Introduction to Spread-Spectrum Communication
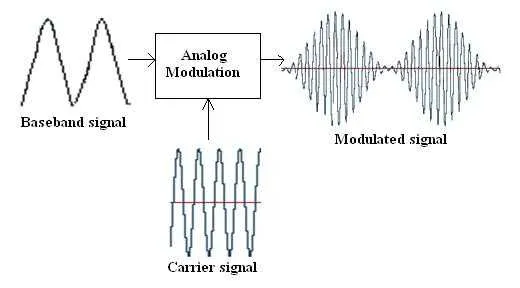
Spread-spectrum communication uses spectrum expansion techniques so that the signal occupies a bandwidth much wider than the minimum bandwidth required by the information being transmitted, thereby improving the communications system's resistance to interference.
1. Principle of Spread Spectrum: Shannon's Theorem
The principle of spread spectrum can be understood by revisiting the Shannon formula. Shannon's theorem defines the maximum rate of a noisy channel as:
C = W * log2(1 + S/N)
where S is the average signal power and N is the average noise power, so S/N is the signal-to-noise ratio (SNR). The conversion between decibels and SNR is: dB = 10 * log10(S/N). A stronger signal or lower noise raises SNR and increases channel rate. For example, a standard telephone line with 3 kHz bandwidth has a baud rate of 6000; depending on modulation it supports different bit rates, but due to noise reaching 9.6 kbps is already good.
When the transmission rate is fixed, increasing the signal bandwidth reduces the required SNR. If the bandwidth is increased sufficiently, the signal power can be allowed to fall below the noise level. Therefore, with a fixed transmit power, spread-spectrum information distributed over a very wide band has a very low useful signal power density. Even when buried in strong noise, reliable communication is possible, giving strong anti-jamming performance. At the same time, spread-spectrum systems use a spreading function (an unpredictable pseudorandom sequence) to modulate and process the signal, which provides high confidentiality. The ratio of the spread-signal bandwidth to the information bandwidth is the spreading factor. Spreading factor values of 1–2 are called narrowband communication; greater than 50 is called wideband communication; greater than 100 is called spread-spectrum communication.
2. Four Spread-Spectrum Techniques
Spread-spectrum systems can be classified into four types:
Direct-Sequence Spread Spectrum (DSSS)
The transmitter multiplies the signal by a high-rate spreading code sequence to expand its spectrum, and the receiver uses the same spreading code to recover the signal. DSSS spreads the signal into a very wide band so that its power spectral density can be lower than the noise floor, hiding the signal in the noise and improving confidentiality. At the receiver, uncorrelated noise is rejected, significantly reducing interference. DSSS is widely used in systems such as CDMA and WLAN.
Frequency-Hopping Spread Spectrum (FHSS)
FHSS uses a pseudorandom code sequence to perform frequency-shift keying so that the carrier frequency hops continuously, expanding the spectrum. The entire spectrum is divided into narrow-band channels; transmitter and receiver operate in each narrow channel for a short time before switching to another. Frequency switching can be random, pseudorandom, or algorithmic depending on the system design. FHSS improves security and anti-jamming because an adversary must track rapid frequency changes to interfere or eavesdrop. FHSS also reduces multipath fading. FHSS is used in WLAN, Bluetooth, and ZigBee. FHSS is commonly used in UAV data radios; typical modules include Digi XBee (900HP, SX Pro, Xtend), Microhard P900, and others that implement FHSS.
Time-Hopping Spread Spectrum (THSS)
THSS is similar to FHSS but performs hops in the time domain: transmissions occur at pseudorandom time slots. Time-domain compression of transmission periods results in spectral expansion. Simple THSS has limited anti-jamming capability and is rarely used alone; it is often combined with other spreading methods to form hybrid systems, such as THSS/DSSS.
Chirp Spread Spectrum / Linear Frequency Modulation (CSS)
If the transmitted signal's carrier frequency varies linearly within a period, it is linear frequency modulation (chirp). Because the instantaneous frequency sweeps a wide band, the signal's bandwidth is widened. CSS is mainly used in radar and low-power wide-area networks (LPWAN) in IoT applications.
