Suppliers represent the largest single risk, but reducing attacks requires industry-wide collaboration.
Industry context
Semiconductor manufacturers are addressing how to secure a highly specialized, diverse global supply chain, especially as intellectual property value and software reliance increase while attackers become more sophisticated and better resourced.
Although security practices and standards exist, they are often confusing, onerous, and incomplete. Many gaps remain, particularly among smaller IP, equipment, and materials suppliers, where security is often basic at best. Historically, attention focused on vulnerabilities in chips and chip manufacturing firms. As companies in the semiconductor industry become more interdependent and designs grow more heterogeneous, the number of interactions increases. The weakest link threatens the entire supply chain; estimates suggest suppliers introduce more than 50% of security incidents.
Manufacturing is a high-value target: stolen data can enable competitors to deploy complex technologies. Even when attacks are stopped, breaches or intrusions can increase delivery timelines and raise investigation and remediation costs. Companies must also explain incidents to customers and regulators, which carries operational and reputational costs.
Industry leaders are aware of the expanding threat landscape. Collaboration was a major theme at the recent SEMICON West cybersecurity forum. Security leaders from Intel, TSMC, Applied Materials, ASML, Lam Research, and Peer Group emphasized the need to secure interactions among industry stakeholders and to adopt security standards and processes that prevent data loss without making security so burdensome that it impedes business.
Security remains a challenge across technical domains and becomes harder as more processes and equipment connect to the internet and to each other. No single control is perfect and no single solution is sufficient. Good security is an ongoing process that requires secure-by-design practices and supply-chain resilience. When vulnerabilities appear, they must be assessed and remediated.
Several CISOs present at SEMICON noted that roughly 60% to 90% of significant security issues are introduced by suppliers.
Vulnerabilities, obstacles, and solutions
Successful breaches can have wide-ranging effects: delayed shipments, IP loss, operational downtime, infected products, and brand damage.
Data sharing, cloud adoption, and smart manufacturing increase exposure. Joon Ahn, Vice President of IT at Amkor Technology, summarized key security vulnerabilities to consider:
- Data leakage: The growth of connected devices and data sharing increases the risk of unauthorized access to sensitive data unless it is properly protected.
- Physical security: As factories become more automated, physical security becomes more critical. Unauthorized access to production areas can lead to equipment damage or theft.
- Insider risk: Employees with access to sensitive systems and data can introduce risk through malicious intent or unintentional error.
Threats can target IT, facilities, and operational technology.
Robert Ivester, senior adviser for the NIST semiconductor engagement, noted that manufacturers and their supply chains increasingly rely on programmable systems and devices that interact with the physical environment, including industrial control systems and building management systems.
Facilities involve more than buildings. James Tu, head of enterprise information security at TSMC, explained that machines require power, chemicals, gases, and waste management to operate. “Facility security matters because it is a security issue. We focus on combining facility security with infrastructure security,” he said.
Amkor’s Ahn suggested steps to address these vulnerabilities, such as risk assessments, staff training, and physical security measures.
For software, compliance requires understanding your footprint and building sustainable security practices. Mike Kropp, President and CEO of Peer Group, noted that software often has special versions or requirements across customer sites. “So our software has different personalities. We need repeatable processes around our footprint,” he said. Kropp described Peer Group’s footprint in terms of the number of staff with access to software IP, customer sites, and connected devices, and noted the need to track supported operating systems and third-party libraries.
Security monitoring should be continuous, automated where possible, and integrated into the development process. “We treat security defects like other defects: assign severity, create work items, and include them in developers’ task lists. If we wait until the end of the process, it is too late. Security must be part of our development environment,” Kropp said.
