1. Intrusion Detection
Intrusion detection refers to identifying system intrusions or intrusion attempts by analyzing behaviors, security logs, audit data, or other information available on the network.
Intrusion detection technology is a method used to discover internal attacks, external attacks, and operator errors. It is a dynamic cybersecurity technique that uses different engines to analyze network data sources in real time or periodically, extract threat-related parts, and trigger response mechanisms.
The combination of intrusion detection software and hardware is called an intrusion detection system (IDS). It is a set of software or hardware that monitors events occurring in computer systems or network systems and performs security auditing based on rules. As a complement to firewalls, IDS helps administrators manage security (including auditing, monitoring, attack identification, and response) and improves the integrity of the information security infrastructure.
As an important network security tool, an IDS can perform real-time detection of system or network resources to discover intruders in time and prevent authorized users from making erroneous operations on resources. It collects information from several key points in the computer network system, analyzes that information, and checks for behavior that violates security policies or signs of attacks. Intrusion detection is often considered the second line of defense after firewalls, providing real-time protection against internal attacks, external attacks, and operator errors without significantly affecting network performance.
1.1 Components and Functions of an IDS
Standardization efforts for intrusion detection are led by organizations such as the IETF Intrusion Detection Working Group (IDWG) and the Common Intrusion Detection Framework (CIDF). CIDF defines a standard language for IDS to express detection information and communication protocols between IDS components. CIDF-compliant IDS can share detection information, communicate, coordinate, and integrate unified configuration, response, and recovery strategies. CIDF's main role is to integrate various IDS so they can work together, forming the basis for distributed IDS.
An intrusion detection system consists of four components:
1. Event generator: The information source that provides event records. It captures packets from the network and forwards them to the analysis engine for processing.
2. Event analyzer: Receives data from information sources, performs data and protocol analysis, and detects intrusion phenomena for further action.
3. Response unit: Reacts to results from the analysis engine, including terminating connections, issuing alerts, or countermeasures against attackers.
4. Event database: Stores intermediate and final data. It may be a complex database or simple text files.
Using IDS can detect intrusions before they harm the system, and leverage alarms and protection to expel intruders, thereby reducing damage during an attack. After an intrusion, IDS collects related information for knowledge base updates to improve future defenses.
IDS not only helps network administrators understand network changes in a timely manner but also guides the formulation of security policies. Upon detecting an intrusion, an IDS can respond promptly, including cutting network connections, logging events, and issuing alerts.
Key functions of an IDS include:
1. Detecting and analyzing user and system activities.
2. Auditing system configuration and vulnerabilities.
3. Assessing the integrity of critical system resources and data files.
4. Identifying known attacks.
5. Statistical analysis of anomalous behavior.
6. Auditing, tracing, and managing the operating system, and identifying user activities that violate security policies.
1.2 Classification of IDS
By detection method
1. Anomaly detection model
The anomaly detection model assumes that attacker activities deviate from normal subject activities. A baseline "activity profile" is created for normal activity, and current activity is compared against this profile. Violations of statistical norms indicate possible intrusions.
Challenges for anomaly detection include constructing accurate activity profiles and designing statistical algorithms that avoid labeling normal operations as intrusions or missing true intrusions. For example, a denial-of-service attack on a POP3 server might be implemented by submitting thousands of identical commands; countermeasures include setting thresholds for command submissions and triggering alerts when exceeded.
2. Signature-based detection model
Signature-based detection, also called misuse detection, assumes attacker activities can be represented by patterns. The system detects whether subject activities match these patterns. It can reliably detect known attack methods but is ineffective against new attack variants. The difficulty lies in designing patterns that represent intrusions without capturing normal activities. Signature detection describes known attack methods deterministically and raises an alert when audited events match known attack patterns. Its approach is similar to virus scanning and is widely applied using packet feature pattern matching.
By detection target
1. HIDS
Host-based intrusion detection systems (HIDS) are typically installed on the hosts being monitored. They analyze real-time connections and system audit logs for that host. If activities appear suspicious (by signature or statistical deviation), the IDS takes actions.