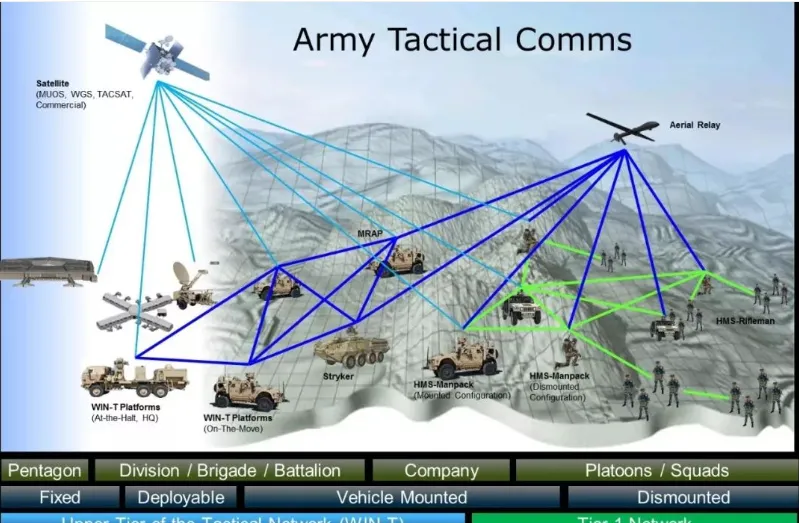
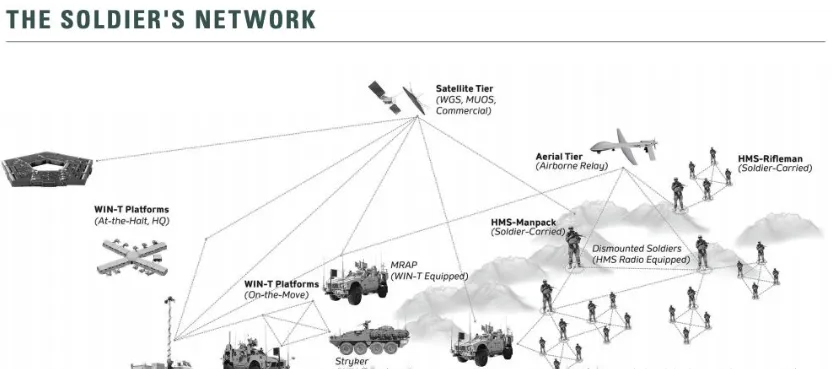
3. U.S. Military Tactical Radios: Broadband Ad-Hoc Networks
Early soldier radios supported basic voice. Later efforts focused on data and voice networking like a mobile phone, but without reliance on fixed base stations. The industry refers to fully decentralized, infrastructureless, dynamic-topology, peer-to-peer, multihop, reconfigurable self-forming networks as ad-hoc. Battlefield and disaster response have been primary use cases.
