1.0 Introduction
Compared with wired communication, wireless communication has become a significant option in process measurement, control, and manufacturing. Advances in short-range wireless technologies have created opportunities to connect field devices to central stations. Process measurement, control, and communication are steadily moving toward wireless strategies as initial limitations are being addressed and systems become more robust and reliable. For any control system to be networked wirelessly, factors that must be considered include reliability, scalability, mixed real-time data transport, availability, security, and coexistence with other networks. Other issues to consider include sensor type, placement, power consumption, local data processing, and timestamping.
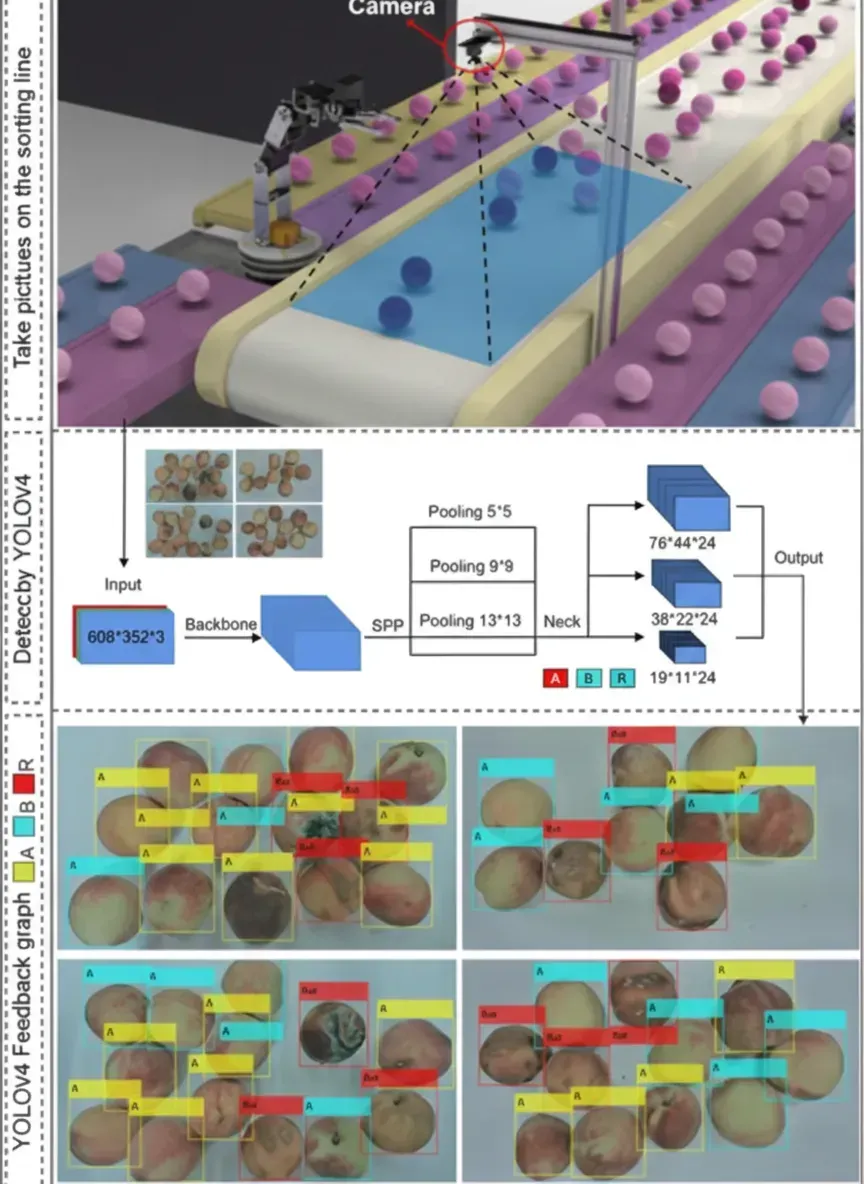
Because cable installation can require large investment, sending data wirelessly is often used to avoid those costs. Each field sensor appears as a node. Before data are sent to a receiver or gateway via multihop communications under a defined protocol, networked sensors perform local acquisition, computation, and data processing. Sensor nodes act like transceivers: they originate data and route data. Local data processing reduces load on the transmission medium.
A typical sensor network layout consists of sensor nodes, receivers or gateways, internet/satellite links, and an application manager before data reach the end user.
