Overview
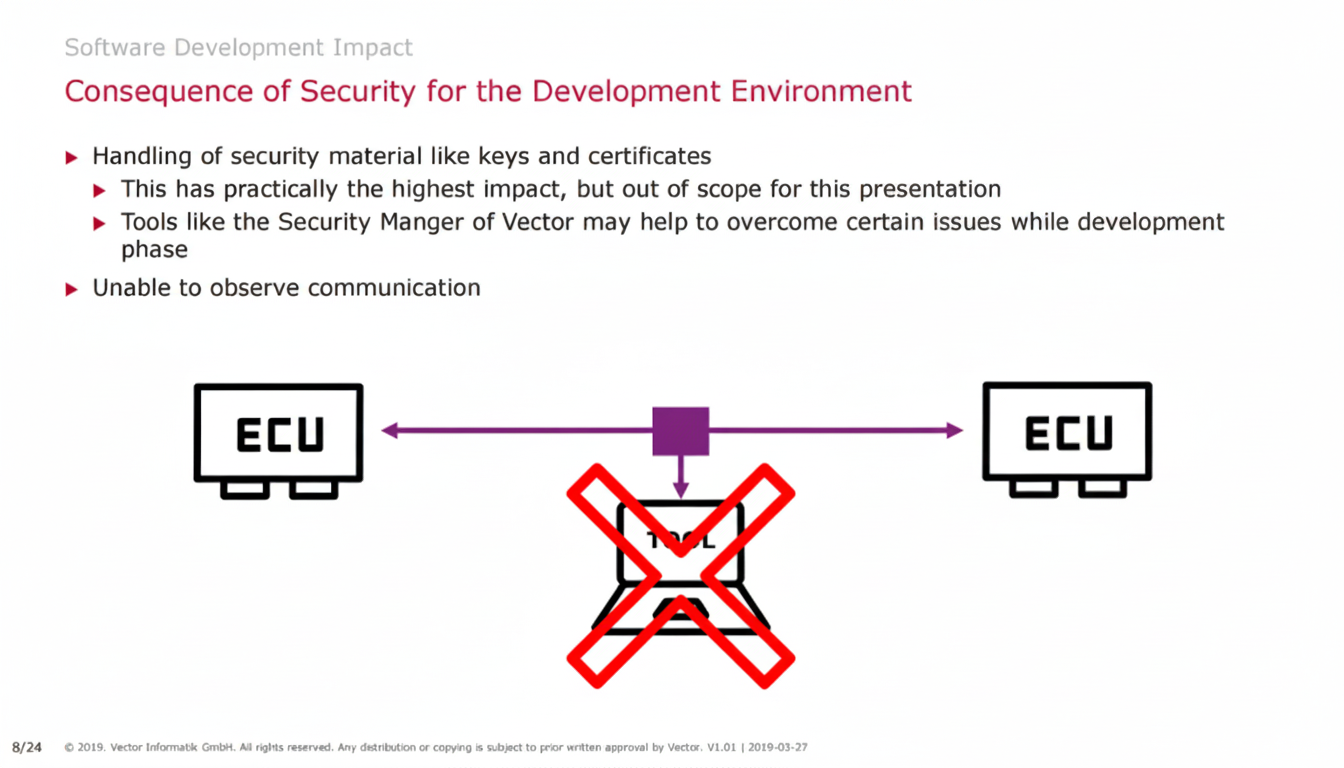
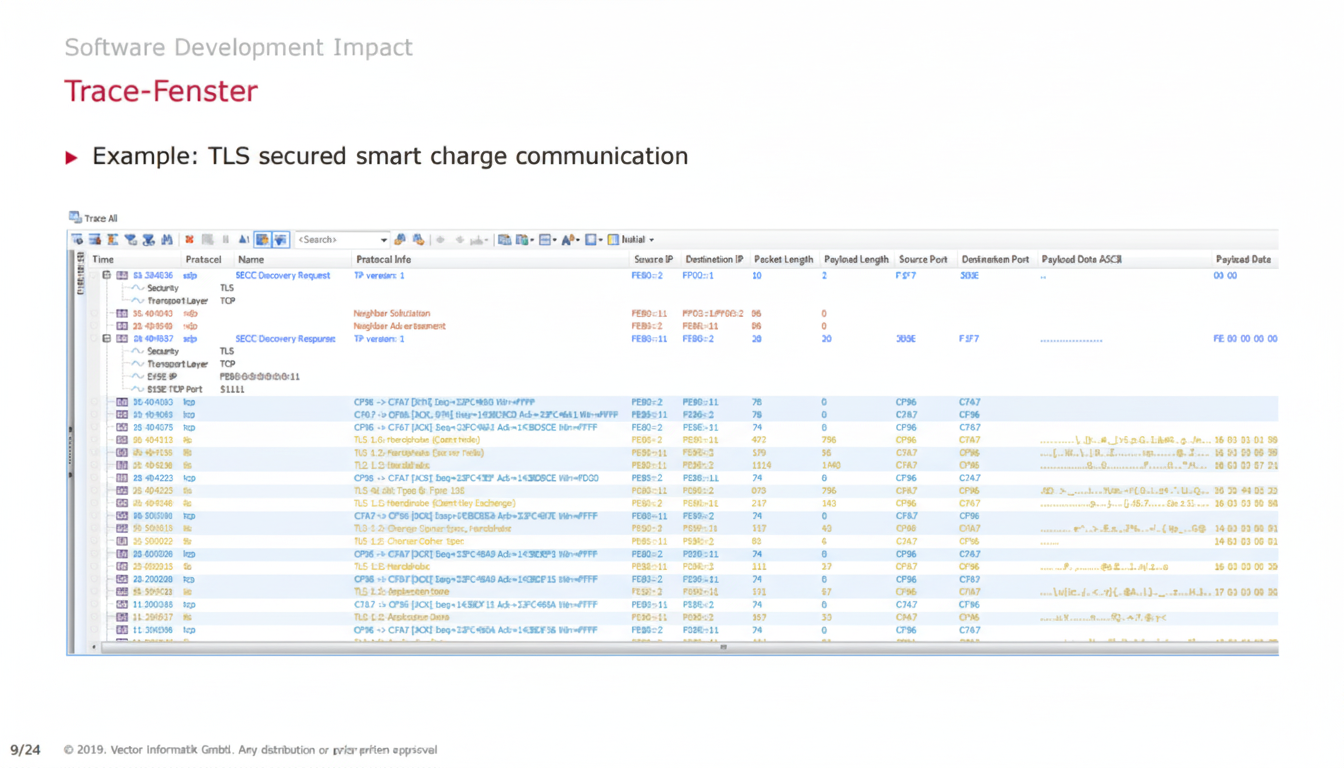
