Theoretical background
1. Malware classification
1.1 Remote-control trojans: can remotely control infected hosts to perform monitoring, file operations, network attacks, and other functions.
1.2 Password-stealing trojans: steal passwords or account information by logging keystrokes or capturing screenshots.
1.3 Phishing trojans: impersonate bank or e-commerce sites to trick users into revealing sensitive information.
1.4 Ransomware: encrypts user files and demands payment for decryption.
1.5 Downloader trojans: download other malicious software onto the infected host, such as adware.
2. Remote-access trojans
These can provide interactive access to target machines (real-time or non-real-time), accept commands to trigger malicious functions, and collect various data from the target. Interaction is bidirectional between the attacker and the controlled host.
3. Threat intelligence IOCs
IOCs are often domains, IPs, or URLs (sometimes SSL certificates, hashes, etc.). These IOCs can be distributed to security devices such as NGFW, IPS, and SIEM for detection, alerting, or real-time blocking. IOC feeds normally include severity, threat actor, malware family, and contextual data to help prioritize incidents and guide response activities. A common use is using IOC feeds to detect compromised internal hosts via log analysis.
4. DarkComet
DarkComet is a remote-access trojan (RAT) developed by Jean-Pierre Lesueur (aka DarkCoderSc). It began spreading in early 2012 and has been used in many targeted attacks. It can capture webcam images or screenshots, record audio via a connected microphone, and gain full control of infected machines.
5. DarkComet main capabilities
Remote control, user-behavior monitoring, installing a SYSTEM-level backdoor for attackers, stealing and exfiltrating user information, and downloading additional malware.
Basic analysis
The sample file is not large and is not digitally signed.
Static analysis shows the sample was developed in Delphi. Delphi remains present in some legacy internal tools and systems, so its use suggests older development environments.
Analysis also shows the sample does not depend on third-party DLL modules, so most functionality is implemented within the malicious EXE itself.
Static analysis has limited visibility into runtime behavior, so next we perform dynamic analysis on the EXE sample.
Dynamic analysis
1. Hidden startup
When the malicious sample is executed, it first renames the original program to ._cache_[original].exe and sets that file as hidden, then runs the infected EXE. The ._cache_ file is the original, uninfected program.
2. Dropping files
After startup, the sample creates folders at specified paths and drops its payload files into those folders.
3. Setting persistence
The sample writes application information to the registry path HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run to achieve autostart behavior.
4. Launching helper programs
The sample executes a BAT file which starts three application components.
The main application claims to query QQ-related information and to perform SMS-bombing against specified phone numbers.
5. Query and SMS-bombing features
QQ-related queries are implemented by calling QQ-related APIs to fetch information.
The SMS-bombing function cycles a configured list of domains and repeatedly attempts to register users with a target phone number on those domains to trigger mass SMS messages.
Function analysis
1. Infection mechanism
The sample searches the Desktop, Downloads, and Documents directories for EXE files. It checks whether those EXEs contain EXEVSNX or EXERESX sections; if present, it infects those applications for propagation.
