Introduction
If you are reading this, your daily work and life likely depend on various digital systems. Many processes run around the clock to keep these systems operating smoothly. At the same time, attackers are attempting to disrupt, penetrate, or control these systems.
No network is 100% secure, and attackers are using graph-like thinking in their campaigns.
Detection Challenges and Impact
Research from the Ponemon Institute found that 66% of small and medium-sized businesses experienced a cyberattack in the past year. The goal of cybersecurity is to stop as many attacks as possible, but some attacks are difficult to detect quickly with traditional solutions.
Rapidly discovering vulnerabilities is critical to minimizing losses, including financial, operational, and reputational damage.
However, organizations still detect and stop attacks relatively slowly. How long does it take to detect an attack? There is no single answer. In some cases, it can take hundreds of days to detect a breach. Unfortunately, when organizations realize they have been attacked by hackers, it is often too late and the damage has already occurred. According to authoritative sources, the average cost of a data breach in 2023 reached $5 million.
Gartner predicts that by 2026, 50% of C-level executives will have risk-related performance requirements in their employment contracts.
Attack Patterns and Modeling
CAPEC (Common Attack Pattern Enumeration and Classification), established by the U.S. Department of Homeland Security, defines more than 500 attack patterns. Examples include Abuse Existing Functionality, Collect and Analyze Information, and Inject Unexpected Items. Understanding these patterns is important for analysts, developers, and IT architects when building effective security systems.
Graph-based analysis can be used to model and search for these patterns.
Why Graphs Fit Security Use Cases
Graphs represent interconnected data. To detect or stop attacks, it is necessary to identify patterns and trace them upstream to their sources and downstream to the affected resources. These patterns can be long, wide, or both, since many events may occur concurrently. In the example below, an alert is traced back to login events and the IP address that originally triggered the alert. Note that successful tracing often requires traversing multiple hops. A graph database can perform these traversals in seconds, while relational databases may take minutes or hours.

Figure 1. Linear trace path for alert activity
Attacks are often carried out by a relatively small number of actors. A DDoS flood, for example, may involve a few IP addresses or user IDs sending large numbers of requests to a target server, causing congestion or denial of service for legitimate users.
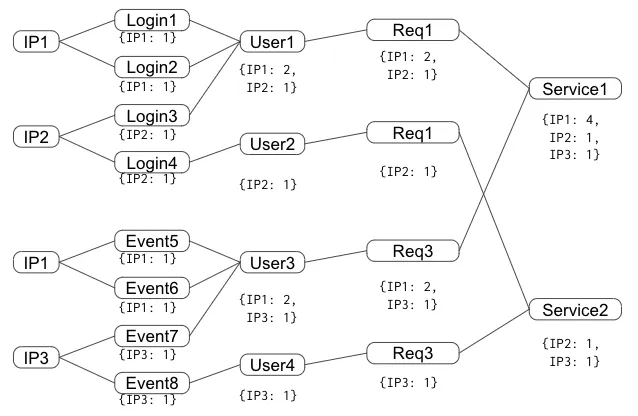
Figure 2. Tracing IPs, events, and users that requested a specific server
Data Integration and Real-Time Analysis
A graph platform can integrate multiple data sources and process them in real time: information from different microservices, user profiles, and authorization systems must be considered together to understand activity, trace events, and disrupt attackers.
Platform Capabilities for Threat Detection
As a native graph database with deep link analysis and in-database machine learning, a graph platform can offer performance advantages compared with typical security information and event management (SIEM) solutions. Organizations can apply graph tools to the right datasets to more quickly identify anomalous behavior, unusual transactions, and various types of malicious activity within the network.