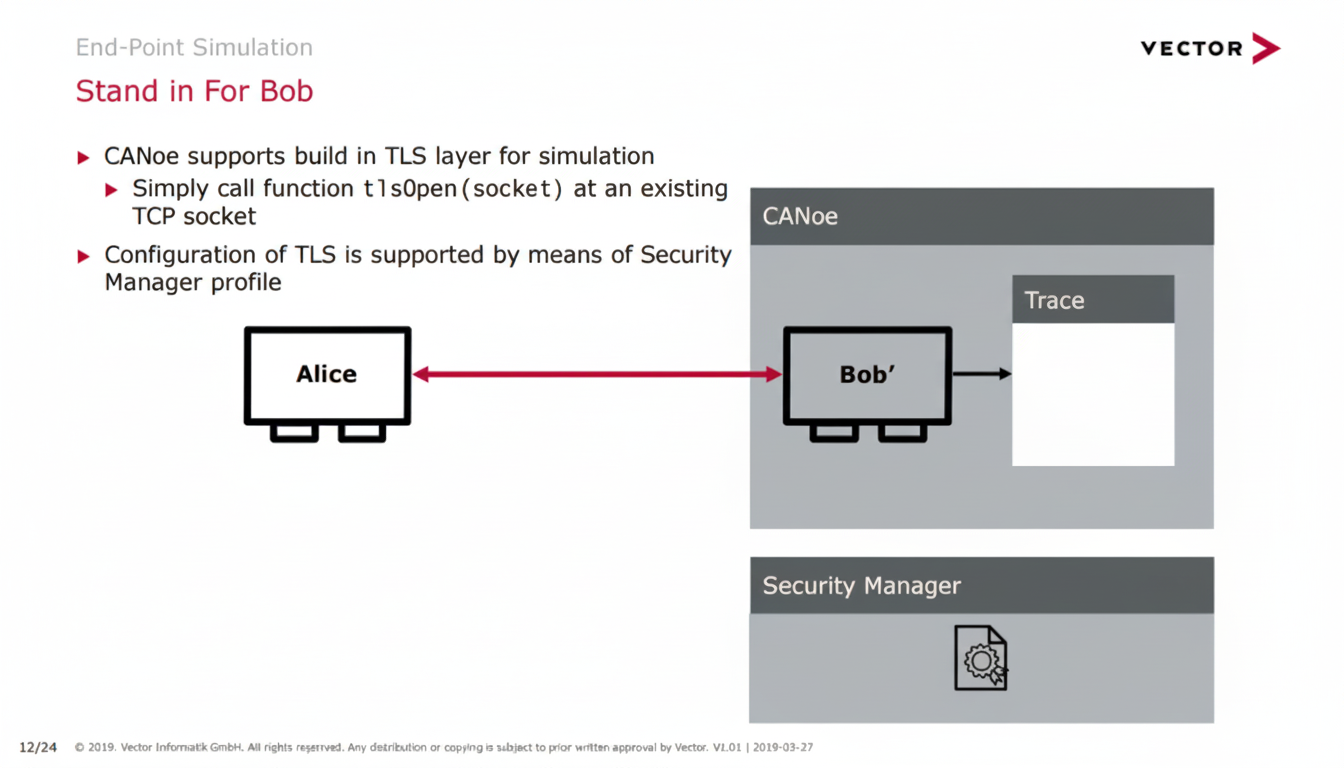
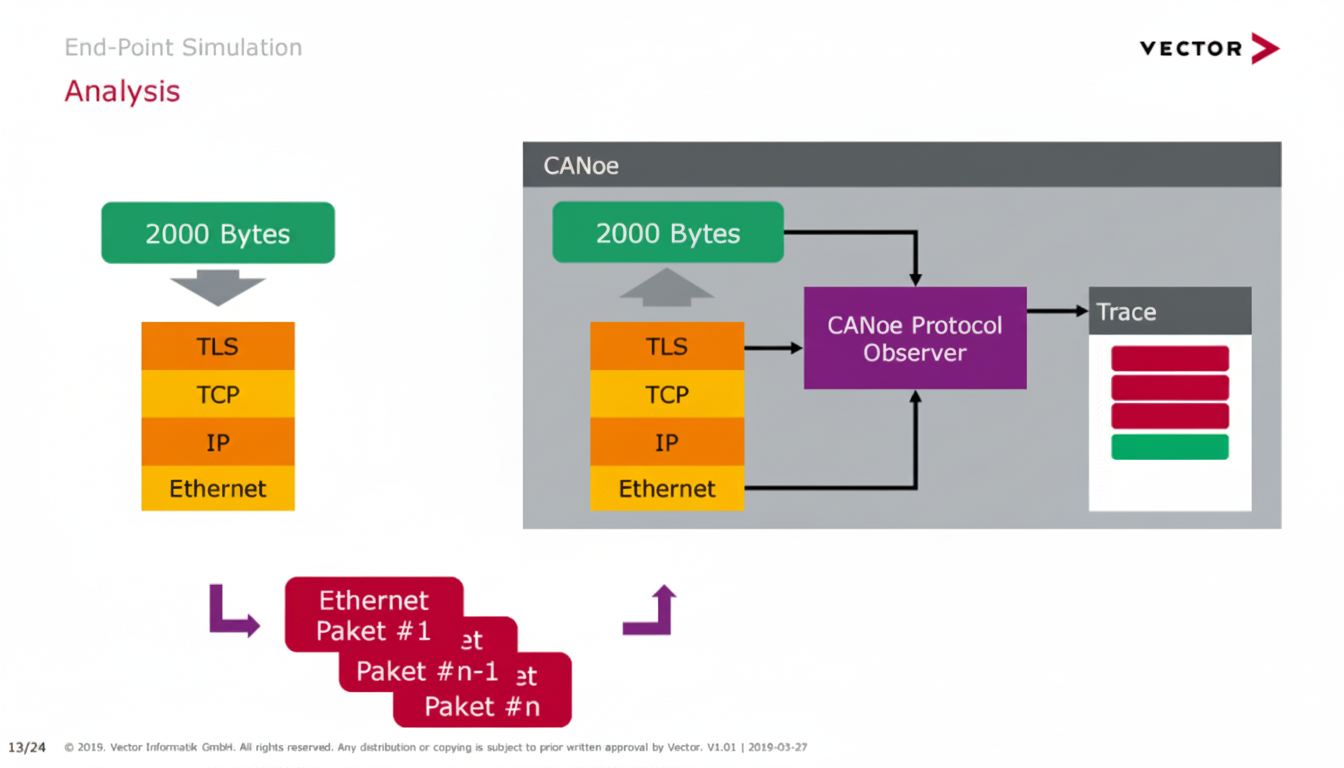
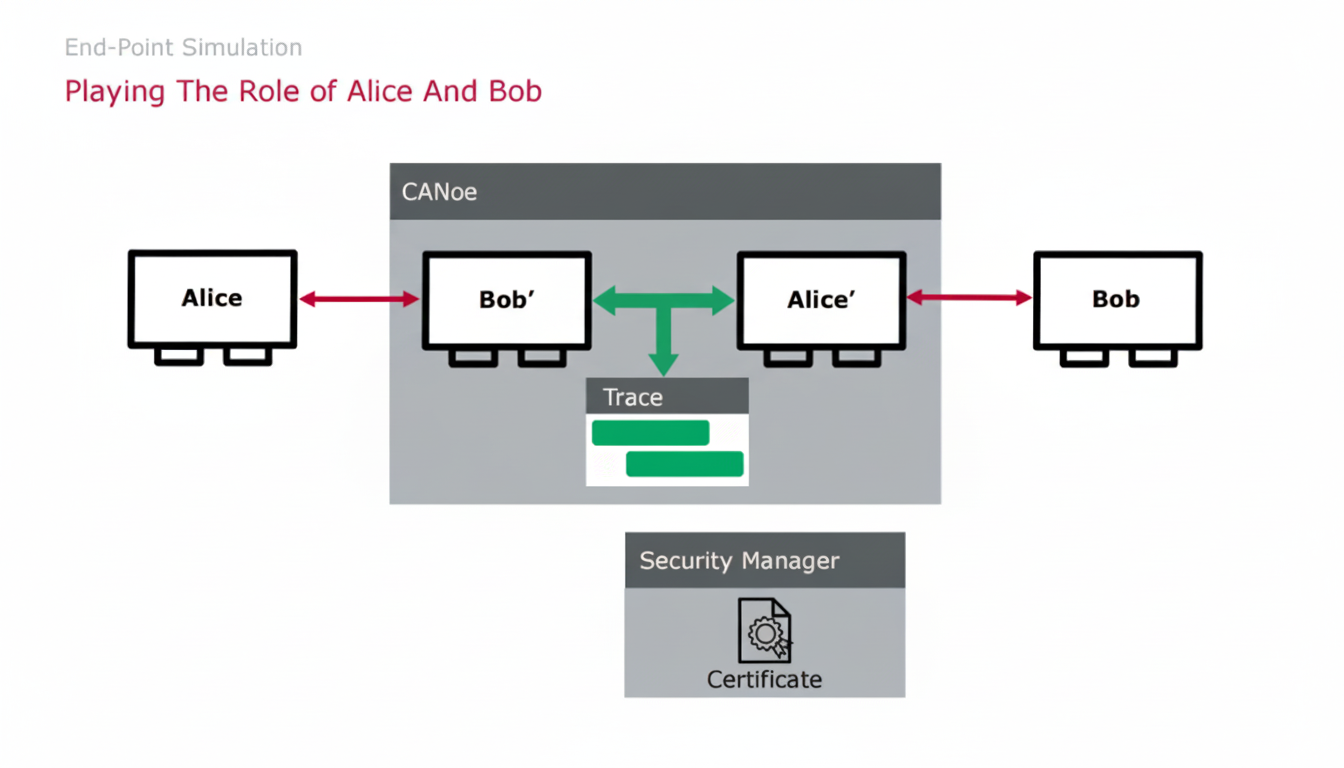