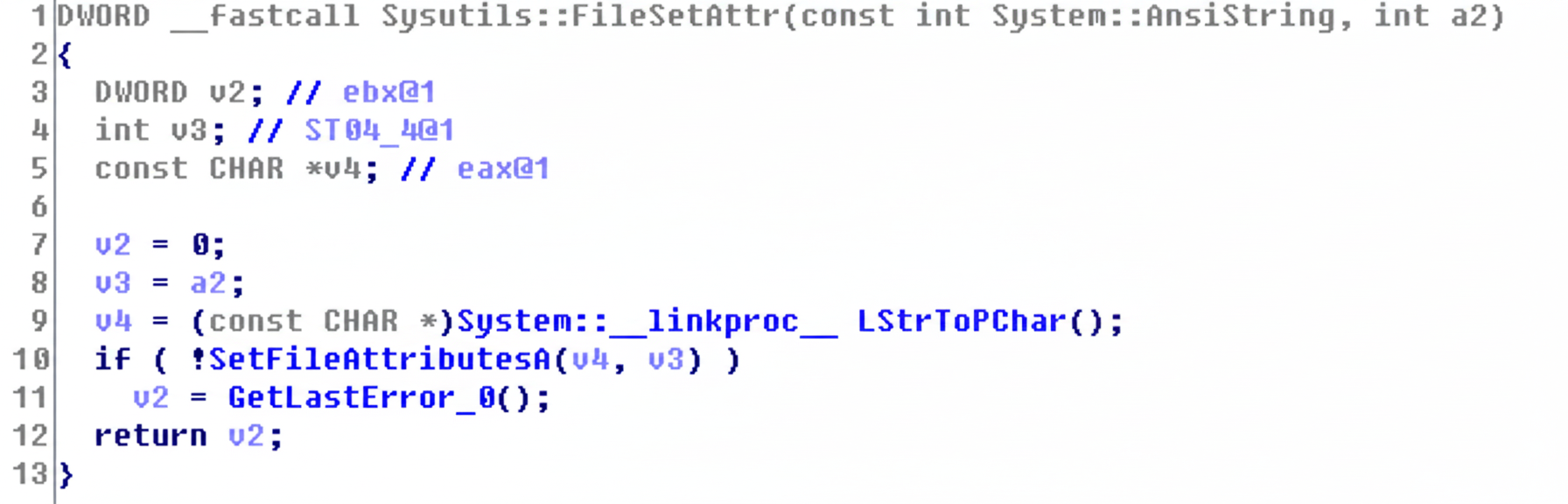
2. Setting hidden attributes
It calls the system API SetFileAttributesA to set files as hidden. If the hidden attribute is enabled, the application will not be visible unless hidden files are shown.
3. Environment data collection
The malware collects system and hardware information from the infected computer and uploads it to its command-and-control servers.
