Overview
In information systems and software development, the role of test servers is indispensable. Test servers are environments designed for experiments, verifying new features, and testing software updates without threatening the stability and continuity of the primary operating system.
However, the nature and use of these test servers inherently introduce a range of information security risks. This article examines core cybersecurity issues related to test server operation and outlines potential countermeasures and protective strategies.
Core Issues
A common misconception among developers and IT professionals is that test servers are an insignificant component within a large organization's infrastructure. As a result, there is often a degree of neglect regarding their security, based on the belief that any attack, compromise, or failure will not affect primary infrastructure operations.
At the same time, information security teams often deprioritize test server security compared with production infrastructure, which typically benefits from stronger technical and organizational protections.
Despite this dismissive attitude, test servers frequently handle sensitive data during testing and debugging. Such data may include production infrastructure configuration elements or personal data from customers or employees. This creates a precarious situation in which developers use sensitive data in an environment with minimal controls and supervision, while security teams may lack the necessary resources and technical measures to secure that process. In this context, incidents become a question of when, not if.
Pressure Points and Mitigations
Test servers are often configured for ease of use, which unintentionally leads to classic security issues such as weak passwords and insufficient access restrictions. While these configurations may simplify developers' workflows, they can significantly weaken overall information security. Common issues related to test server security include:
- Data sensitivity. Organizations often neglect the need to obfuscate or mask data used for testing. It is also common for credentials on test infrastructure to remain unchanged for long periods.
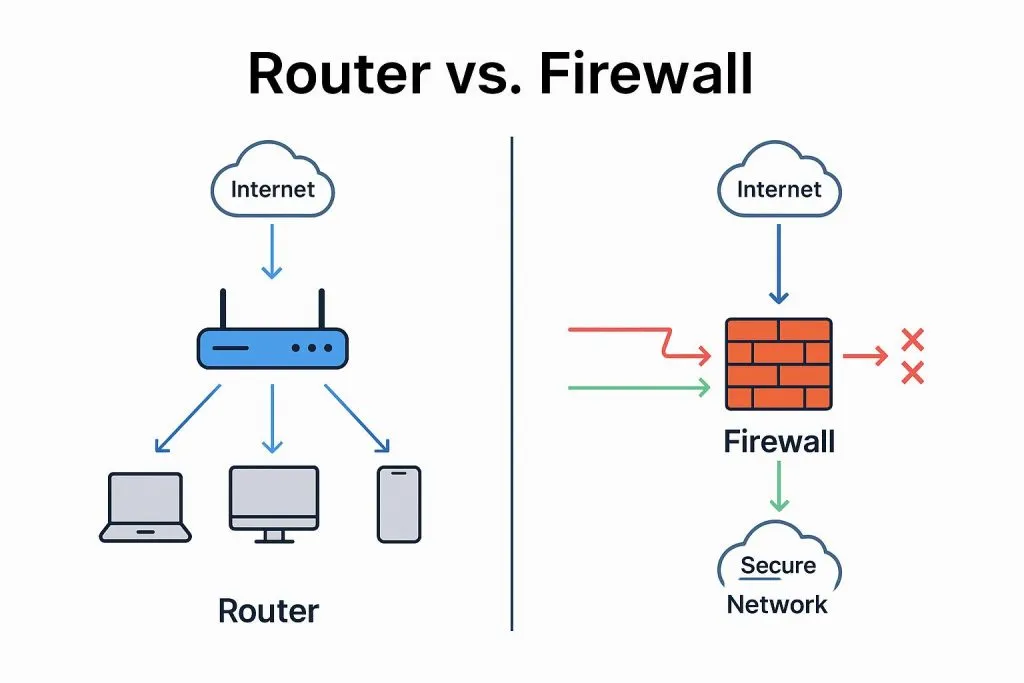
- Protection level. Production servers generally have stronger protections such as firewalls, intrusion detection, and intrusion prevention systems. By contrast, test servers used to simplify operations and testing often lack these protections and may reside on separate network infrastructure with a lower security posture.
- Access control. On test servers, users frequently have the same elevated privileges, which increases the risk of compromise due to weak or reused passwords.
- Vulnerabilities and flaws. Test servers, as platforms for new features and updates, may run older software versions and contain vulnerabilities that can be exploited.
One primary mitigation is to never use raw sensitive data on test servers. Although data masking is resource intensive, it can significantly reduce the impact of potential leaks.
Additionally, a well-structured governance framework is essential. Even with minimal resources, adherence to a clear set of structured rules can greatly enhance the security of test infrastructure.
Final Thoughts
Test server security measures are a critical part of the overall development and testing process. While test environments carry inherent risks that can lead to serious consequences for organizations and users, appropriate security controls can substantially reduce those risks.
Key steps to secure test servers include isolating them on separate networks, deploying robust authentication and authorization mechanisms, regularly patching and configuring servers, restricting access to test data, and performing frequent vulnerability scans.
Security should not be an afterthought but an integral part of every stage of development and testing. By enforcing strong security controls, following industry best practices, and updating security policies in line with current information security trends, organizations can reduce the risks associated with test servers and protect data confidentiality and integrity.