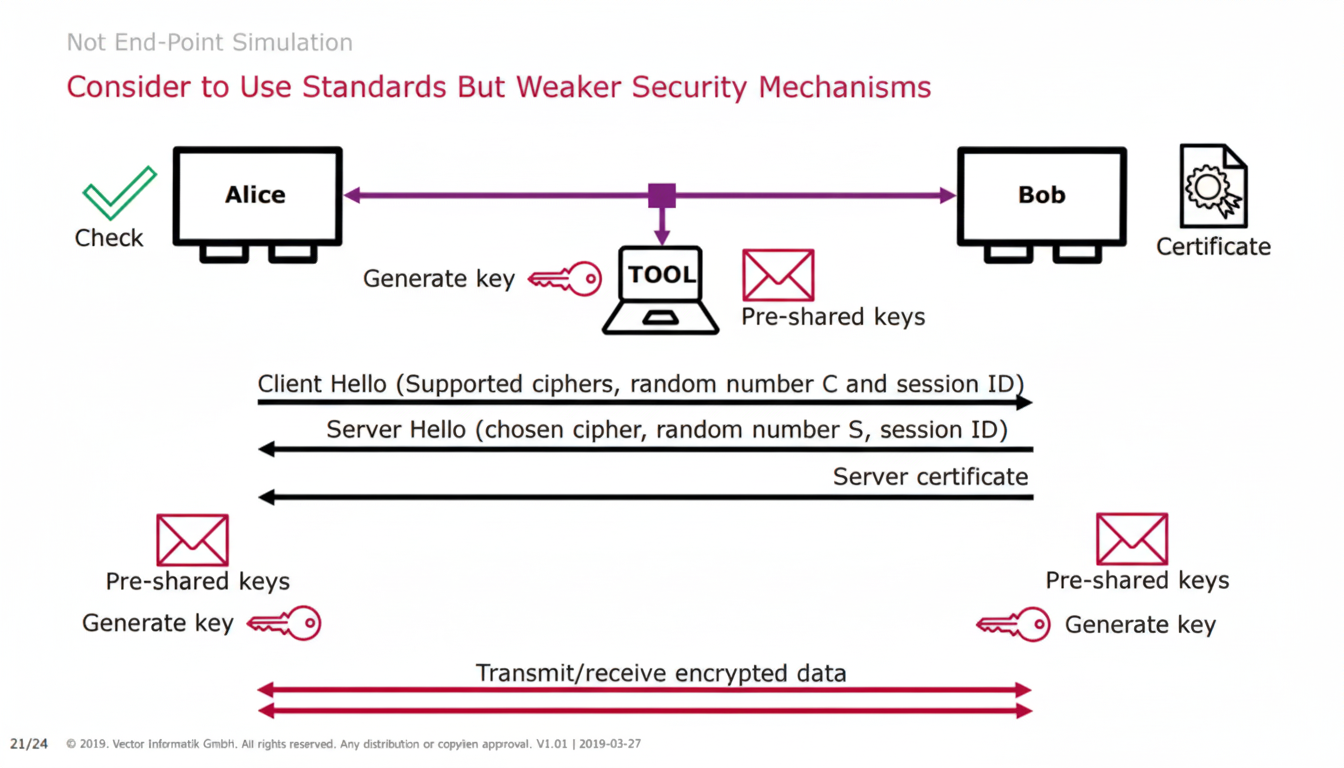
Because decrypted messages are