Introduction
Remote access control systems rely on printed circuit boards (PCBs) to manage doors, gates, and entry points over networks. These PCBs integrate microcontrollers, wireless modules, and sensors, enabling administrators to configure settings, monitor status, and grant access from afar. As connectivity grows, so do risks from cyberattacks targeting remote access security. Hackers exploit weak hardware designs to intercept commands, extract credentials, or manipulate relays. Electric engineers must prioritize circuit board security during design to safeguard physical assets. This article explores vulnerabilities, principles, and solutions for robust embedded system security.
Modern access control PCBs handle encrypted communications and firmware updates remotely. Poorly secured boards invite network intrusion detection failures and unauthorized control. Engineers face pressure to balance functionality, cost, and protection. Understanding hardware-level threats ensures designs withstand sophisticated attacks. Proactive measures prevent breaches that could compromise facilities.
What Are Remote Access Control PCBs and Why Security Matters
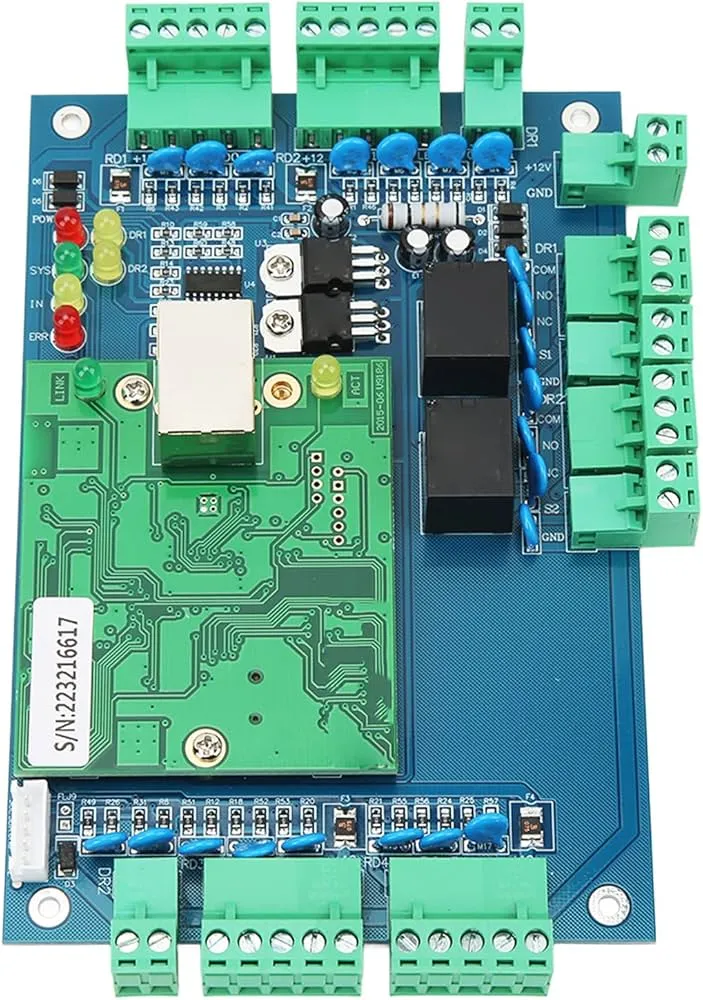
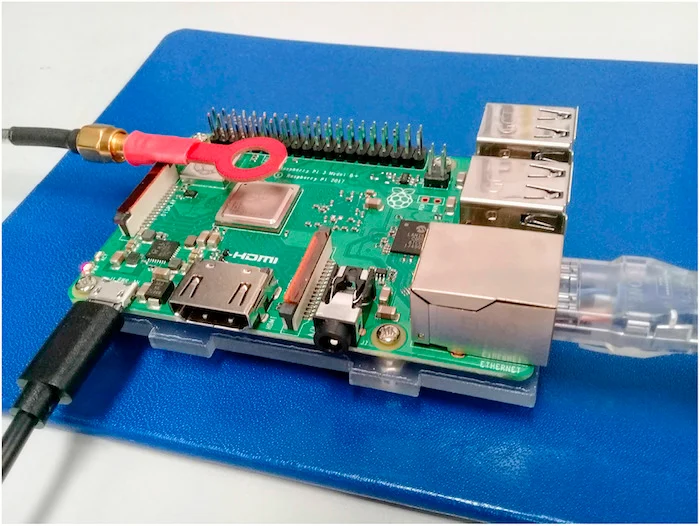
Remote access control PCBs serve as the core of systems controlling physical entry via digital signals. They typically feature a processor, network interface like Ethernet or WiFi, memory for credentials, and output drivers for locks or alarms. Remote access security allows legitimate users to authenticate over IP networks, but exposes the board to internet threats. Engineers design these boards for low power, compact size, and reliability in harsh environments.