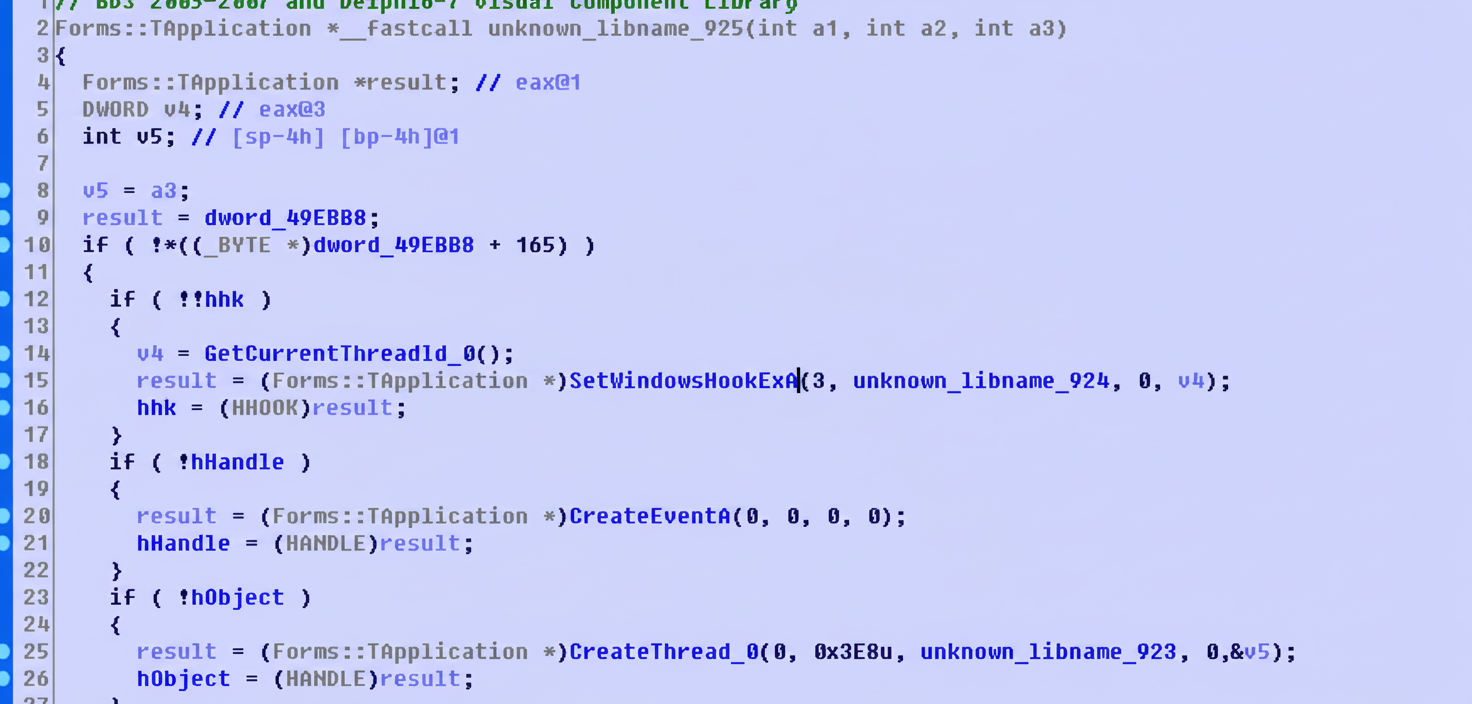
4. Keylogging
It installs a keyboard hook via SetWindowsHookExA to monitor keystrokes and upload captured input.
5. Email exfiltration
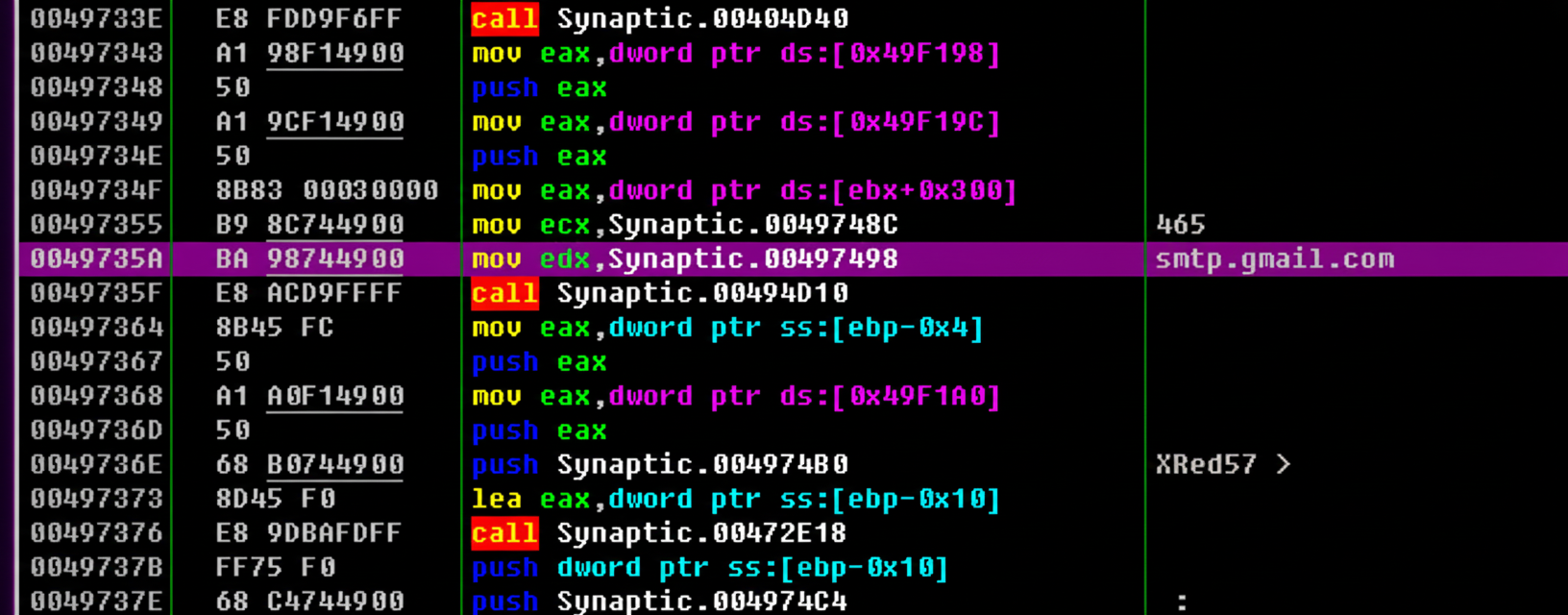
The sample uses Delphi's built-in email library and sends mail through smtp.gmail.com to the address xredlinel@gmail.com.
