Overview
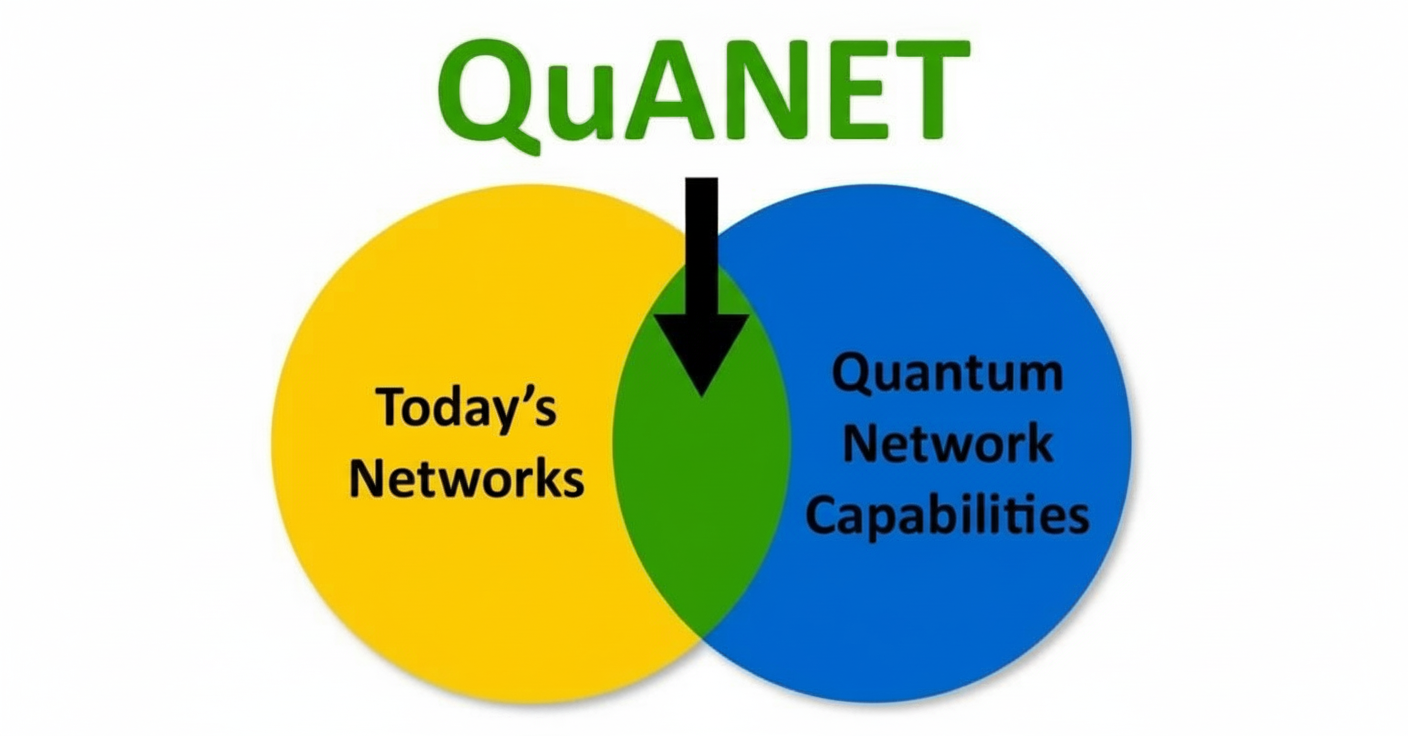
Network monitoring systems are used to observe and manage traffic, devices, and activity on a network. Common system types include tools for traffic inspection, threat detection, log analysis, and access management.
