Overview
The transition to autonomous driving and public concern about driverless vehicle safety have made cybersecurity a top priority for automotive original equipment manufacturers (OEMs). Ensuring system integrity and control is essential to protect drivers, passengers, and pedestrians. Cybersecurity is critical for networked vehicle subsystems, including image sensors used for advanced driver assistance systems (ADAS) and driver monitoring.
Role of Image Sensors
Image sensors serve as the vehicle's eyes and support ADAS functions such as lane departure warning, pedestrian detection, and automatic emergency braking (AEB). They enable vehicle systems to assess the surrounding environment and monitor driver behavior. In future use cases, they may also assist with user identification and vital-sign monitoring so that a vehicle can be controlled by onboard systems if the driver becomes incapacitated. For these reasons, image sensors must operate reliably, including under extreme conditions vehicles may encounter.
Four Main Cybersecurity Threats
Automotive image sensors face four primary cybersecurity threats: counterfeiting, tampering, bypass, and eavesdropping, with eavesdropping being especially relevant to in-cabin applications.
Counterfeit Components
Counterfeit products have increased amid the semiconductor supply shortages affecting the automotive industry. Installing non-genuine parts may not always be malicious, but it can degrade system performance. Counterfeit parts often use different boot sequences, protocols, firmware, and software. At best an ADAS system may fail to operate; at worst, the system may use substandard components whose poor performance compromises safety functions.
AEB systems depend on image sensors that meet specific characteristics such as high dynamic range and low-light performance and that are calibrated to specified parameters like exposure control and frames per second. Counterfeit sensors can appear identical to genuine parts while exhibiting very different performance. For example, a counterfeit camera might use the same sensor die but lack the testing required to ensure that the final camera module meets performance requirements, leading to failures under high-stress conditions.
Such parts may function under normal conditions but degrade or fail in other situations, such as hot sunny days or cold winter nights. Some sophisticated counterfeits may emulate the initialization sequence or pass simple device-health checks while offering severely reduced dynamic range or frame rate. Because AEB systems are optimized for genuine components, degraded performance from counterfeit replacements can impair system response and lead to catastrophic outcomes. An object or pedestrian that would previously be detected at a distance allowing several seconds of reaction time may only be detected a few meters away, leaving insufficient time to avoid a collision.
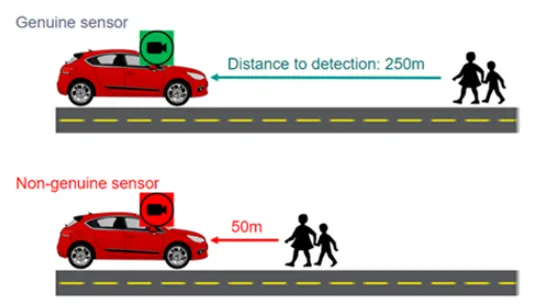
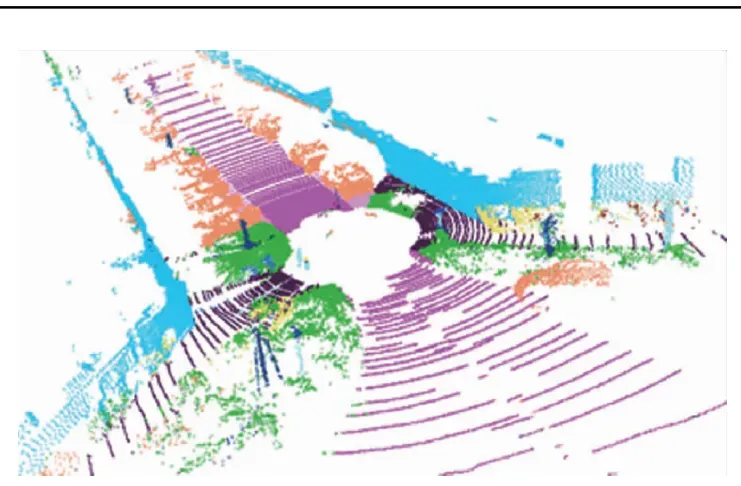
Figure 1: Consequences of replacing genuine image sensors with counterfeit products
Tampering with Sensor Configuration
Modifying image sensor configuration can also harm performance. Vehicle systems program image sensors to optimize image quality for machine vision algorithms that have been certified and tested for specific implementations. If someone or some program changes those configurations, system performance can be affected and the vehicle may no longer perceive driving scenarios correctly.
