Overview of Network Security Devices
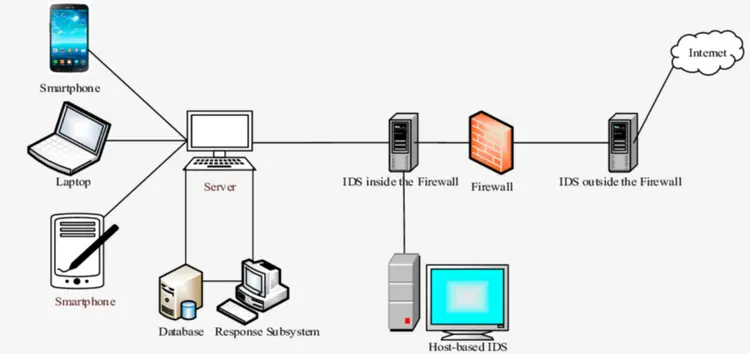
Overview of common network security devices—routers, switches, proxies, firewalls, load balancers, IDS/IPS, SIEM, DLP and UTM—definitions, functions, and security roles.
In the realm of electronics and printed circuit board (PCB) design, Security Devices & Systems represent a critical intersection of technology and protection. This category delves into the hardware and systems that safeguard homes, businesses, and infrastructure against unauthorized access, theft, and other threats. From intrusion detection sensors to advanced biometric locks, these devices rely on sophisticated PCB layouts to ensure reliability and efficiency. Understanding their design principles not only enhances security measures but also drives innovation in fields like IoT integration and wireless communication. Our articles provide comprehensive guides on selecting and assembling components for security systems, including microcontrollers, RF modules, and power management circuits. Tutorials walk through practical builds, such as creating a custom alarm system or integrating cameras with edge computing. Insights into emerging trends, like AI-enhanced surveillance and blockchain for secure data transmission, offer forward-looking perspectives. Best practices emphasize robust PCB design to withstand environmental challenges, ensuring longevity and minimal false positives in real-world deployments. The technical relevance of Security Devices & Systems extends to diverse applications, from residential smart homes that alert users via mobile apps to industrial setups monitoring critical assets in manufacturing plants. By addressing power efficiency, signal integrity, and scalability, these topics equip engineers and hobbyists with the knowledge to implement effective solutions. As cyber-physical threats evolve, staying informed on these systems is essential for maintaining secure environments. Readers will find value in the range of articles here, each building on core concepts to tackle specific challenges in security electronics. Whether optimizing battery life in portable devices or troubleshooting network vulnerabilities, the content fosters a deeper grasp of how PCBs power modern security.
Overview of common network security devices—routers, switches, proxies, firewalls, load balancers, IDS/IPS, SIEM, DLP and UTM—definitions, functions, and security roles.
Technical guide to CentOS 7 firewall management: compares firewalld and iptables, explains zones, netfilter concepts, iptables tables, chains, commands and rule management.
Comprehensive key distribution overview covering KDC-based symmetric key distribution and Kerberos ticket flows, plus public key certification and CA trust.
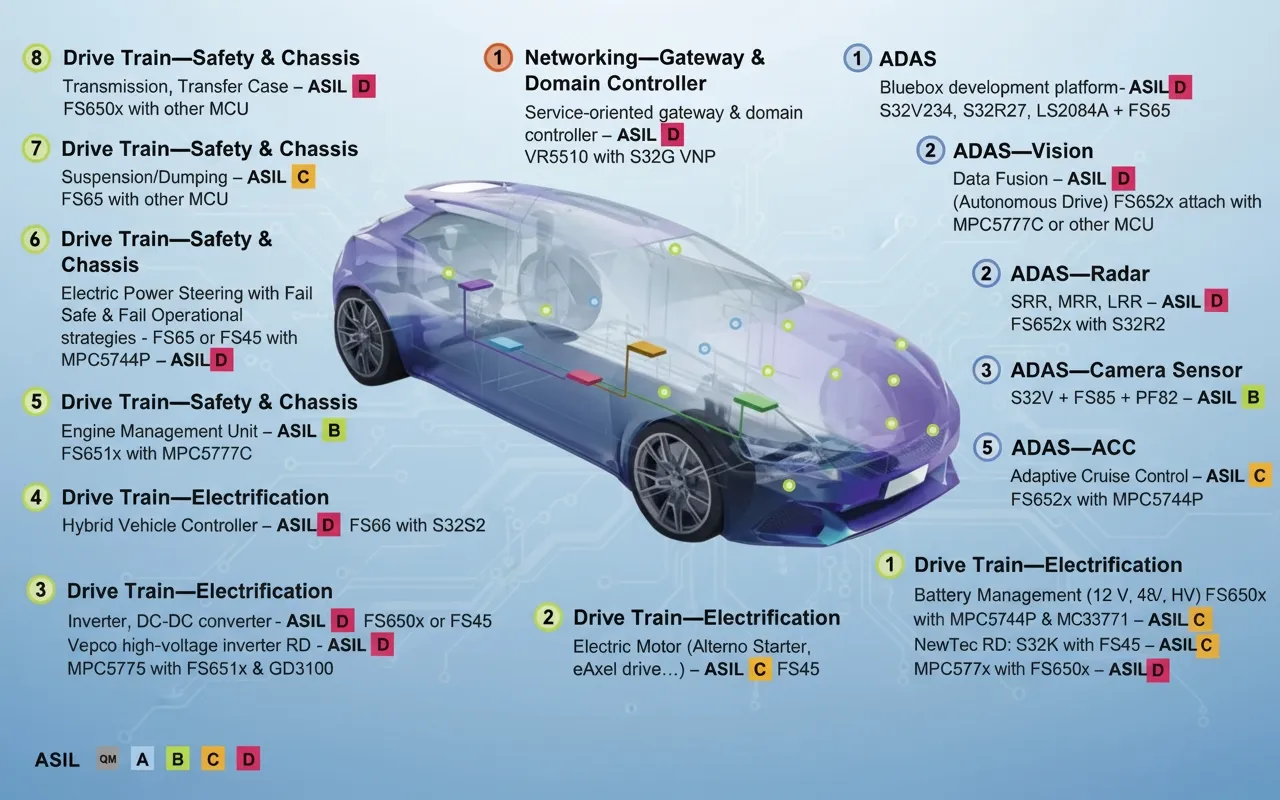
Automotive security requirements covering hardware security, secure boot (signature/MAC/CMAC), secure update processes, cryptographic HSM/SE and communication protection.
Cybersecurity glossary covering malware, vulnerabilities, exploits, phishing, APTs, backdoors, privilege escalation, honeypots and key attack techniques for engineers.
Linux incident response: investigation and remediation of SSH compromise, replaced system utilities, cron persistence, immutable file locks, and ld.so.preload malware.
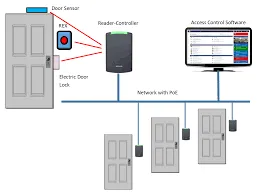
Practical guide to access control installation: site survey, reader/controller and lock wiring, conduit and grounding best practices, and system commissioning.
Technical summary of dual-core lockstep safety chips, their hardware diagnostics, ISO 26262 requirements, representative MCU families, and design considerations.
Overview of trusted data space and data security situation awareness: definitions, mechanisms, challenges, and recommendations for standardizing global data usage state.
Step-by-step checks to determine Linux compromise using audit logs, file integrity checks, process and network inspection, rootkit scanning, and forensic evidence collection.
Overview of six common Android security threats - malware, phishing, unpatched vulnerabilities, public Wi-Fi, USB charging risks, and device theft - with practical countermeasures.