HIDS remain useful for understanding historical attack forms and choosing defenses for future attacks. HIDS can detect system events and security logs on Windows and system logs in UNIX environments. When file changes occur, the IDS compares new entries to attack markers and alerts administrators and other targets for response. HIDS has integrated other techniques over time. A common method for detecting modifications to critical system files and executables is periodic checksum checks to detect unexpected changes; detection latency depends on polling frequency. Many IDS products also monitor port activity and alert administrators on access. This approach integrates basic network-based detection methods into host-based environments.
Advantages of HIDS:
1. Cost-effective when the number of hosts is small.
2. Higher precision: It can detect activities such as access to sensitive files, directories, programs, or ports that are difficult to detect from the network.
3. Focused view: If an attacker obtains a host's credentials, a host-based agent is more likely to distinguish normal from unauthorized activity.
4. Easier to choose: Each host has its own agent, simplifying selection for users.
5. Fewer dedicated hardware platforms may be required; HIDS can operate within existing network structures, including file servers and web servers.
6. Less sensitive to network traffic: Agents typically do not lose monitoring capability due to increased network traffic.
7. Suitable for encrypted environments: Since HIDS are installed across enterprise hosts, they are better suited than network-based systems to environments where traffic is encrypted.
8. Useful for analyzing potential attack behaviors: Beyond indicating dangerous commands executed by the attacker, HIDS can identify which programs ran, which files were opened, and which system calls were made.
Disadvantages of HIDS:
1. They must be installed on the devices to be protected. For example, protecting a database server requires installing IDS on the server itself.
2. They depend on the server's logging and monitoring capabilities. If logging is not configured, reconfiguration is required, which can affect performance of production systems.
2. NIDS
Network-based intrusion detection systems (NIDS) are placed in important network segments and continuously monitor packets in those segments. They analyze each packet or suspicious packet for signatures. If a packet matches built-in rules, the IDS alerts or can even terminate network connections. NIDS do not require changes to server configurations and do not install extra software on production hosts, avoiding impact on CPU, I/O, and disk resources and preserving system performance.
Advantages of NIDS:
1. Covert operation: A network detector is less conspicuous than a host and thus less likely to be attacked. Network monitors do not run other applications or provide network services, making them more secure.
2. Wider visibility: Network-based detection can identify and stop attackers at the network edge before they connect to the network.
3. Fewer detectors needed: One detector can protect a shared segment, avoiding the need for an agent on every host, which reduces cost and administrative overhead. Special configuration is required in switched environments.
4. Harder for attackers to remove evidence: NIDS capture live network communications for real-time detection, making it difficult for attackers to remove evidence. Captured data can include attack methods and information useful for identifying attackers.
5. Operating system independence: NIDS operate independently of host OS, whereas HIDS require a specific, uncompromised OS to function and produce useful results.
6. Low resource usage on protected devices: NIDS do not consume resources on protected hosts.
Disadvantages of NIDS:
1. They can only inspect communications on the segment to which they are directly connected and cannot detect packets on different segments.
2. For performance reasons, they often rely on signature detection methods, making it difficult to detect complex attacks requiring significant computation or analysis time.