Wireless networks may be configured as personal area networks (PAN), local area networks (LAN), metropolitan area networks (MAN), wide area networks (WAN), or global area networks (GAN).
2.0 Wired vs Wireless
Wired networks face many difficulties, such as expensive cabling, difficulty expanding and adding loose connections, high maintenance costs, and susceptibility to surge damage.
Wireless networks are easier to scale and can reduce coverage blind spots. However, wireless deployments face concerns including reliability, security, signal interference, and eavesdropping.
3.0 ISM Bands
Wireless sensor networks use unlicensed ISM (industrial, scientific, and medical) frequency bands. Common ISM ranges include 902–928 MHz, 2.4–2.835 GHz, and 5.725–5.85 GHz. Historically, ISM bands were also used for RF heating and microwave ovens.
When two or more wireless devices operate adjacent in the same band, electromagnetic emissions from one device can affect the other. Network designs must ensure this does not happen. Wireless networks are increasingly used in many domains, such as wireless LANs, Bluetooth and near-field devices, and cordless phones.
4.0 Wireless Standards
Different wireless protocols are used to meet different needs and applications. Examples include IEEE 802.11, IEEE 802.15, and IEEE 802.16, each with variants for specific use cases. The choice depends on application requirements.
Wi-Fi, based on IEEE 802.11, is a LAN technology sometimes called wireless Ethernet. WiMAX is based on IEEE 802.16. Wi-Fi uses carrier sense multiple access with collision avoidance (CSMA/CA) as its MAC protocol and operates as a half-duplex shared medium. WiMAX can be advantageous for sensor networks because of greater coverage and capacity; it commonly uses full-duplex transmission with a request/grant mechanism that assumes separate channels for uplink and downlink.
Bluetooth is a low-power, short-range wireless protocol based on IEEE 802.15.1 and uses frequency hopping to reduce interference and fading. Bluetooth employs a time-division duplex time-division multiple access (TDD-TDMA) scheme with separate hops for two-way communication; it is half duplex and cannot guarantee end-to-end latency.
ZigBee, like Bluetooth, uses PAN technology and targets ultra-low power monitoring applications. It is based on IEEE 802.15.4 at the physical and MAC layers and provides low power, low cost, and low data-rate communications. ZigBee uses direct-sequence spread spectrum (DSSS). It lacks frequency and path diversity and therefore provides limited resistance to interference and obstacles; as a result, its use in industrial environments is limited.
WirelessHART, based on IEEE 802.15.4, is backward compatible with existing HART devices and uses the 2.4 GHz ISM band. It is a standard protocol for automation and control applications. WirelessHART uses TDMA with a 250 kbit/s data rate and supports channel hopping with 5 MHz separation between adjacent channels. It provides security at the MAC and network layers using 128-bit AES. Frequency diversity, path diversity, and appropriate messaging methods improve network reliability when WirelessHART is used.
ISA100.11a, like WirelessHART, is based on IEEE 802.15.4 and uses the unlicensed 2.4 GHz ISM band. It is not backward compatible with HART. Features include low cost, low complexity, low power consumption, RF interference resistance, interoperability, and scalability. It supports star and mesh topologies and provides message protection using 128-bit AES with asymmetric encryption. ISA100.11a uses time-division multiple access to allow routers to sleep, reducing power consumption.
5.0 Node Architecture
A sensor node consists of a sensing unit, processing unit, power unit, and communication unit.
The sensing unit may include one or more sensors that measure physical parameters such as temperature and pressure. An ADC converts analog sensor outputs into digital signals for the processing unit.
The processing unit receives ADC data and interfaces with the wireless physical layer, managing network protocols. Software running on this unit also reduces power consumption across the radio, sensors, signal conditioning, and communications. The processor is selected based on data rate, processing speed, memory, and peripheral requirements.
The communication unit includes a common transceiver that connects the node to the network. It is used to transmit and receive data between nodes and base stations. Typical radio states are transmit, receive, idle, and sleep.
Sensor networks are typically not powered by grid infrastructure; nodes use batteries or solar power depending on the environment.
Sensor nodes perform data acquisition. The processing unit handles analysis, aggregation, compression, and fusion. Other blocks manage data coordination and configuration within the node.
6.0 Sensor Network Structure
A sensor network includes remote sensors, aggregator or intermediate processing nodes, and end processing nodes. Sensors support single-hop and multihop connections. The whole set is called the sensor domain.