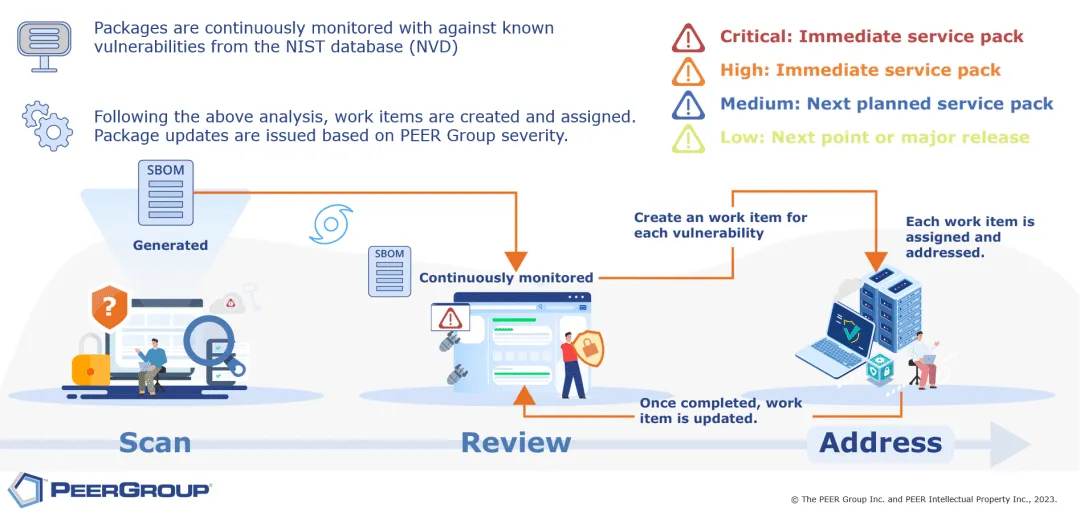
Figure 1: Example software vulnerability workflow
Data sharing and cloud security remain concerns. James Lin, Vice Director of Smart Manufacturing at UMC, said cloud information security is a consideration on the path to autonomous smart factories, especially when adopting generative AI. Training advanced generative AI models requires using sensitive enterprise data on large GPU environments. If companies use enterprise cloud solutions, strong information security certifications are essential.
Generative AI introduces new risks because it can piece together data fragments rather than requiring all data in a single location. Reports note engineers using ChatGPT-style tools to optimize test sequences and transform meeting notes into presentations, which can result in sharing sensitive information externally.
The cloud offers advanced security, but it is not a complete solution. David Park, vice president of marketing at Tignis, suggested that cloud data security from major providers is likely stronger than most on-premises environments. The larger issue is improper user authentication: granting inappropriate access to employees can be as damaging as an external hacker. As smart manufacturing becomes the norm, internal security and access control will be major challenges.
Data moving to and from the cloud and between companies or offices can be far less secure. While encryption is a standard protection, it can be problematic in complex supply chains because many organizations block incoming encrypted data and software.
Jason Callahan, Vice President and CISO at Lam Research, observed that organizations often operate inconsistently with respect to data. “We operate from a zero-trust perspective, but we share IP. There is a lot of trust involved. We work with suppliers to share information effectively, but we encounter obstacles. Fundamentally, as security practitioners, we distrust encrypted content. Many block encryption entering their environment. If you are a network person, encryption can be problematic. This is a major vulnerability. We reject encrypted content, which is ironic because we push encryption internally,” he said.
Encryption raises three traditional concerns: it can conceal malware until decrypted; it can hide data exfiltration; and it can complicate forensic discovery in legal matters. Callahan argued that deep defense, including antivirus and endpoint detection and response, should underpin security programs. Data leakage is primarily an internal risk that can be addressed with appropriate tools. Legal-forensic concerns are a special case, and allowing encrypted transmission of IP for secure transfer may be necessary.
Vendor security management
All CISOs agreed that managing supply-chain security is essential, but it is difficult in practice due to the large number of suppliers.
For software vendors, supply-chain risk includes third-party libraries; for equipment vendors, it includes parts suppliers. A factory’s supply chain includes equipment manufacturers, materials suppliers, software vendors, and hardware providers. ASML’s CISO Aernout Reijmer said the company’s equipment comprises roughly 380,000 components from about 5,000 suppliers.
Companies such as TSMC and ASML provide supplier training and set up alerts to support smaller suppliers that may not have large security teams.
Standards
The NIST Cybersecurity Framework offers guidance for building organizational practices. Multiple ISO standards also address information security. However, these generic standards are not always easily applied to complex factory environments with integrated third-party equipment.
Wafer fabs combine high value, high complexity, and a historical reluctance to update factory equipment. This makes fabs and foundries particularly vulnerable and has driven SEMI members in Taiwan and North America to push equipment-focused industry standards. SEMI working groups defined factory equipment security standards E187 (Taiwan) and E188 (North America). These standards include:
SEMI E187: Cybersecurity for Fab Equipment
- A baseline set of minimum security requirements for fab equipment designed to run Linux or Windows, intended for OEM implementation.
- Focus on cybersecurity, endpoint hardening, and security monitoring.
SEMI E188: Ensuring Equipment Integration Is Free of Malware
- A framework to mitigate malware risks during equipment installation and maintenance based on explicit reporting requirements.
