Because many IoT devices lack secure design and often retain default passwords for long periods, they are becoming preferred targets for attackers. In operational technology (OT) networks, the rapid increase in roles and identities assigned to each advanced IoT sensor, and their proximity to mission-critical operational systems, also makes IoT devices attractive entry points for adversaries.
Rising IoT attacks and recent findings
Research shows IoT attacks are growing faster than mainstream cyberattacks. Kaspersky ICS CERT reported that in the second half of 2022, 34.3% of servers in the industrial sector experienced cyberattacks. In the first half of 2021, attacks targeting IoT devices reached 1.5 billion, and more than 40% of OT systems were attacked. SonicWall Capture Labs recorded 112.3 million IoT malware attack instances in 2022, an 87% increase compared with 2021.
Ritesh Agrawal, CEO of Airgap Networks, noted that although IoT endpoints may not be business-critical on their own, they are easy to compromise and can be used to spread malware into an organization’s most valuable systems and data. He recommends that organizations apply basic cybersecurity measures to every IoT endpoint: discovery, segmentation, and identity.
Agrawal also suggested organizations seek solutions that do not require forced upgrades and that will not disrupt IoT networks during deployment. Those are two of the design goals his team identified when creating Airgap Networks.
Manufacturing IoT devices are high-value targets
IoT devices are attractive to attackers because they are easy to target and, in industries where uptime is critical to survival, they can quickly trigger widespread ransomware incidents. Manufacturing has been hit particularly hard because attackers know factories cannot tolerate prolonged downtime, so demanded ransoms are often two to four times higher than for other targets. Research indicates 61% of intrusion attempts and 23% of ransomware attacks are primarily aimed at OT systems.
Forrester identified four key reasons why IoT devices have become such high-value targets and how they are used to launch broader, more destructive attacks within enterprises.
1. Security blind spots in IoT device design
Most legacy IoT devices currently in use were not designed with security as a priority. Many lack options for refreshing firmware or loading new software agents. Despite these limitations, effective methods exist to protect IoT endpoints.
Security measures must cover the blind spots associated with sensors and the network. Shivan Mandalam, director of IoT security product management at CrowdStrike, said organizations must eliminate blind spots linked to unmanaged or unsupported legacy systems. As IT and OT visibility and analytics improve, security teams can identify and remediate issues before adversaries exploit them.
Leading vendors offering IoT security systems and platforms include AirGap Networks, Absolute Software, Armis, Broadcom, Cisco, CradlePoint, CrowdStrike, Entrust, Forescout, Fortinet, Ivanti, JFrog, and Rapid7. In 2022, CrowdStrike expanded Falcon Insight with Falcon Insight XDR and Falcon Discover for IoT to help close security gaps inside and between industrial control systems (ICS).
2. Long-term use of default admin passwords is common
It is common for manufacturers with weaker cybersecurity practices to use default admin passwords on IoT sensors. Teams often rely on default settings because IT staff lack time to configure every device or do not realize configuration options exist. Forrester notes many IoT devices do not require users to set a new password during initialization, nor do they force a password change. Management credentials in legacy devices are frequently unchangeable.
As a result, CISOs, security teams, risk professionals, and IT staff may have a mix of new and old devices on their networks with known credentials.
Vendors that provide solutions to improve password and identity controls on IoT endpoints include Armis, Broadcom, Cisco, CradlePoint, CrowdStrike, Entrust, Forescout, Fortinet, Ivanti, and JFrog. Ivanti has developed several IoT security offerings, including solutions for risk-based vulnerability management, unified endpoint management (UEM), healthcare IoT, and industrial IoT protection.
Srinivas Mukkamala, chief product officer at Ivanti, explained that IoT devices are becoming popular targets. An IBM study found IoT attacks accounted for more than 12% of global malware attacks in 2021, up from 1% in 2019. To address this, organizations should implement unified endpoint management that discovers all assets on the corporate network, including consumer devices that connect via Wi-Fi. Mukkamala added that combining UEM with risk-based vulnerability management is essential for seamless, proactive risk remediation across all devices and operating systems.
3. Healthcare, service, and manufacturing rely on legacy IoT sensors
From hospital wards to factory floors, legacy IoT sensors provide the real-time data these organizations rely on to operate. Healthcare and service industries are high-value targets; attackers aim to compromise IoT to enable lateral movement. For example, 73% of IoT-connected infusion pumps are vulnerable, and 50% of IP voice systems are likewise at risk. Overall, in a typical hospital, roughly half of connected devices are currently at serious risk.
