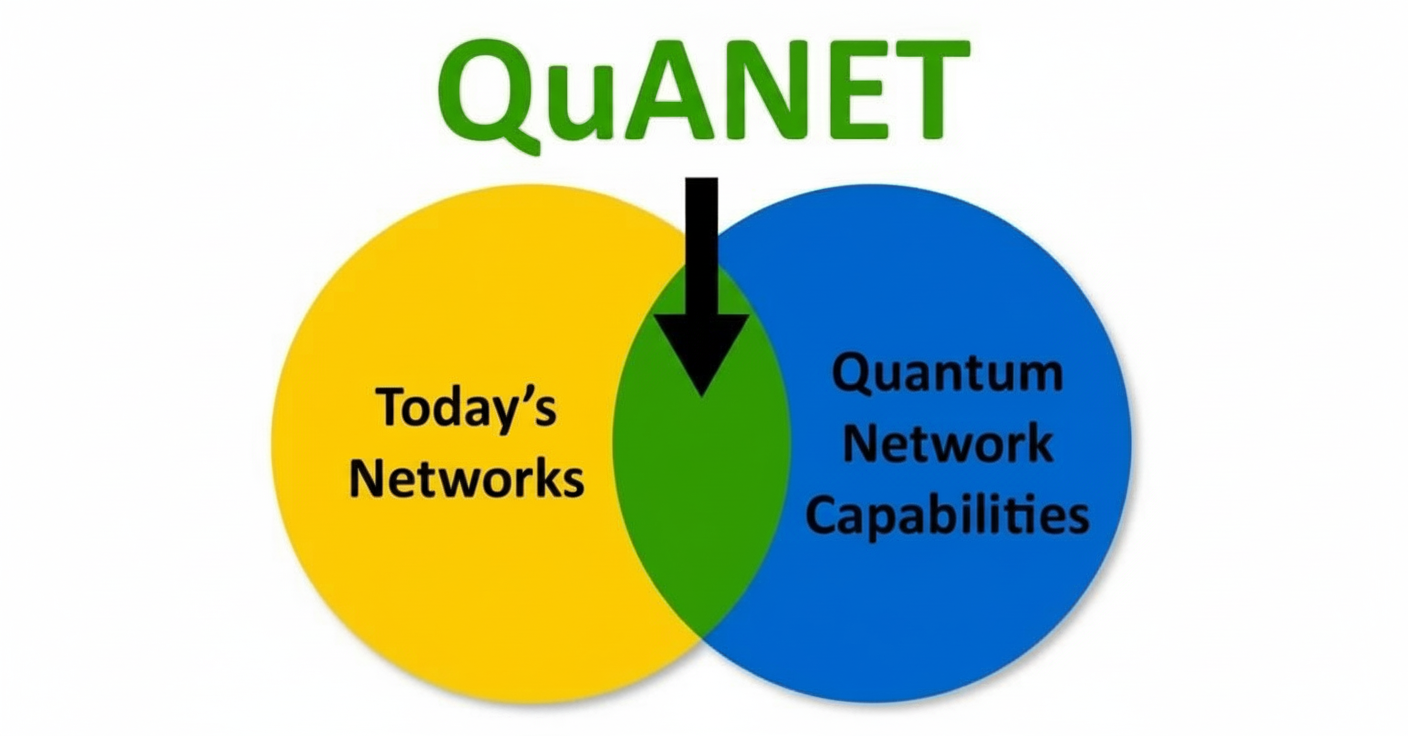
The "Vehicle Information Security Technical Requirements" is a national standard developed in China with reference to UN Regulation No. 155 (UNR155), and it reflects government management needs and the current state of industry development. Automotive cybersecurity cannot be risk-free; the goal is to reduce risk to an acceptable level.
"Acceptable" implies two points: accepting the existence of vulnerabilities, and ensuring that critical assets receive appropriate protection.