- Requires malware scanning, system hardening, and inspection of incoming software and patches for known vulnerabilities.
These standards are complementary. SEMI E187 aims to ensure equipment is designed and configured at shipment to meet baseline security and maintainability. SEMI E188 addresses a subset of these topics with requirements to reduce the risk of introducing malware during equipment installation and field support. The standards work continues to expand different E187 topics.
Manufacturers are adopting these standards and requiring compliance for new equipment.
Assessment
Security assessments help determine supplier maturity and can influence procurement and improvement measures. TSMC’s Tu described a supplier scoring process that includes third-party online assessments and a 135-question self-assessment covering areas such as:
- certification and risk assessment
- inventory management and physical security
- cybersecurity event detection and response
- system development and application security
- cybersecurity and change management
- organizational policy and human resources safeguards
- computer operations and information management
- identity and access management
Major semiconductor manufacturers perform well and complete assessments for their customers. However, when every company has its own assessment, the burden becomes significant. “We run many security assessments across the industry. We do not yet know what we have rolled out in the supply chain. If we overcomplicate or overengineer this, we will not find a solution,” Reijmer said.
Others raised similar concerns. “I have 15 people dedicated full time to answering these questions so I can sell my products,” said Brent Conran, CISO at Intel. “Could those resources be better applied to actual cybersecurity work? The industry needs to consider that what was done over the past 20 years may no longer be sufficient given how rapidly we have digitized.”
Assessments also often omit key attributes related to recovery and resilience. “Our efforts are not tied to risk reduction,” said Kannan Perumal, CISO at Applied Materials. “We have many initiatives that could help, but we are still struggling because we have so many suppliers and limited resources.”
Perumal noted the lack of a standardized semiconductor supply-chain risk assessment. Each company uses its own assessment, usually executed by the supplier’s security team when one exists, making the process resource intensive. Assessments also often overlook recovery and resilience concerns.
Perumal compared how the semiconductor and automotive industries manage large supplier bases. The comparison supports several CISOs’ points: the chip industry needs efficient frameworks, common standards, and third-party certification bodies to scale the process.
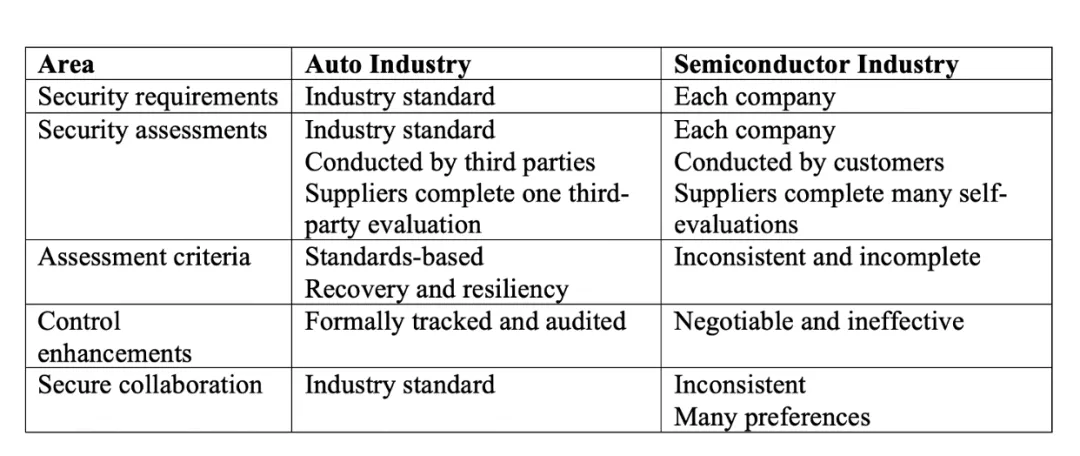
Figure 2: Comparison of supply-chain cybersecurity risk management
Call for collaboration
Because of deep interdependence across the semiconductor supply chain, protection beyond individual company boundaries is necessary. Multiple operational touchpoints and attack surfaces require joint efforts to be effective and cost-efficient. “We cannot do this alone. We all need to work together across the supply chain and understand the many things we must do to keep the machine running,” said Intel’s Conran.
Advancing cybersecurity collaboration goes beyond agreeing on standards and vendor assessment processes. It requires incorporating expertise from major fabs and equipment suppliers so the industry can learn quickly and respond to common threats. SEMI is forming a cybersecurity alliance to enable this level of collaboration.