Common types of network monitoring systems
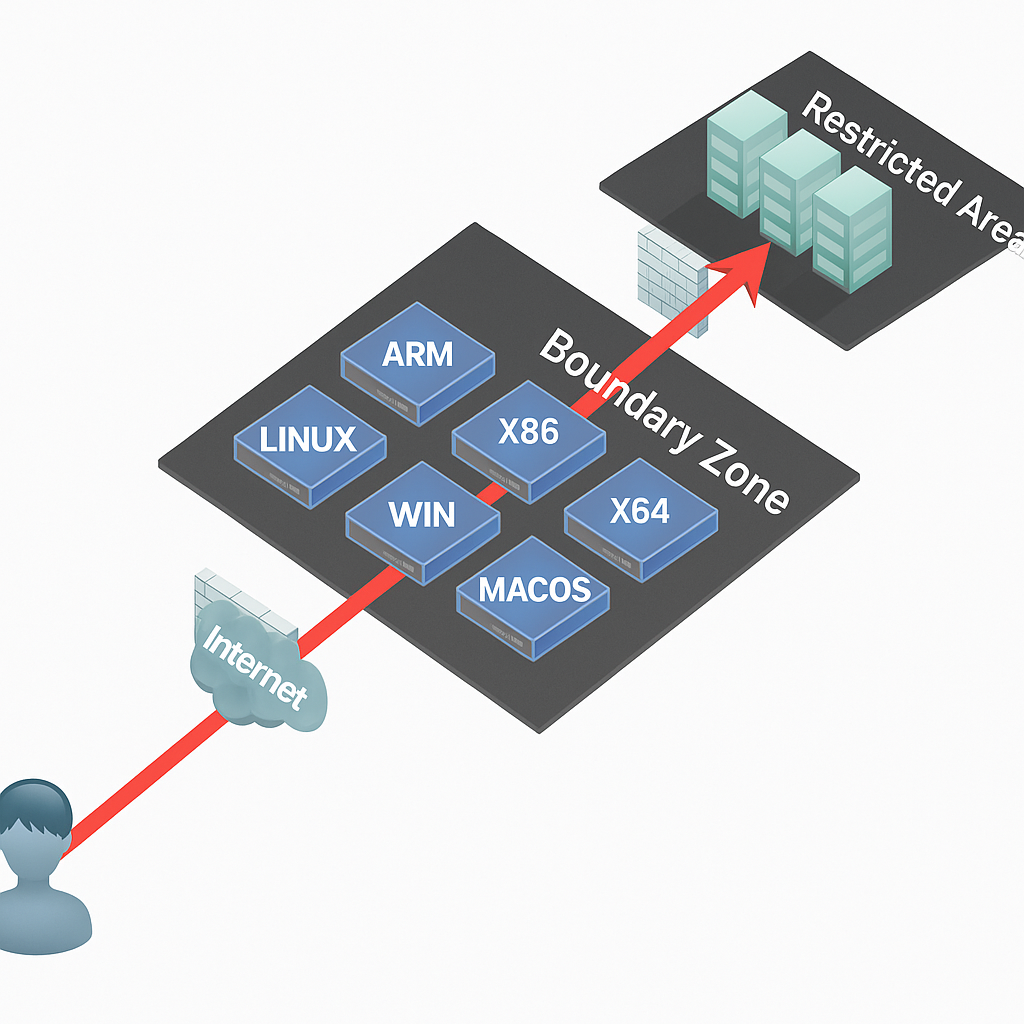
Firewall
A firewall monitors network traffic and allows or blocks connections based on predefined rules. It can detect and block potential intrusions and protect the network from unauthorized access.
Intrusion Detection System (IDS)
An IDS detects and alerts on anomalous behavior or attack attempts by monitoring network traffic and system logs. It identifies potential security threats by recognizing known attack patterns or abnormal activity.
Intrusion Prevention System (IPS)
An IPS includes IDS capabilities and can actively block detected threats. It can automatically terminate malicious connections or take other mitigation actions based on detected threats.
Network Traffic Analysis Tools
These tools capture and analyze network traffic to identify anomalies, bandwidth usage, and performance issues. They provide visibility into traffic patterns, protocol usage, and network performance.