available, application-layer issues can be analyzed. Even messages/signals can be manipulated. The security layer on the actual ECU does not need any modification. Logging for subsequent data analysis is simpler only when private certificates are shared with the tool.
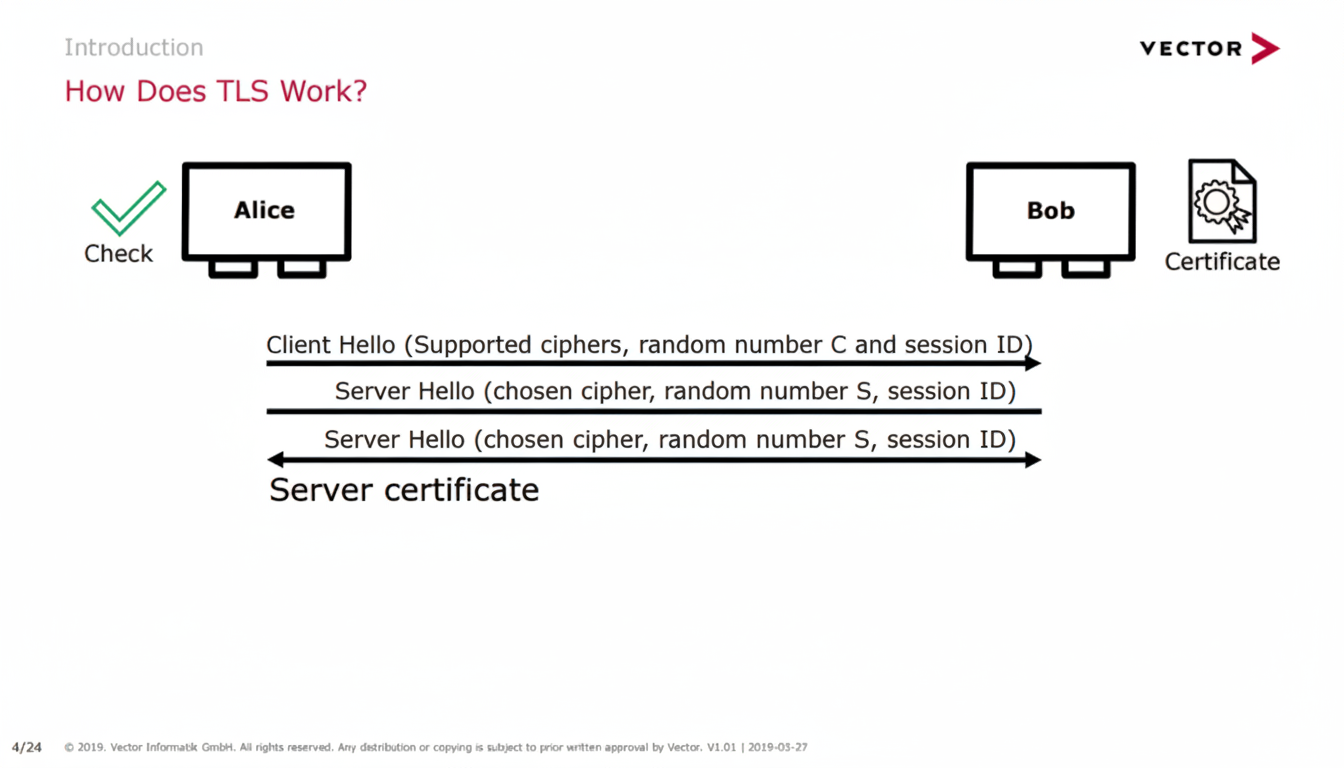