Accurate sensor placement and timestamping are crucial for reliable operation. Nodes communicate with receivers. Nodes often include GPS positioning capability, collect and analyze data, compress results, and route data to receivers.
Data are collected at base stations, so nodes closer to a base station typically carry a heavier data burden. A suitable routing mechanism mitigates this load imbalance.
7.0 Characteristics of Wireless Sensor Networks
Wireless sensor networks are scalable and use unlicensed ISM bands. They are infrastructure-less, peer-to-multipoint networks where topology changes frequently and data collection is typically many-to-one at base stations. Node density may vary. Nodes are power-constrained and self-configuring, and are robust to nodes joining and leaving. Data from groups of nodes are aggregated to reduce the number of transmissions required.
8.0 Challenges
Because sensor nodes have very limited energy, communication protocols for these networks must be highly energy efficient. Protocols for wireless sensor networks therefore prioritize power consumption and efficiency, while traditional protocols focus on throughput and latency.
Node deployment is another critical factor for protocol design. Random deployment requires self-organizing protocols so nodes can collaborate and adapt to failures without human intervention. Most sensor deployments are unattended, so nodes must support autonomous repair, maintenance, and adaptation to new environments. These self-management features must be designed and implemented so nodes can operate consistently.
9.0 Limitations When Connecting to the Internet
Energy and memory efficiency are key performance metrics for sensor networks, unlike many conventional network protocols. To achieve seamless integration with the Internet, sensor network designs require significant modification.
Different wireless network architectures, such as cognitive radio networks, mesh networks, and wireless sensor networks, require interoperability for Internet integration. Cross-layer, location- and spectrum-aware communication protocols