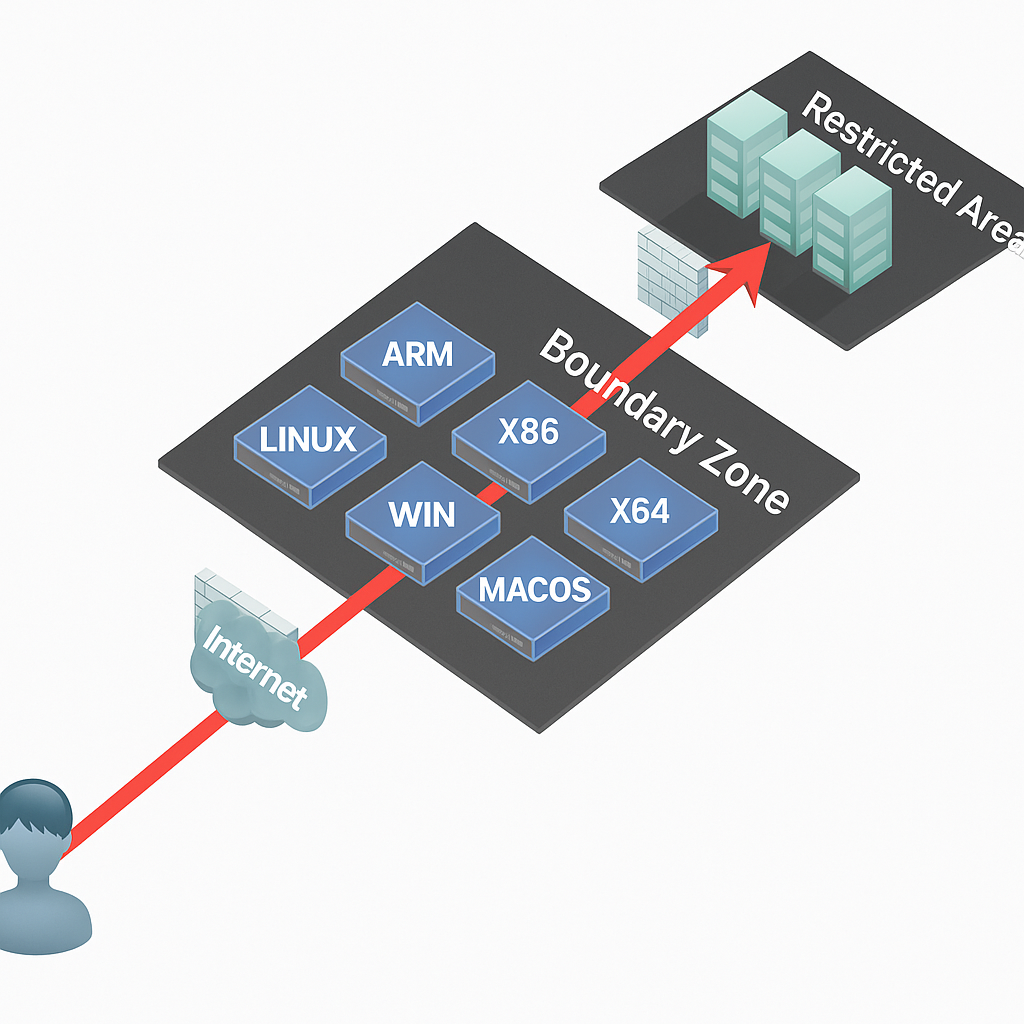
In other words, automotive cybersecurity should focus on defense rather than attempting absolute isolation.