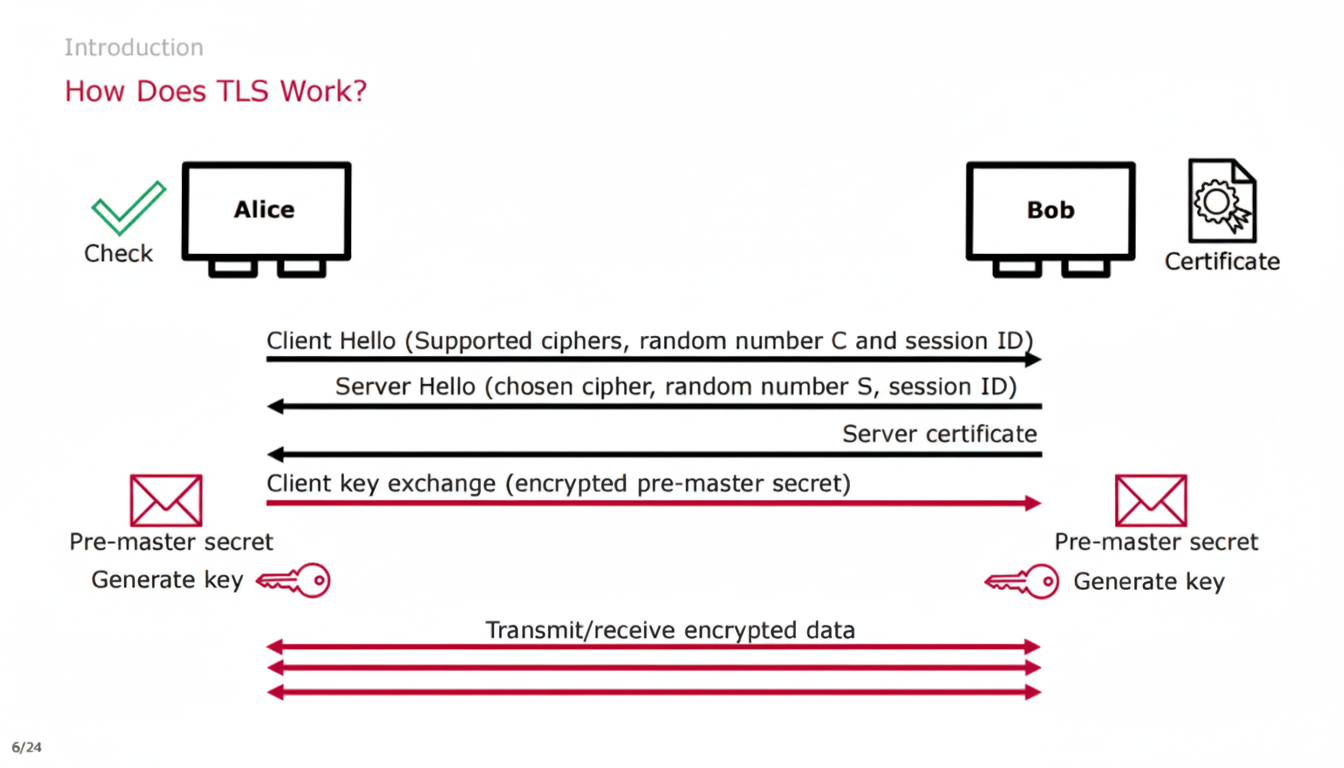
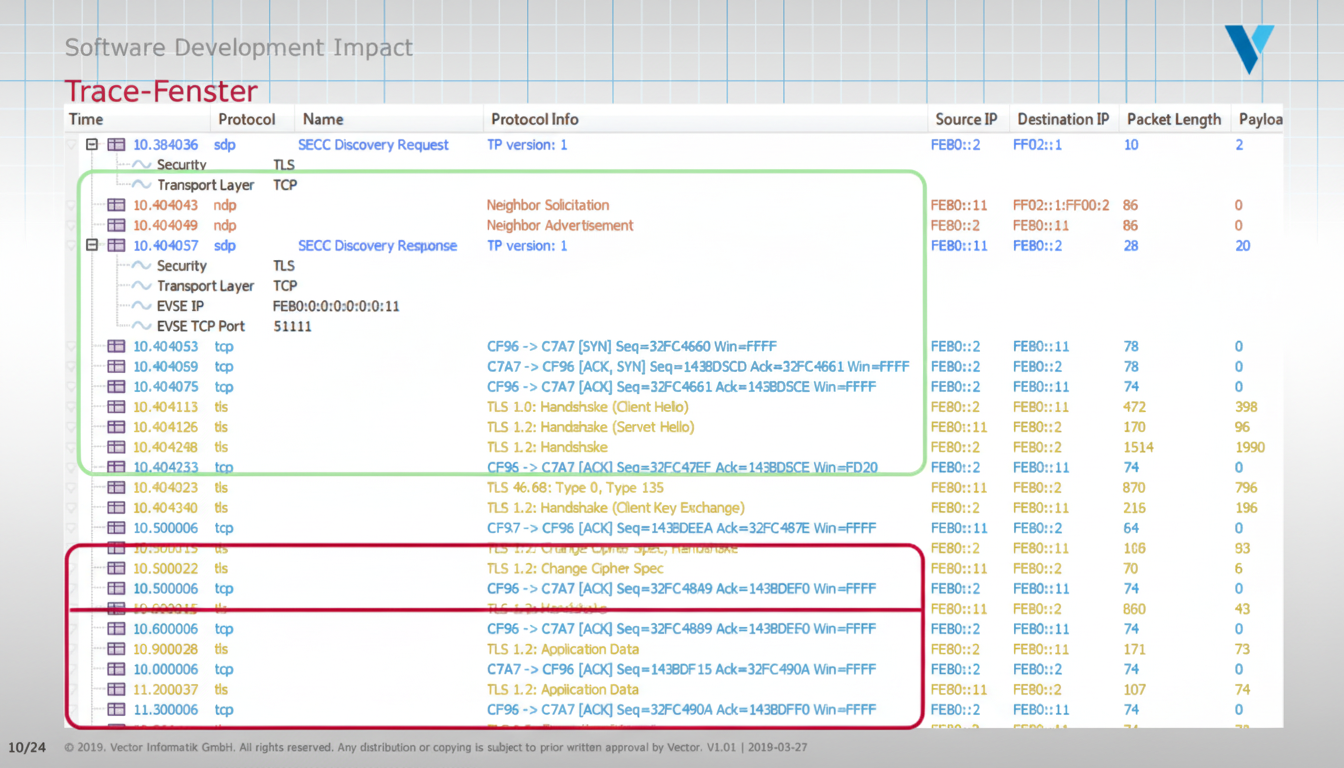
Figures