and heterogeneous network management tools are important for seamless integration. The 6LoWPAN standard was developed to integrate IPv6 with low-power sensor nodes by compressing IPv6 headers for sensor networks. Coexistence at the MAC layer is a major challenge because sensor networks and WLANs often operate in the same spectrum.
Other issues to address include: (a) end-to-end routing or connectivity between sensor nodes and the Internet, and (b) incompatibility between existing transport-layer solutions in sensor networks and widely used Internet transport protocols such as TCP and UDP. Transport protocols for sensor networks should be designed to reliably deliver sensor data and event information end to end.
10.0 Topologies
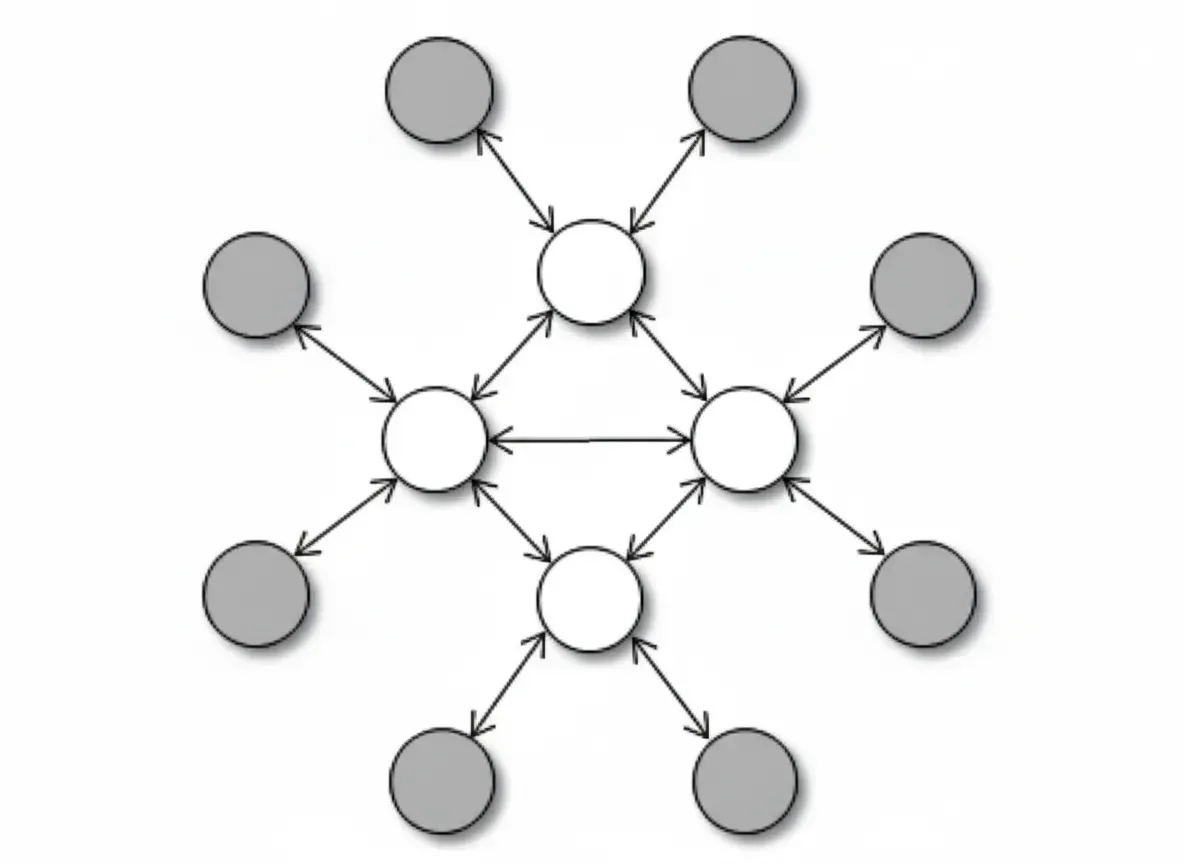
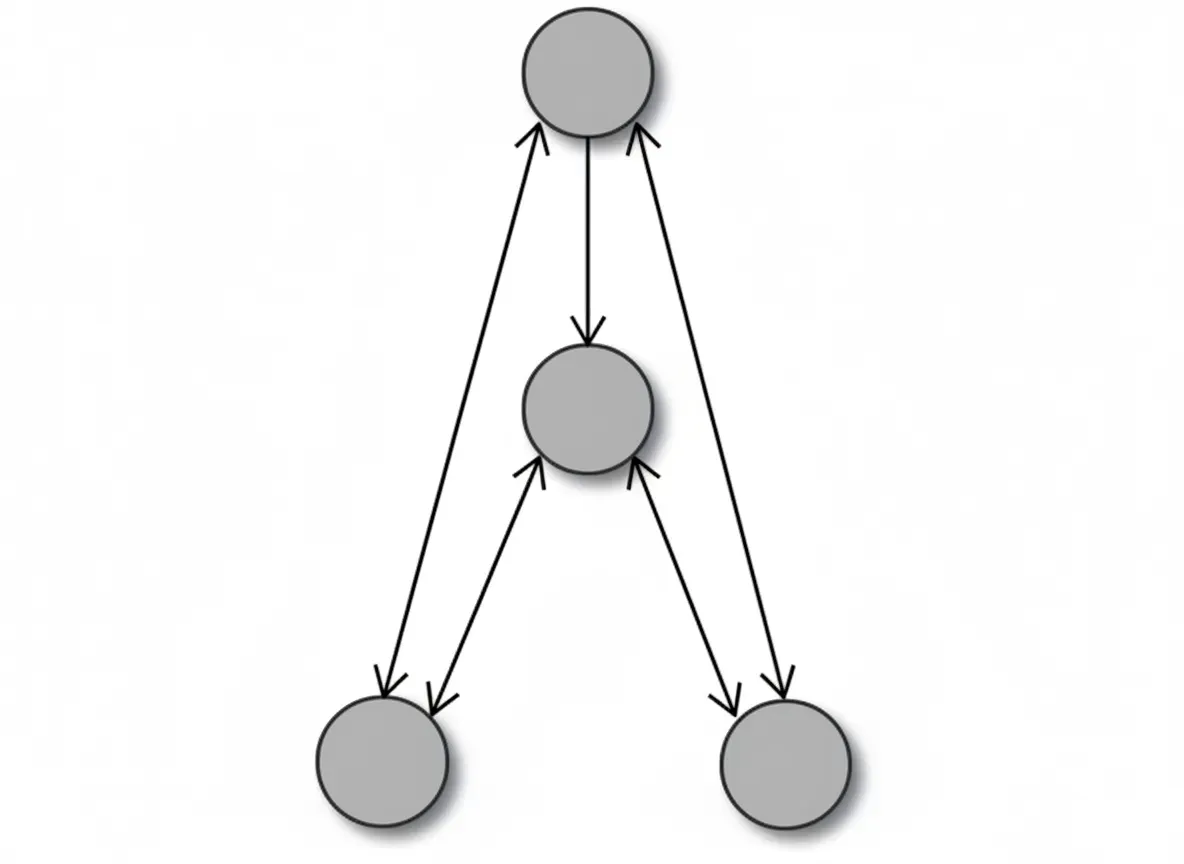
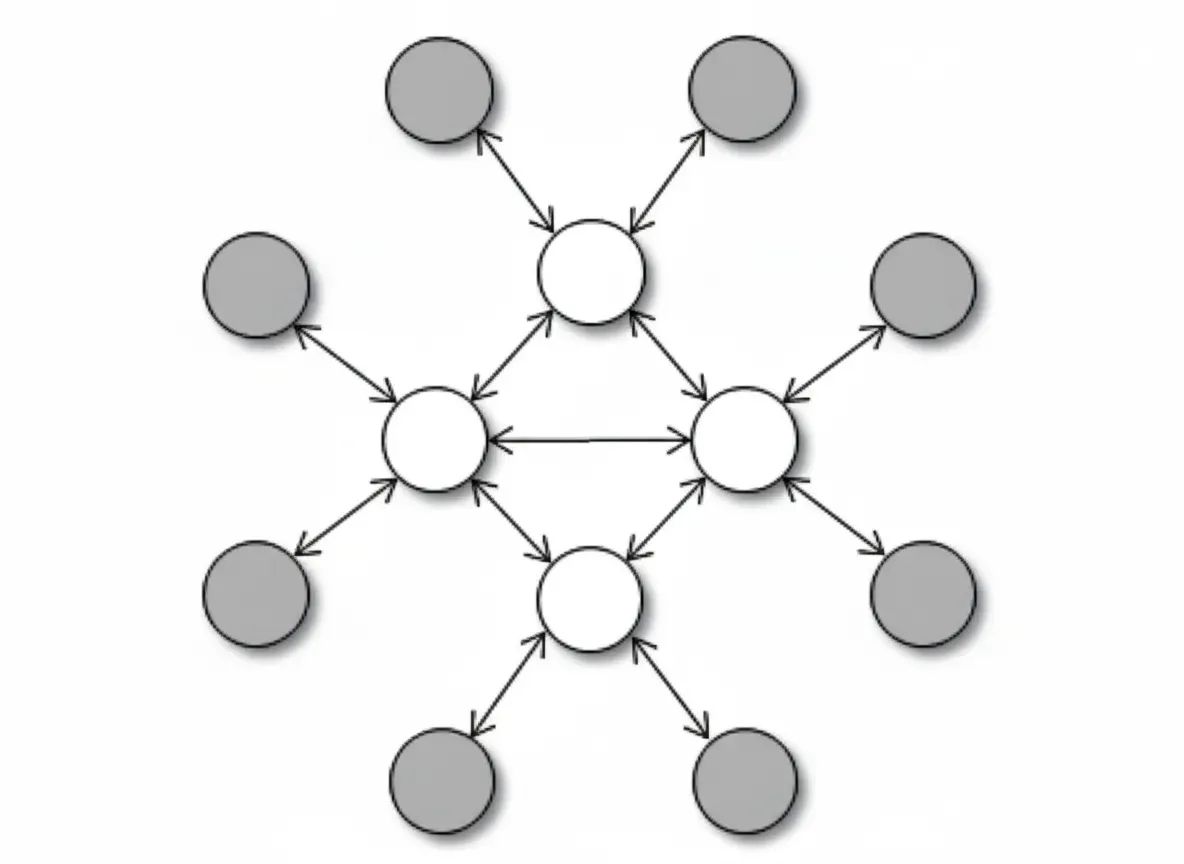
The arrangement of sensor nodes and their interconnections define the network topology. Common topologies for wireless networks include star (point-to-multipoint), mesh, and hybrid star-mesh.