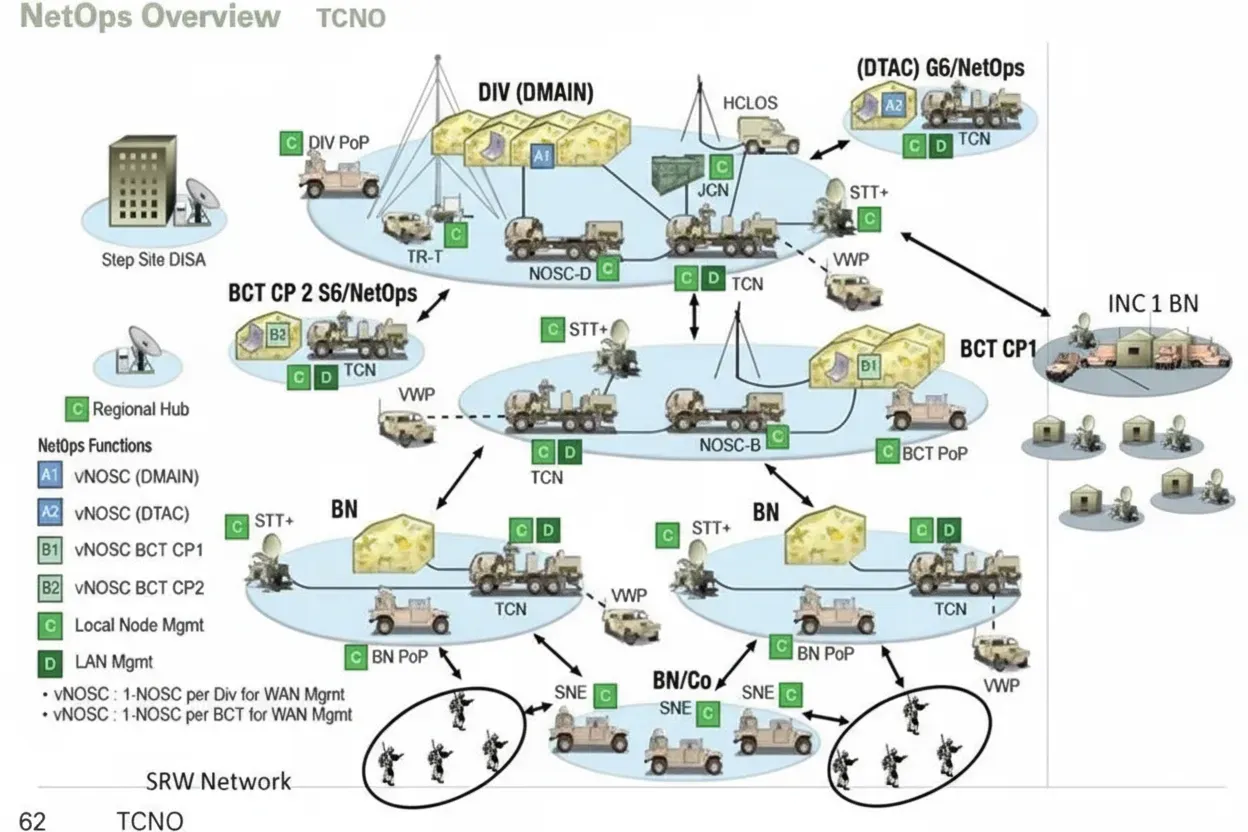
The U.S. Army has used two main radio system types: traditional single-channel ground and airborne radios like SINCGARS, and ad-hoc mobile self-organizing networks (MANET). Since the 1980s, SINCGARS has been the basic radio. As ad-hoc broadband networking technologies matured, soldier radios capable of dynamic broadband networking (SRW) advanced rapidly. Multiple vendors have developed branded solutions that follow military MANET standards within frameworks such as the Joint Tactical Radio System (JTRS).
TrellisWare BRN Network
TrellisWare's SRW solutions are mature and include Tier 1 and Tier 2. Tier 1 covers squad-to-soldier links; Tier 2 covers battalion-to-brigade levels and integrates with higher-layer WIN-T networks to enable data sharing from high headquarters to soldiers in the field. TrellisWare's BRN targets tactical MANET systems and narrowband radios, using virtualized multipath routing to locate nodes and maintain network resilience against link failures. Civilian applications include underground tunnels, mining, vessels, and urban emergency response.
SoldierLink System
The SoldierLink system developed by an established defense contractor implements a mobile tactical cloud communications network. It uses advanced dynamic waveforms and modern network protocols to create a secure, base-station-free MANET that supports data sharing below squad level and bridges important information to higher echelons via WIN-T. SoldierLink nodes can act as switches, routers, access points, or gateways and connect via standard Ethernet. Deployed systems can scale to around 1,000 nodes with per-user encrypted throughput typically in the 5–20 Mbps range. SoldierLink equipment is designed to interoperate with existing tactical networks such as Harris ANW2, SRW, WNW, WIN-T, BFT, tactical cellular, and commercial satellite services.