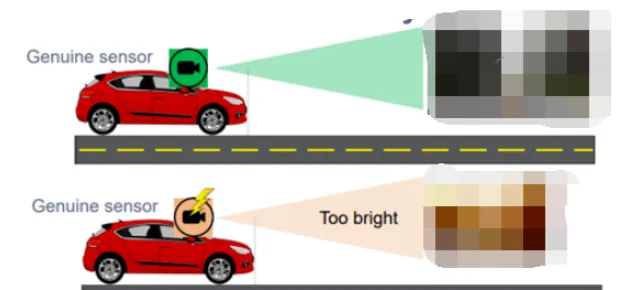
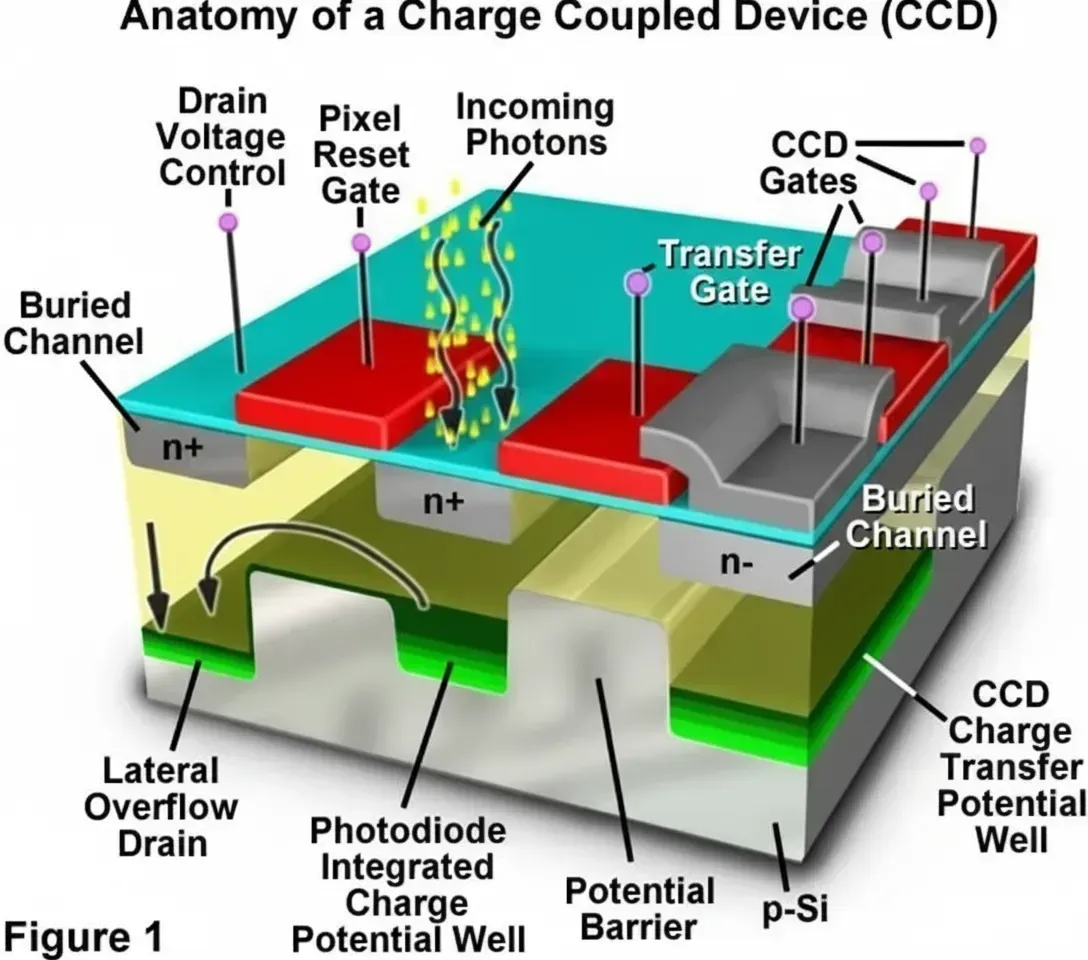
Figure 2: Consequences of tampering with image sensor settings
Bypass and Sensor Failure
An improperly functioning image sensor can effectively render a vehicle "blind" to potential threats. Image sensors supply raw video data to image processors, which extract information about obstacles ahead so the vehicle can respond appropriately. For example, a system that receives raw video data can detect an approaching vehicle and decide whether braking or evasive steering is the safest response. If the image sensor fails to provide raw video data, the system may not detect an oncoming vehicle at all.
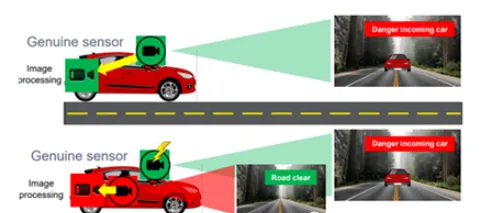
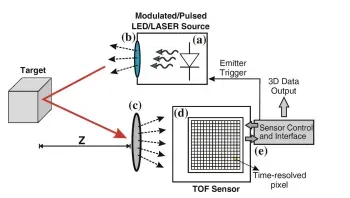
Figure 3: Consequences of image sensor malfunction
Eavesdropping
Eavesdropping on image data streams is a particular concern for in-cabin applications, where sensitive information about occupants may be exposed. Protecting the confidentiality of such data is an important aspect of sensor and system cybersecurity.
Regulatory and Technical Measures
In 2021, the United Nations Economic Commission for Europe (UNECE) working group published the UN-R155 cybersecurity regulation, requiring OEMs to establish a Cybersecurity Management System (CSMS). The regulation came into effect in July 2022 to address the growing threat landscape. Automotive suppliers must ensure that relevant components comply with the ISO 21434 cybersecurity standard. While using ISO 21434-compliant parts alone does not satisfy all UNECE requirements, it is a key element in regulatory compliance.
Onsemi has deployed cybersecurity features in some ADAS image sensors since 2018 to meet cybersecurity requirements. These sensors use authentication mechanisms so a sensor can prove its authenticity to the host, implemented via certificate chains or pre-shared keys. Message authentication codes (MACs) are required to ensure the integrity of video data streams between sensor and host. Protections are also needed for sensor control and configuration data to prevent unauthorized changes to key registers. Because anti-tamper protocols vary by system, the system processor retains final authority to decide how to respond when tampering is detected.
Conclusion
Cybersecurity requirements are essential to prevent automotive image sensors from becoming attack vectors within complex vehicle electronics. For OEMs, achieving compliance requires more than secure circuitry inside the image sensor; sensors with integrated cybersecurity features are a fundamental component for meeting ADAS and in-cabin monitoring cybersecurity standards.