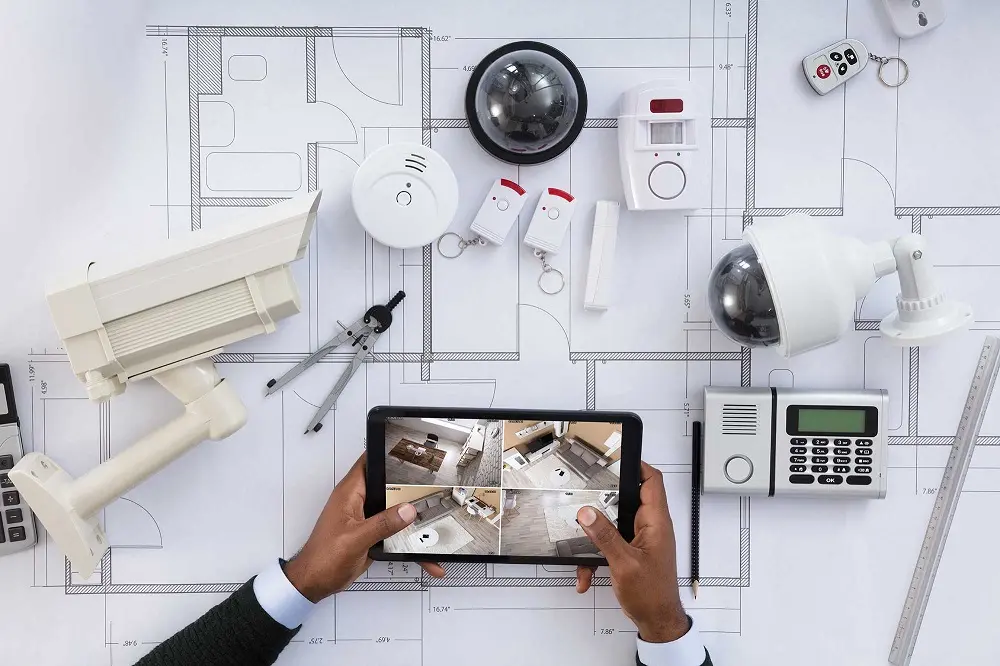
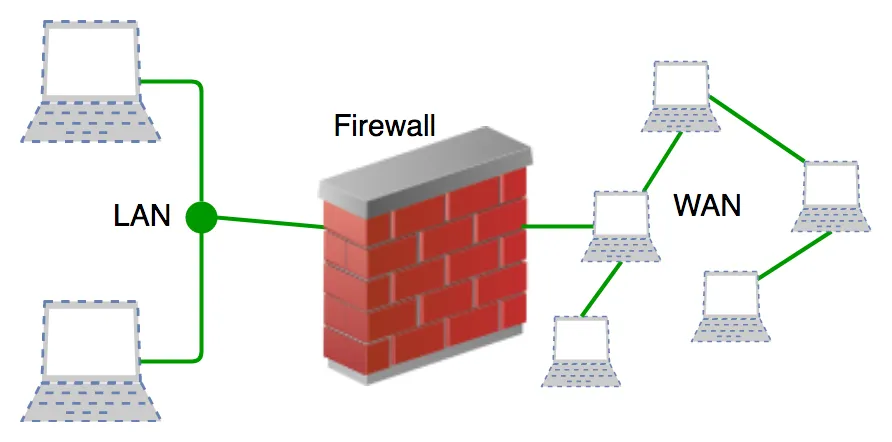
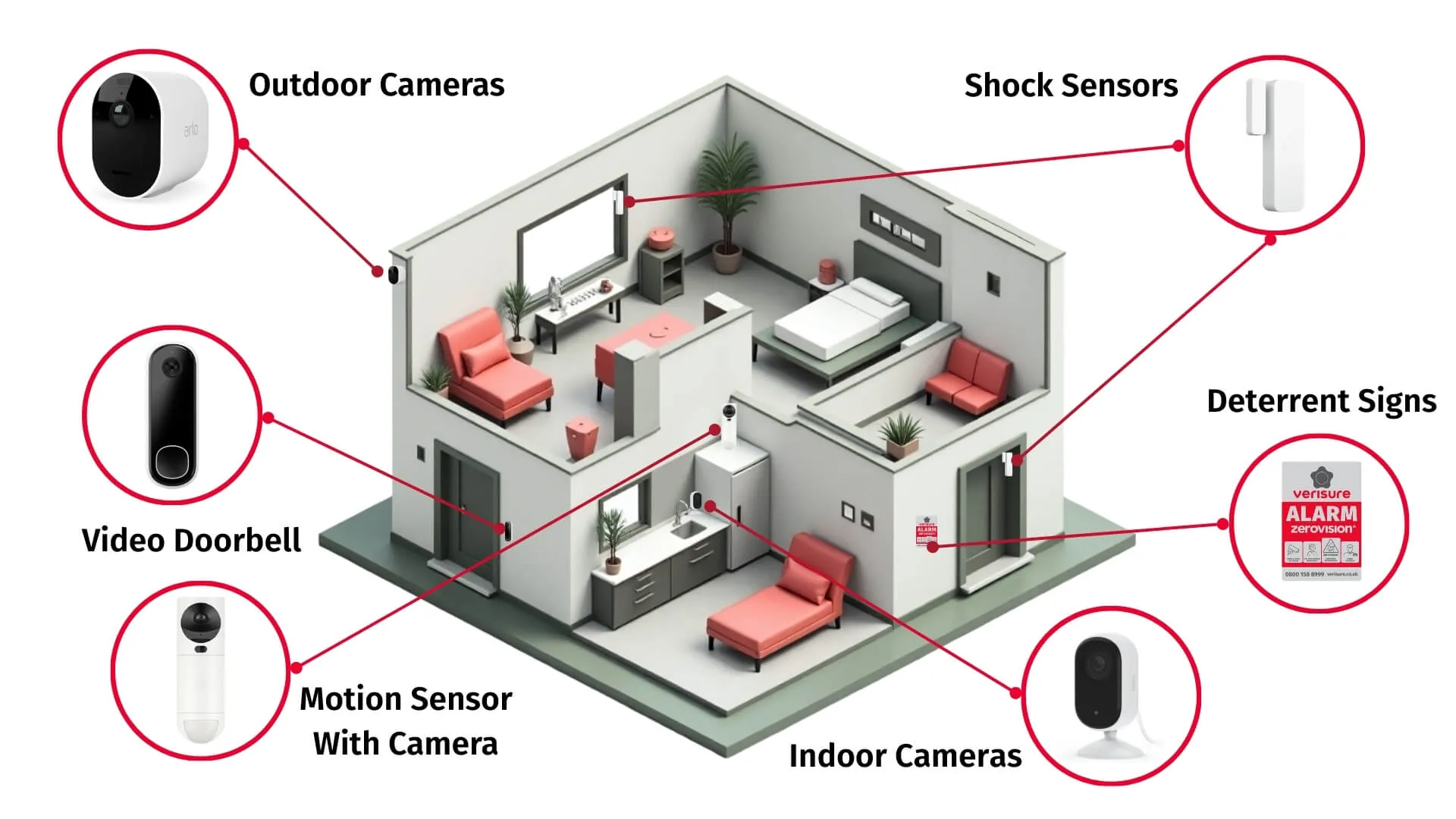
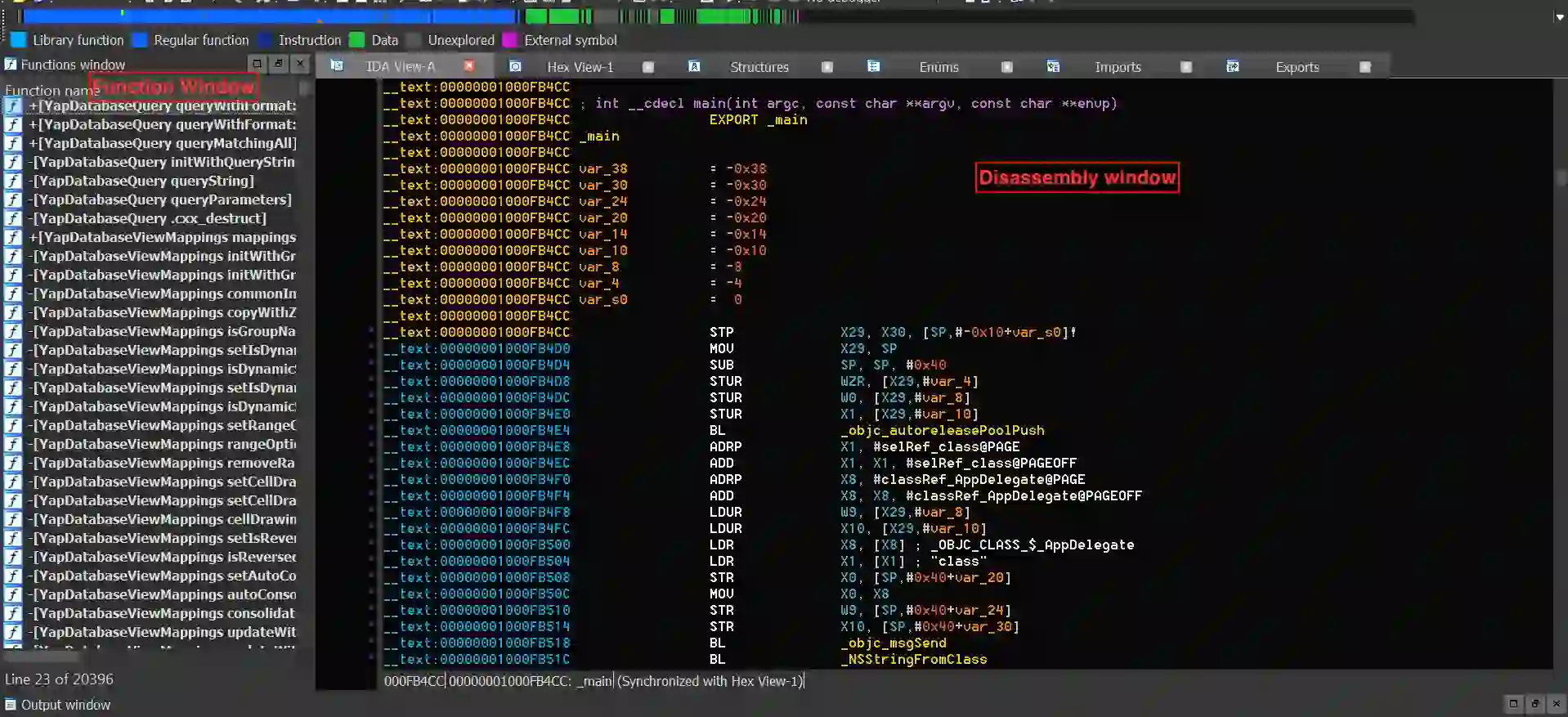
Overview of Network Security Devices: PCB Design, Manufacturing, and Reliability Considerations
Find expert insights on IDS and IPS PCB manufacturing for security systems. Our guide explains how to manage thermal loads and signal integrity for reliable network protection hardware today.