Forrester points out that one major cause is that many of these devices run unsupported operating systems that cannot be protected or updated. If attackers compromise IoT devices that cannot be patched, the risk of device “bricking” increases.
4. The problem is the Internet, not the technology
Forrester observes that once IoT devices are connected to the Internet, they immediately become security liabilities. One security vendor said a major client found an external IP address tied to a camera in a factory lobby. Attackers monitored who entered the building and attempted to blend in with staff to gain physical access and plant devices. Forrester also noted that IoT devices have become channels for command-and-control or components of botnets, as seen in well-known Mirai attacks.
What an IoT attack feels like
Some manufacturers are unsure how to secure legacy IoT devices and programmable logic controllers (PLCs). PLCs provide the real-time data streams required for operational business functions. IoT devices and PLCs are often designed for easy integration rather than security, making it difficult for manufacturers without dedicated IT and security teams to secure their networks.
One Midwestern US auto parts manufacturer experienced a large ransomware attack that targeted unprotected IoT sensors and cameras on its network. Attackers used a variant of R4IoT ransomware and initially breached the IoT devices, video surveillance, and PLCs used for HVAC, power, and mechanical preventive maintenance.
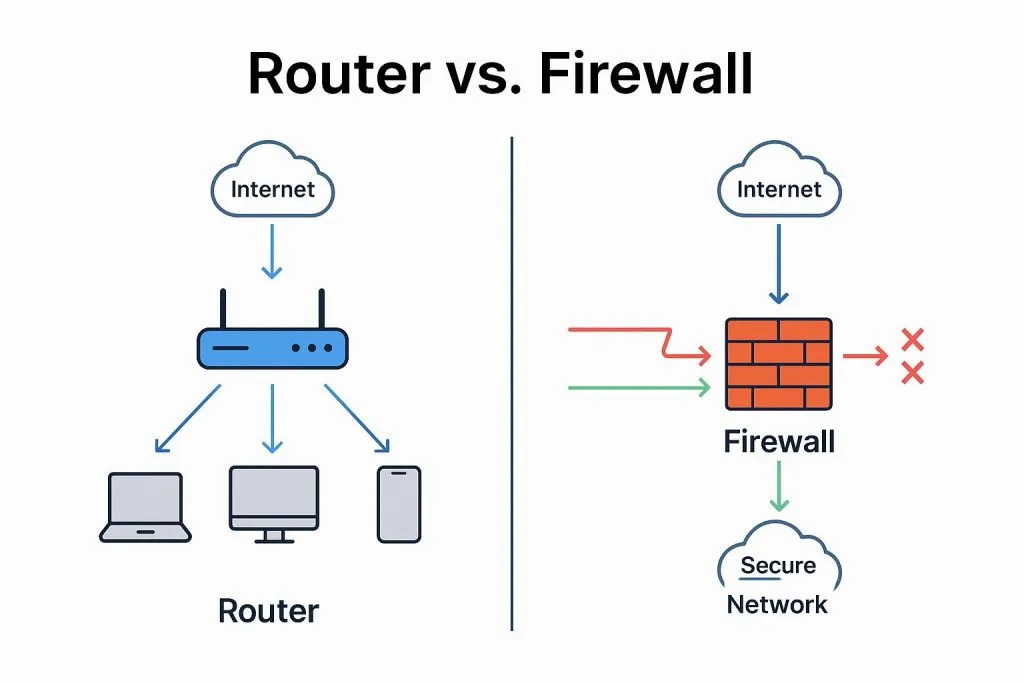
After entering the enterprise network, attackers moved laterally, sought Windows systems, and infected them with ransomware. They obtained administrator privileges, disabled Windows and third-party firewalls, and deployed the R4IoT executable across machines. The attack prevented monitoring of machine temperature, pressure, health, and cycle time, and it froze and encrypted all data files. Attackers also threatened to publish the company’s pricing, customer, and production data to the dark web within 24 hours if a ransom was not paid.
The manufacturer felt compelled to pay the ransom; its security staff were overwhelmed and uncertain how to respond. Attackers exploit the fact that many manufacturers lack dedicated cybersecurity and IT teams. This is why manufacturing continues to be one of the most affected industries. In short, IoT devices have become preferred threat vectors because they are frequently unprotected.
Agrawal said IoT places significant strain on enterprise security maturity. Extending zero trust to IoT is difficult because endpoints vary and environments are dynamic and populated with legacy devices. When asked how manufacturers and other high-risk industries should start, he recommended accurate asset discovery, segmentation, and identity as the correct starting points. However, with most IoT devices unable to accept agents, integrating them with traditional solutions is challenging. That has led many organizations to adopt agentless network security architectures for IoT as a practical approach.