3. Handling encrypted sessions is more difficult.
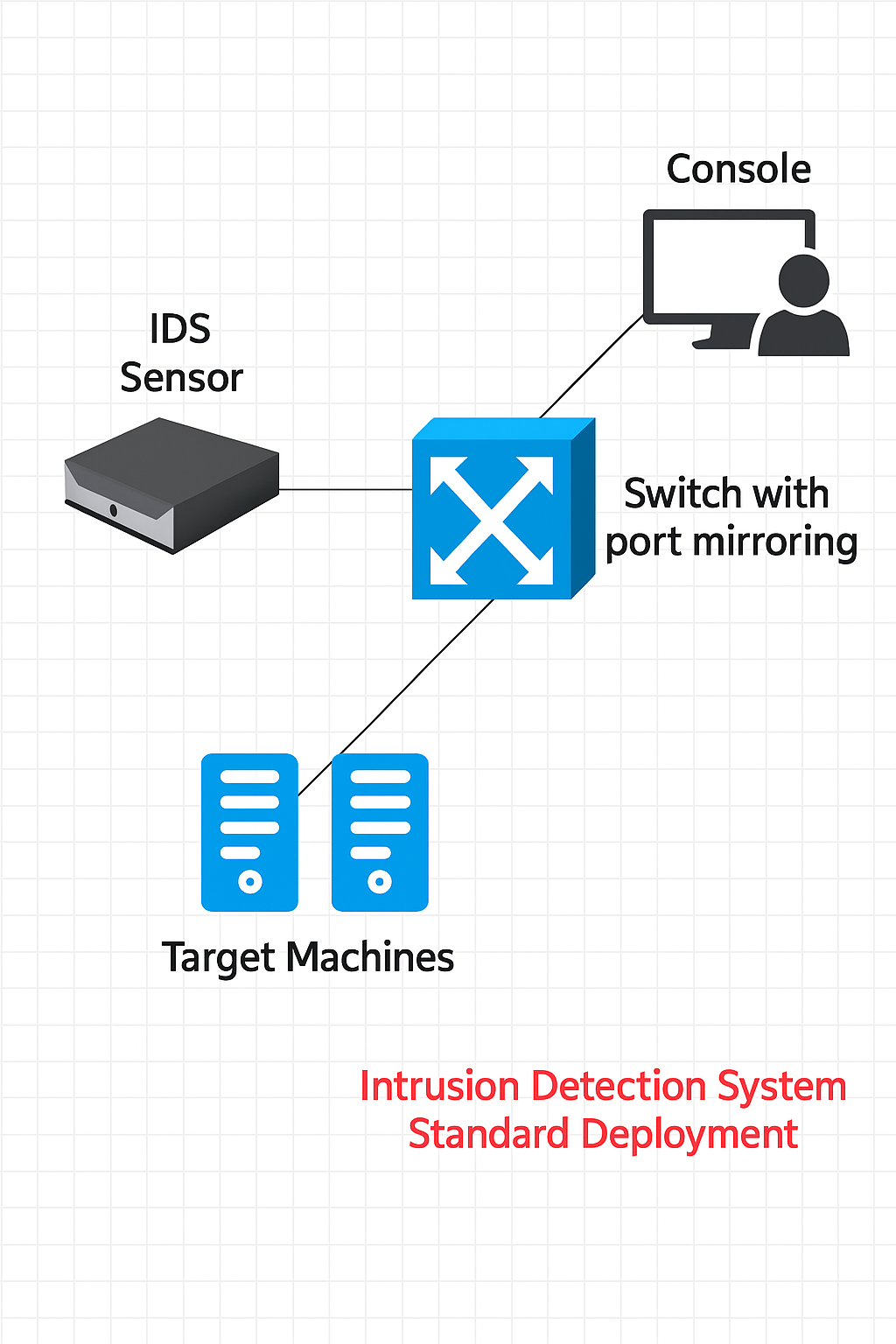
1.3 IDS Deployment
IDS products generally consist of two parts: sensors and a console.
Sensors collect data (network packets, system logs, etc.), analyze it, and generate security events.
The console provides central management; commercial products usually provide a graphical interface for the console.
Sensor placement is the main deployment decision. In switched VLAN environments, sensors can still function, but they require correct switch port configuration to capture traffic.
NIDS require sensors to operate. If sensors are placed incorrectly, IDS performance will be suboptimal. Common placement options include:
1. Inside the perimeter firewall: Sensors can detect attacks originating from the Internet. However, if the attack is a TCP-based attack that the firewall or router blocks, the IDS may not see it.
2. Outside the perimeter firewall: Sensors can detect all attacks against the protected network, including counts and types, but this exposes the sensor to attackers.