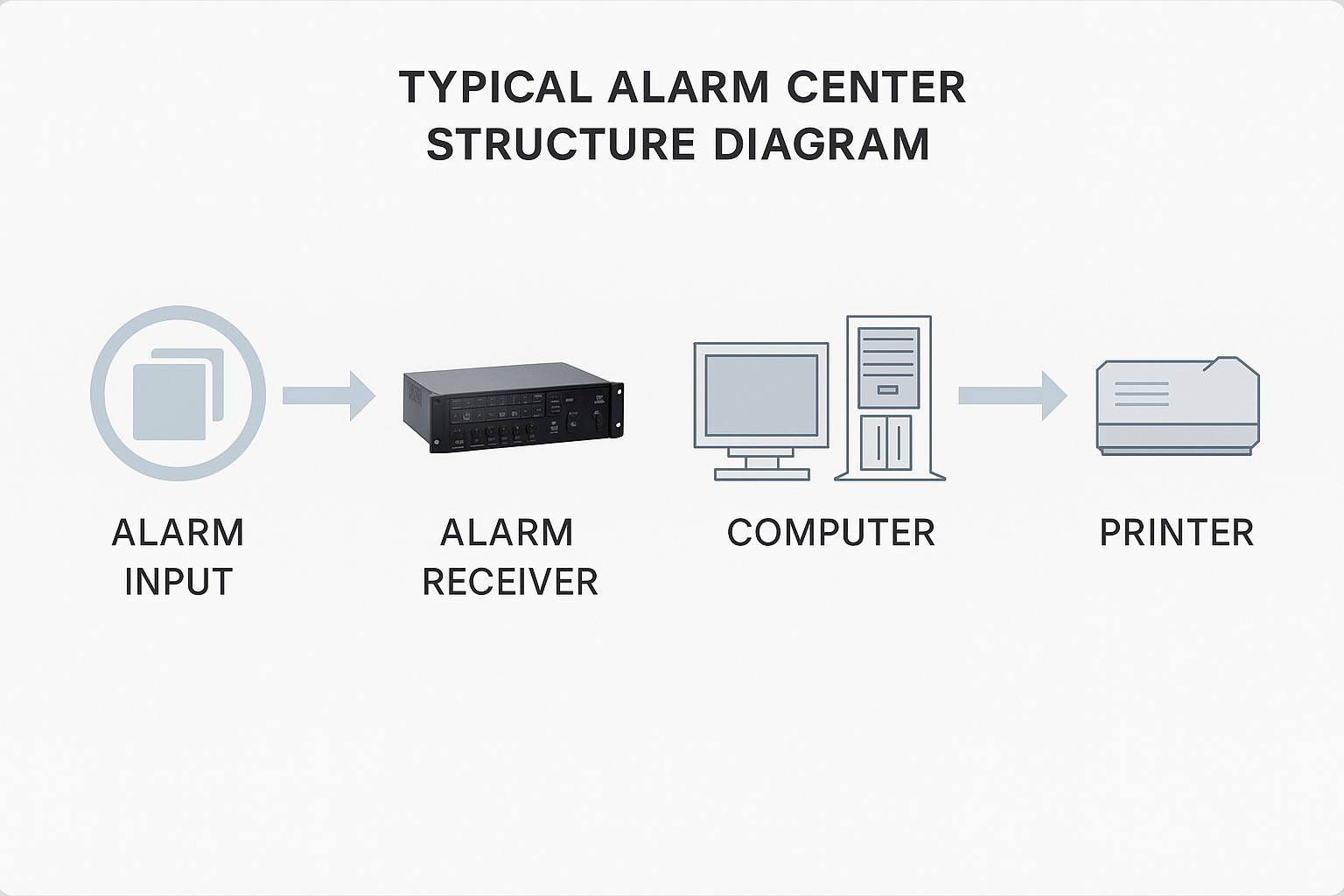
Network Log Analysis Tools
Log analysis tools collect and analyze logs from network devices, servers, and applications. They help detect unusual events, failures, and security incidents to enable timely response.
Identity and Access Management (IAM)
IAM systems manage and monitor user access to network and system resources. They handle roles, permissions, and authentication methods to ensure only authorized users can access sensitive data and services.
Devices required for network monitoring
Typical devices used to implement network monitoring include:
- Firewall: A core device for monitoring and controlling traffic and preventing unauthorized access.
- Router: For forwarding packets across networks and applying monitoring or security policies.
- Switch: Connects network devices within a LAN. Managed switches can provide monitoring features such as port mirroring for traffic capture and analysis.
- IDS/IPS: Devices deployed at network edges or critical points to detect and block malicious activity.
- Network traffic analyzer: Captures traffic and performs deep analysis to identify anomalies and security threats.
- Log server: Centralized storage and management for logs from various network devices and applications, essential for monitoring and forensic analysis.
Additional devices may be required depending on monitoring needs, such as network cameras or specialized security gateways. When selecting and configuring monitoring equipment, plan according to the network topology and security requirements, ensure device compatibility and interoperability, and consider compliance and privacy protections.
Note: Use of network monitoring must comply with applicable laws and privacy regulations. Respect employee and user privacy and take appropriate measures to protect the confidentiality of monitoring data.