Soldiers access the network via a ruggedized terminal (often an Android-based handset) that serves as a personal information hub. Supported functions include tactical radio-over-IP (PTT), VoIP telephony, C2/SA applications, ISR reporting, fire support requests, video access, mission file transfer, chat, and maintenance/training points of interest.
WIN-T Backbone
WIN-T is the U.S. Army tactical backbone network. Incremental upgrades have provided battalion-level high-speed data since the mid-2000s and more advanced capabilities in subsequent deployments. WIN-T supports a largely self-organizing network for vehicle-mounted and higher-echelon communications.
Radios such as older PRC-155 manpack radios (now retired) paired with PRC-154 handsets were early examples of dual-channel software-defined radios capable of connecting to satellite networks to provide smartphone-like voice services. These radios supported GPS, encryption, and ad-hoc networking, demonstrating practical use of early MANET technologies despite narrowband constraints at the time.
Persistent Systems MPU5 and Wave Relay
One of the more advanced deployed systems uses Persistent Systems' Wave Relay technology. The MPU5, introduced in 2017, is a smartphone-form-factor radio that supports self-forming, self-healing MANETs with features such as H.264 video streaming, multiple channels, RoIP interfaces, and no central nodes. It is used by military and law enforcement customers.
To address high-frequency, short-range, and multipath challenges in urban, forest, and cave environments, the system uses 3x3 MIMO. Compared to traditional radios it can extend range and deliver throughput over 100 Mbps. RF hardware is modular across S-, L-, and C-bands covering hundreds of MHz to 6 GHz and is intended for tool-based reconfiguration. Units provide up to 10 W transmit power and are built to rugged standards such as IP68 and MIL-STD-810G.
New nodes can join the network in under one second. Network hop count and node count are not limited by the device. Reported range and throughput examples include long-distance links measured in tens to over a hundred miles and peak TCP throughput around 150 Mbps on a 20 MHz channel. Devices include multiple USB and Ethernet ports and support video inputs/outputs such as 3G-SDI and HDMI with onboard H.264 hardware encoding supporting multiple streams. MPU5 and similar systems have seen adoption by police, federal agencies, and civilian users.
4. How Military Radios Ensure Communication Security
Military radios are critical tools for intra- and inter-unit communications. Securing those communications is vital to mission success and force protection. Communication security goals include maintaining confidentiality, preventing eavesdropping, resisting jamming and tampering, and ensuring integrity and availability. The following are key technologies used to ensure military radio security.
Frequency Hopping
Frequency-hopping techniques frequently change the operating frequency during communications. By rapidly switching among frequencies according to a shared sequence, frequency hopping makes interception and jamming more difficult. It reduces the effectiveness of narrowband interference and mitigates multipath fading.
Encrypted Communication
Encrypted communication uses cryptographic algorithms to protect message confidentiality. The sender encrypts plaintext into ciphertext; only receivers with the correct key can recover the plaintext. Military encryption systems use a combination of secure cryptographic devices, strong algorithms, and rigorous key management to protect sensitive information.
Key components include:
- Cryptographic devices: secure phones, encrypted communication terminals, and secure radios that encrypt data during transmission.
- Encryption algorithms: robust symmetric and asymmetric algorithms such as AES and RSA are commonly used to ensure confidentiality and integrity.
- Key management: secure generation, distribution, and storage of keys so that only authorized personnel can access decryption keys.
- Network security: layered security measures in communication networks including firewalls, intrusion detection, and network encryption to prevent unauthorized access and attacks.
- Policies and procedures: identity verification, access control, auditing, and security training to ensure secure operation and handling of communications.
Military encrypted communications are used across command and control, battlefield communications, intelligence collection and sharing, and joint operations. Continuous research and updates to cryptographic and communication technologies are required to address evolving threats and operational needs.
Fielded Radio Types and Procurement
Recent reporting notes large-scale procurement plans for various hand-held and manpack radios for dismounted troops and vehicle/fixed-site platforms. Examples include fielding tens of thousands of hand-held and manpack radios across force inventories to equip units with modern MANET-capable radios and other tactical radios.