3. At major network hubs: Sensors can monitor large volumes of traffic, increasing the chance of detecting attacks and discovering unauthorized behavior relative to authorized user perimeters.
4. Within high-security subnets: For critical systems and resources, such as a corporate finance subnet, a dedicated sensor can be deployed for that segment.
2. Intrusion Prevention Systems
An intrusion prevention system (IPS) is an active system that prevents and blocks intrusions. Deployed at network ingress and egress points, an IPS drops attack packets or blocks attack sources when it detects attack attempts. IPS detection functions are similar to IDS, but IPS takes action to stop attacks once detected. IPS can be seen as a development built on IDS. Real-time detection and proactive prevention are the core design principles that distinguish IPS from firewalls and IDS.
2.1 Main Technical Advantages of IPS
1. Inline deployment
IPS retains IDS-style real-time detection but uses a firewall-like inline installation. It sits directly in the traffic path, receiving external traffic on one port, inspecting it for anomalies or suspicious content, and forwarding it to internal systems via another port if cleared.
2. Real-time blocking
IPS has robust real-time blocking capabilities, intercepting intrusive activity and malicious network traffic in advance to prevent damage.
3. Advanced detection techniques
IPS uses parallel processing for detection and protocol reassembly analysis. Parallel processing means all packets passing through the IPS are matched against filters in parallel, traversing all packet filters within a single clock cycle. Protocol reassembly analysis performs hardware-level preprocessing to reconstruct packets and determine the application protocol. Based on the protocol characteristics and attack vectors, IPS filters the reconstructed packets and compares suspicious items against a signature database to improve detection quality and efficiency.
4. Custom rule injection
IPS allows custom rules to block malicious code. It can enforce acceptable-use policies, such as blocking peer-to-peer file sharing or high-bandwidth free VoIP tools.
5. Self-learning and adaptive capabilities
To address evolving attack techniques, modern IPS incorporate self-learning and adaptive features that analyze the network environment and intrusion context to extract new attack signatures and update the signature database. The IPS can automatically summarize experience and create new defense strategies. When a new attack is discovered, the IPS generates a new filter to block it.
Because IPS is inline with communication lines, it combines IDS detection functions with the ability to terminate network intrusions in real time. IPS consists of detection and defense systems and provides defenses from network to host with predefined response settings.
2.2 Classification of IPS
From the perspective of protection targets, IPS can be classified into three types:
1. Host-based intrusion prevention (HIPS): Protects servers and hosts from attacks and operator errors.
2. Network-based intrusion prevention (NIPS): Protects the network by inspecting traffic and blocking sessions identified as intrusions.
3. Application intrusion prevention (AIP): Extends host-based protection to a network device placed in front of application servers.
In the ISO/OSI model, firewalls primarily operate at layers 2 to 4, with limited capability at layers 4 to 7. Antivirus software mainly operates at layers 5 to 7. To fill the gap between firewalls and antivirus at layers 4 to 5, IDS was introduced. IDS notifies administrators or firewalls after discovering anomalies, but damage may already have occurred. Defensive measures are most effective if they act before harm is realized. Intrusion response systems (IRS) supplement IDS by responding rapidly when an intrusion is detected and automatically applying blocking measures. IPS emerged as a further development that incorporates strengths from both IDS and IRS.
3. Relationship Among IDS, IRS, and IPS
Intrusion Detection System (IDS): Detects and alerts on anomalous or potentially intrusive data, informs operators of the network status, and provides guidance for remediation. IDS emphasizes risk management.
Intrusion Response System (IRS): Inspects network data to find known attack code signatures, filters harmful data flows, drops malicious packets, and logs events for post-event analysis. IRS considers application and transport anomalies to assist in identifying intrusions. The purpose is to identify attack programs or malicious code and prevent intrusions proactively.
Intrusion Prevention System (IPS): Detects and defends against behaviors that are clearly identified as attacks and harmful to networks or data. IPS reduces the resource burden on operators for handling anomalies and focuses on risk control. IPS can be viewed as a derivative that combines IDS and IRS functions.