What is a firewall
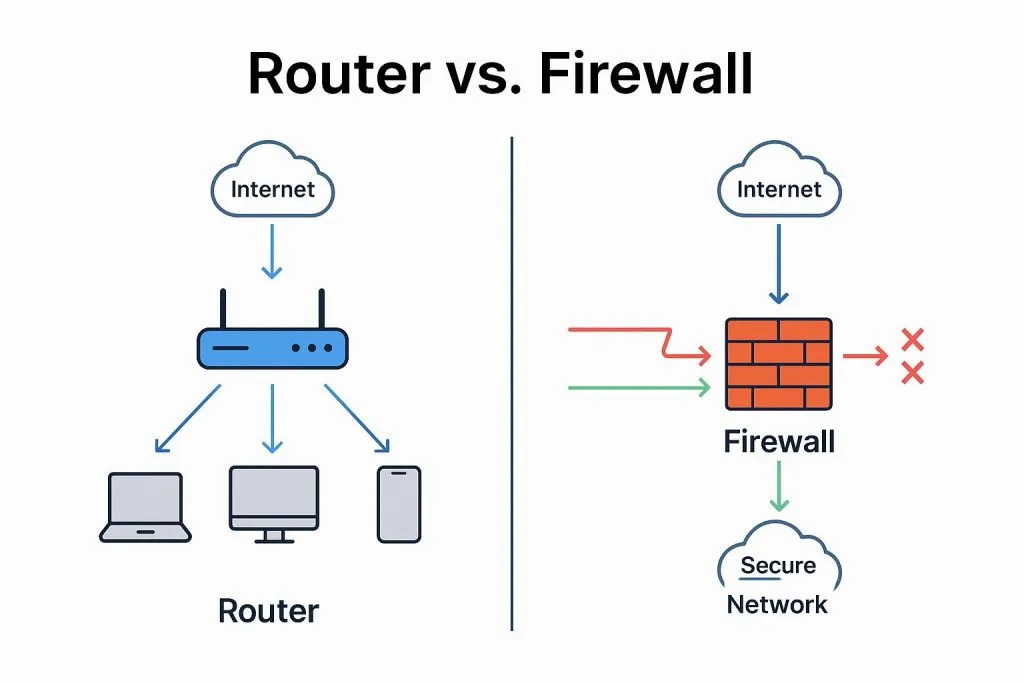
A firewall is a network security device or software that monitors and controls network traffic to protect networks from unauthorized access, malicious attacks, data leakage, and other threats.
Firewalls enforce rules and policies to filter and inspect packets entering or leaving a network, deciding whether to allow those packets based on predefined security rules. They can inspect and filter traffic at multiple network layers, such as the network layer, transport layer, and application layer.
Key functions
- Access control: Selectively allow or block traffic from specific IP addresses, ports, or protocols at the network boundary based on configured rules and policies.
- Packet filtering: Inspect incoming and outgoing packets and filter them according to source address, destination address, port number, protocol, and other attributes to block potential threats or unauthorized access.
- Network address translation (NAT): Translate internal private IP addresses to public IP addresses to improve security and privacy.
- VPN support: Establish virtual private network (VPN) connections to provide secure remote access and data transfer, protecting sensitive information from unauthorized access.
- Event logging and alerting: Record network activity and security events, and generate alerts or logs so administrators can monitor and respond to potential threats.
In summary, a firewall plays an important role in protecting networks from threats and unauthorized access, helping to maintain confidentiality, integrity, and availability.
Main firewall technologies
Firewalls use a variety of technologies to achieve network security objectives. Common firewall technologies include:
- Packet filtering: The most basic firewall technology, which filters packets based on source IP, destination IP, port number, protocol, and related attributes.
- Stateful inspection: Builds on packet filtering by tracking the state of network connections, allowing return traffic that matches an established legitimate connection while blocking unsolicited connections.
- Application proxy: Acts as a proxy between clients and servers, inspecting application-layer data and performing analysis and control on bidirectional transfers to provide finer-grained filtering.
- Network address translation (NAT): Maps internal private IP addresses to public IP addresses, hiding internal IP information and reducing exposure to external attacks.
- Virtual private network (VPN): Uses encryption and authentication to create secure remote access connections so remote users can safely connect to internal networks over public infrastructure.
- IDS/IPS integration: Integrates intrusion detection and intrusion prevention systems to monitor traffic and events in real time and identify and block potential malicious activity.
- Content filtering: Filters packets based on content, keywords, or specific protocols to block access to or transmission of certain content types, such as spam or malware.
- Virtual segmentation: Divides the network into multiple virtual zones, each with its own security policies and rules, to limit access between different parts of the network.