Overview
The security landscape is continually changing. As attackers adopt AI technology to refine attack methods and bypass traditional defenses, defenders must deploy smarter, faster, and more creative threat detection and response techniques to protect organizations from internal and external attacks. Integrating traditional security tools with emerging technologies is one approach CISOs are adopting to address these challenges.
VentureBeat identified 10 proven innovative security technologies based on surveys and interviews with enterprise users. These technologies can help organizations address attacks, eliminate vulnerabilities, and reduce risk during digital transformation.
1. Zero Trust Network Access (ZTNA)
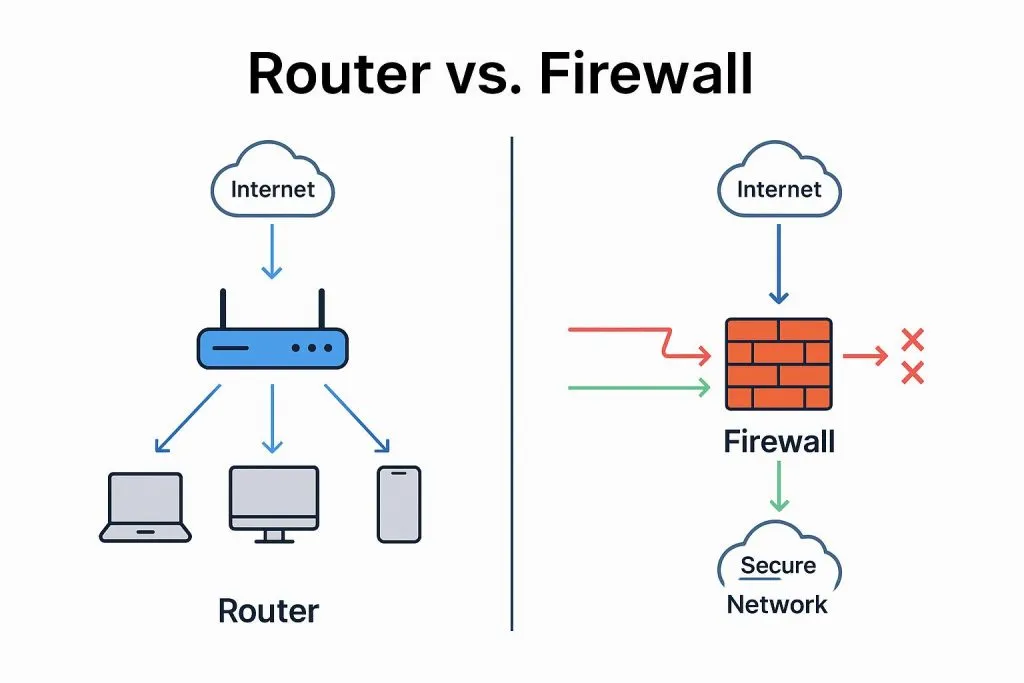
With the growth of cloud computing, virtualization, IoT, BYOD, and remote work, device counts have surged and network perimeters have become blurred. ZTNA applies zero trust principles in practice. Deployed ZTNA extends protections beyond traditional proxy, network access control, and firewall mechanisms and continuously monitors whether workstations and nodes comply with established security policies. Scalability is a key differentiator for ZTNA versus traditional models. Gartner cites hybrid work as a major driver for ZTNA adoption and its integration into security service edge (SSE). Zero trust policies restrict access to authorized applications only, reducing the remote-access attack surface.
2. Extended Detection and Response (XDR)
According to Gartner, XDR is a unified threat detection and incident response platform that integrates multiple security capabilities into a single operations system. It consolidates heterogeneous telemetry from cloud, network, and endpoints into a data lake to detect advanced threats, triage incidents, and trace intrusion paths for closed-loop security operations. XDR focuses on detection and response using primary telemetry aggregation and analysis and supports automated, rapid responses by integrating with third-party components. XDR helps organizations improve detection and response against evolving attacks.
3. Identity Threat Detection and Response (ITDR)
Digital identity protection is systemic, and overall security depends on the weakest link. Organizations should combine endpoint defenses, real-time incident response, zero trust infrastructure, and domain protection to build stronger identity management. Gartner introduced Identity Threat Detection and Response (ITDR) to fill gaps in identity threat monitoring and response. ITDR enhances existing identity management and complements EDR, NDR, and XDR solutions.
4. Mobile Threat Defense (MTD)
MTD is a prevention-first approach that assumes moving targets are harder to hit. It shifts or obfuscates application access points through dynamic or static rearrangement, mutation, or other techniques to divert attacks. MTD can also set traps to capture attacker behavior and inform future defenses. MTD has demonstrated effectiveness against ransomware and advanced zero-day attacks and can strengthen the security of memory, network, applications, and operating systems. Organizations can use MTD to implement proactive defenses.
5. Microsegmentation
Microsegmentation limits lateral movement within an environment by dividing networks or clouds into smaller isolated segments. It is widely regarded as a best practice to counter internal spread of attacks. By separating workloads by identity, microsegmentation prevents unauthorized workload communication during an incident. Practical deployments have reduced the scope of unauthorized communications and attacks, making microsegmentation a key component in future security and zero trust architectures.
6. Secure Access Service Edge (SASE)
SASE is an architecture designed to provide secure network access, application protection, and data security. It combines SD-WAN, cloud security, and network security technologies to deliver secure, reliable access at the enterprise edge. Gartner views SASE as a natural security architecture for cloud- and service-based enterprise networks. It enables organizations to meet business needs with secure, efficient, and flexible access. Gartner also forecasts increasing SASE adoption for remote access across enterprises by 2025.
7. Security Service Edge (SSE)
SSE is a SASE variation that focuses on securing SaaS, web, and private applications by integrating secure web gateway (SWG), cloud access security broker (CASB), and ZTNA into a single cloud platform. SSE may be more suitable for some small and midsize organizations that do not require or cannot deploy the full SASE stack.
8. Endpoint Detection and Response (EDR)
EDR emerged as threats evolved and endpoints became primary targets. Traditional defenses often miss sophisticated attacker techniques. EDR uses threat intelligence, machine learning, and behavior analysis to detect and respond to endpoint threats, providing comprehensive, sensitive, and intelligent defense. EDR gives organizations better visibility into endpoint status and helps identify and respond to complex threats.
9. Endpoint Protection Platform (EPP)
EPP complements EDR with stronger management and control of endpoint systems. As organizations modernize their stacks for integration and scalability, EPP is seen as an essential tool. EPP platforms employing advanced artificial intelligence and machine learning can block intrusions before malicious activity penetrates the network. With improved data analytics, EPP is becoming more data-driven, offering better endpoint visibility and control.
10. Unified Endpoint Security (UES)
UES consolidates EPP, EDR, and MTD capabilities into a single console and platform, simplifying management and providing a clearer security posture. By unifying previously siloed endpoint technologies, UES reduces complexity for protecting each endpoint device, including PCs, mobile devices, and servers. Some CISOs report that UES is their preferred endpoint security model, particularly during mergers and acquisitions.