Star network:
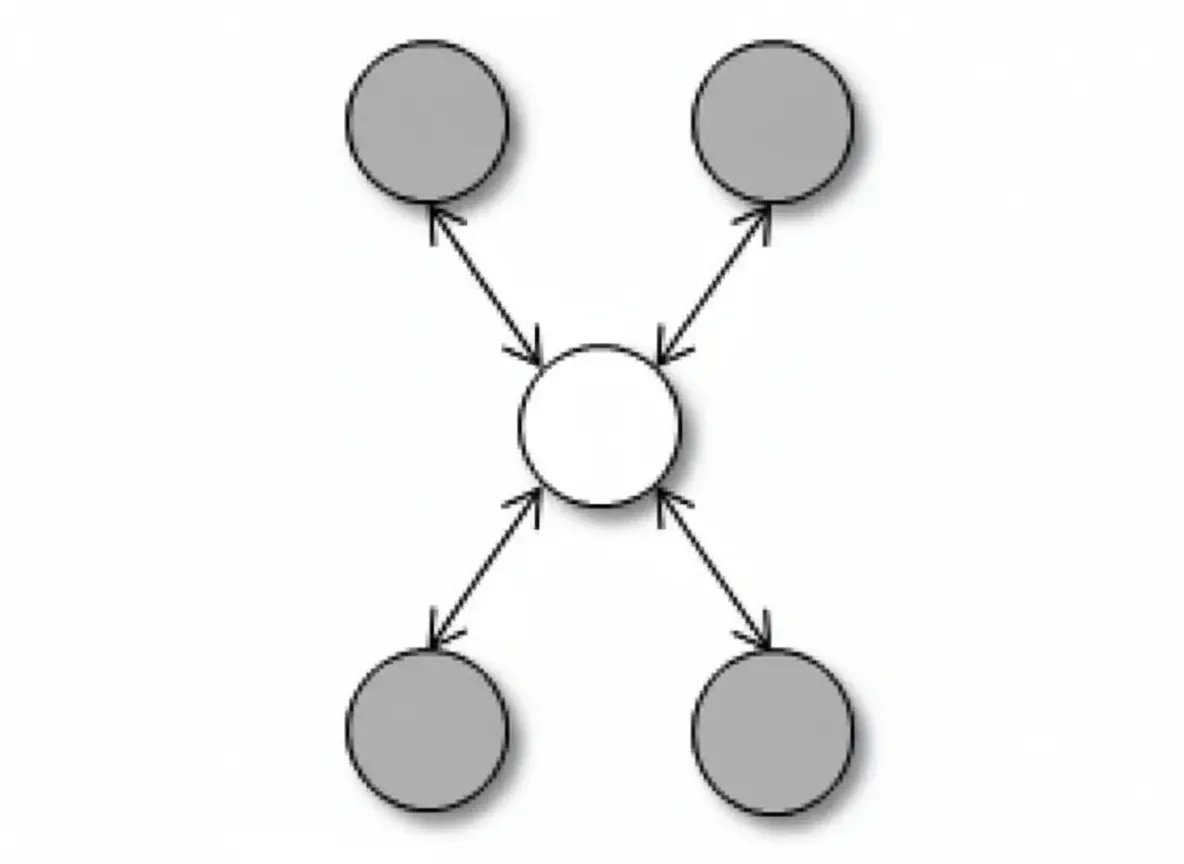
In a star network, the base station sends and receives data from remote nodes. Remote nodes cannot send data directly to other remote nodes, so end-to-end communication between nodes is not possible. Advantages include simplicity, speed, and minimized energy consumption for remote nodes. However, the base station must be within radio range of all connected nodes, and if the base station fails, that portion of the network goes offline.
Mesh network:
Mesh topologies are used when sensors are deployed over large geographic areas with high redundancy. Because wireless sensor networks are self-configuring, a node that fails will be bypassed and the network will determine alternative routes. This topology offers redundancy and scalability.
When a node needs to send data beyond its radio range, it forwards data to a neighboring node within range; the data is passed hop-by-hop until it reaches the destination. This multihop communication consumes more battery power at intermediate nodes, limiting their lifetime. Another disadvantage of multihop communication is increased message latency as hop count grows.
Multihop communication shortens single-hop coverage distance. Since path loss increases nonlinearly with distance, received signal quality at the receiver can be maintained.
Hybrid star-mesh topology combines advantages of star and mesh networks, offering low energy consumption for end nodes and self-healing capabilities for the network.
11.0 Coexistence Issues
When multiple adjacent wireless channels transmit simultaneously, RF interference can prevent correct reception. Coexistence is defined as a system's ability to perform its tasks in an environment where other systems can also perform their tasks, possibly under different rules. For example, IEEE 802.15.4 and IEEE 802.11b/g both use the 2.4 GHz unlicensed band. If both protocols operate in adjacent areas, RF interference may affect both. Reducing such interference improves reception quality. Collisions or overlaps in time or frequency domains worsen the issue when energy is sufficient in both messages.