IOCs
The domain xred.mooo.com was extracted from the sample and is classified as malicious.
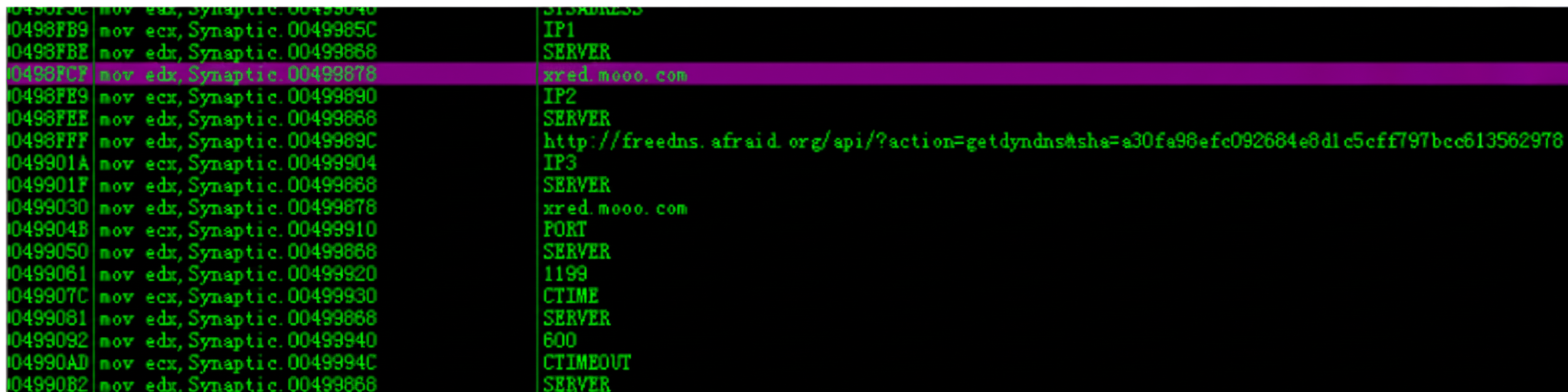
One server IP found in the sample: 124.222.126.226, which is also recorded as a threat indicator.
Mitigation and recommendations
Practical security recommendations:
- Do not download or run applications from untrusted sources or social platforms.
- Install and keep antivirus/endpoint protection up to date with the latest signature feeds.
- Before running an installer, verify file size and digital signature and scan with antivirus tools.
Suggested remediation steps for infected systems (automation via antivirus tools or scripted remediation is recommended):
- Use updated antivirus/EDR tools to detect and remove infected applications and perform repair actions.
- Manually remove registry entries that set programs to autostart and terminate malicious processes if necessary.
- Manually inspect Desktop, Downloads, and Documents for EXE files. Use PE-section inspection tools to check for EXEVSNX or EXERESX sections; infected files should be removed. Alternatively, disable hidden-file filtering and search for files prefixed with ._cache_ to locate original saved binaries.