Scope and Practical Concerns
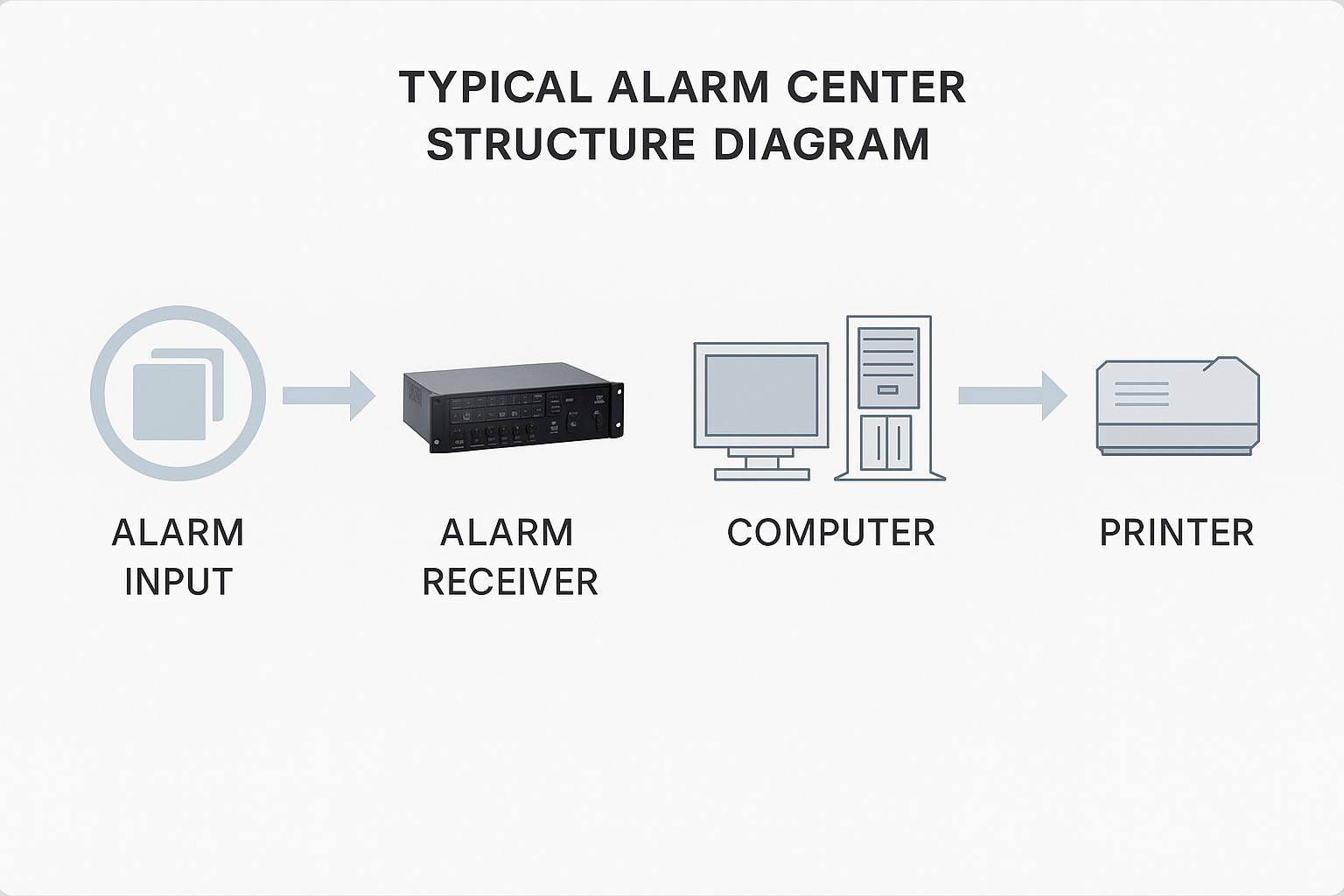
Consider an in-vehicle mobile TV that only shares the vehicle power supply with other electronic systems and has no wired or wireless network connections. Does it need to meet the requirements of the Vehicle Information Security Technical Requirements?
Are the telecom network ports and USB interfaces on the mobile TV considered "external interfaces" under Clause 7.3 of the draft national standard?
From a practical perspective the answer would be no, and there is little controversy. However, under the current wording of Clauses 7, 8, 9 and 10 of the draft standard, the answer could be yes.
It is hard to predict the full impact if the new national standard is strictly enforced. There is concern whether vehicle manufacturers can meet mandatory requirements and deliver compliant products at economically feasible cost.
Management System and Risk
The most important and fundamental requirement in the Vehicle Information Security Technical Requirements is the cybersecurity management system and the concept of "risk" as mentioned in the standard.
All technical requirements and management measures should be determined by risk.