Techniques used to mitigate interference include time diversity, frequency diversity, power diversity, coding diversity, spatial diversity, blacklisting, and channel assessment.
The figure below compares 802.15.4 and 802.11b/g responses in the 2.4 GHz ISM band. 802.15.4 has 16 channels, while 802.11b/g has 3 non-overlapping channels. Certain 802.15.4 channels are less affected by 802.11b/g transmissions. WirelessHART reduces interference by using pseudo-random channel-hopping sequences and avoiding overlapping channels.
WirelessHART uses TDMA to transmit one message per frequency channel at any given time to avoid collisions. A WirelessHART network can be configured to avoid channels commonly used by other networks, reducing collisions and interference. The network listens before initializing transmissions and schedules future time slots for retransmission if a channel is busy.
DSSS spreads the message across the chosen channel bandwidth to reduce interference under coding diversity. Spatial diversity is achieved via mesh networks where original messages may traverse different paths to a gateway depending on traffic load and node availability.
12.0 Comparison: Conventional Fieldbus vs Wireless Architectures
Conventional fieldbus systems and wireless sensor network architectures differ significantly. The main advantage of wireless networks is the elimination of wired connections common in other systems, which can reduce maintenance and labor. Wireless systems must address eavesdropping and RF interference from neighboring channels and must maintain connectivity for both static and mobile sensors.
13.0 Protocols for Wireless Sensor Networks
Wired networks communicate over guided media, while wireless networks transmit electromagnetic signals through the air. Sensor nodes must self-organize to support multihop communication. To improve efficiency, nodes must share resources effectively, which depends on an efficient MAC layer that determines overall network performance.
The protocol stack used by sensor nodes and receivers includes physical, MAC, network, transport, and application layers.
Because networks can include many nodes, MAC protocols must ensure a node can access the transmission medium when needed. The data link layer is split into two sublayers: logical link control (LLC) and MAC. LLC adapts logical functions for medium access and supports multiple MAC variants. Different MAC variants are chosen based on node topology, required quality of service, and channel characteristics.
MAC functions include: (a) regulating access to a shared medium, (b) adding address headers and error-detection trailers to data streams, and (c) on reception, stripping these fields and validating addresses and data integrity. Exchanging control information among nodes to decide channel access increases MAC complexity and overhead.
Protocol performance depends on throughput, delay, robustness, stability, scalability, fairness, and energy efficiency. Higher throughput reduces delivery delay. Robustness refers to tolerance to errors and faulty information. Stability is the ability to handle traffic fluctuations reliably over time. Scalability means maintaining performance as the network grows. Fairness is equitable sharing of channel capacity without reducing throughput. Energy efficiency is critical, particularly for geographically dispersed networks. Causes of low energy efficiency include collisions, control packet overhead, idle listening, and mode switching.
MAC protocol choices include fixed allocation, on-demand allocation, random access, flooding, and gossip protocols. These aim to balance reasonable resource allocation with protocol overhead.
14.0 Security
Resource-constrained sensor nodes are vulnerable to external attacks such as eavesdropping, data manipulation, and node impersonation. Providing security per node in large-scale deployments is challenging, as is handling rapid node addition or removal.
Cryptography secures data between sender and receiver. Encryption converts plaintext into ciphertext at the sender; decryption restores plaintext at the receiver. Encryption requires algorithms and keys. Algorithms need not be secret, but keys must be kept confidential. Symmetric cryptosystems use a single key for encryption and decryption, while asymmetric systems use different keys. Cryptography provides data integrity, confidentiality, and authentication of devices and messages. The security of any cryptosystem depends on key strength rather than algorithm secrecy.
Security services also include authentication, access control, scalability, and data freshness. Authentication verifies resource users' authorization. Access control restricts resource access. Scalability allows adding nodes without degrading security. Data freshness ensures messages are recent and not replayed or out of order.
An effective key management scheme (KMS) is essential to counter data security threats. KMS is critical when nodes join or leave the network to maintain a secure environment.
Security goals for sensor networks include confidentiality, integrity, authentication, and availability. Confidentiality protects messages from eavesdropping as they hop from node to node. Integrity ensures messages are not altered in transit. Authentication confirms message origin. Availability ensures the network remains accessible for message delivery.
Data freshness is a significant security concern, especially when WSN nodes use shared keys. Attackers can perform replay attacks using old keys if new keys are being refreshed across the network. Adding a nonce or timestamp to each packet helps guarantee freshness.