Security matters because a hacked PCB grants physical access to buildings, data centers, or secure areas. Attackers bypass doors without traces, leading to theft, sabotage, or worse. In embedded systems, software patches alone fail against hardware exploits like firmware dumping. Circuit board security integrates defenses from layout to assembly, reducing attack surfaces. Industry shifts toward IoT amplify risks, demanding hardware resilience.
Vulnerabilities often stem from exposed debug ports or unshielded traces carrying keys. Without proper remote access security, attackers use tools to replay commands or inject malware. Engineers must consider lifecycle threats, from manufacturing to deployment. Compliance with reliability standards enhances trustworthiness. Protecting these PCBs upholds system integrity.
Common Vulnerabilities and Hacking Vectors in Remote Access Control PCBs
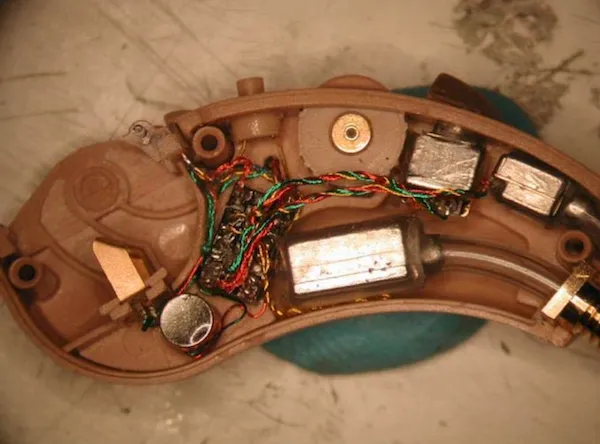
Attackers target remote access control PCBs through physical, network, and supply chain vectors. Physical access enables JTAG probing to read firmware, exposing encryption keys. Side-channel attacks analyze power consumption or electromagnetic emissions to infer secrets. Network vectors involve man-in-the-middle interception of unencrypted traffic. Engineers overlook these during rushed designs, inviting access control hacking prevention gaps.
Firmware vulnerabilities allow remote code execution via buffer overflows. Weak bootloaders permit malicious updates. Supply chain tampering inserts hardware trojans during fabrication. Glitching attacks disrupt power rails to bypass checks. Embedded system security demands awareness of these multi-layer threats.
Unsecured debug interfaces persist in production boards. Exposed antennas leak signals. Poor grounding invites fault injection. Network intrusion detection struggles without hardware support. Logical analysis reveals patterns in high-profile breaches.
Technical Principles of Hardware Security in PCB Design
Secure PCB design begins with a root of trust, often a dedicated secure element storing keys immutably. This chip verifies firmware signatures before execution, enabling secure boot. Cryptographic accelerators offload encryption tasks from the main processor. Engineers route sensitive signals on inner layers, shielded by ground planes. Tamper detection meshes, thin wires under components, trigger erasure if breached.
Power analysis resistance uses constant current regulators to mask operations. Shielding cans over crypto modules block emissions. Obfuscated layouts avoid straight traces for reverse engineering. Epoxy potting encases boards, deterring physical attacks. These principles form layered embedded system security.
Firmware protection includes code signing and rollback prevention. Hardware firewalls filter packets at the PHY layer. Watchdog timers reset on anomalies. Standards like IPC-A-610H guide assembly quality, ensuring joints withstand probing stresses. Reliable fabrication minimizes exploitable defects.
Side-channel mitigations employ noise injection circuits. Differential power analysis requires statistical sampling, thwarted by randomization. Clock glitching detectors monitor frequency drifts. Secure storage fuses disable readouts post-programming. Engineers balance performance with these overheads.
Practical Solutions for Access Control Hacking Prevention
Implement multi-factor authentication at the hardware level using secure elements. Store private keys in tamper-resistant vaults. Enforce TLS 1.3 for all remote sessions, with hardware acceleration. Disable unused ports via fuses. Partition layouts into security zones with moats of ground.
For network intrusion detection, integrate anomaly monitors tracking traffic patterns. Microcontrollers flag unusual packet rates or payloads. Power delivery network sensing detects hardware trojans via voltage anomalies. These lightweight methods suit resource-constrained PCBs.
Physical protections include conformal coatings and metal enclosures. Anti-tamper switches erase keys on casing breach. Firmware over-the-air updates verify chains of trust. Penetration testing simulates attacks pre-production. J-STD-001H ensures soldering integrity for signal fidelity.
Supply chain controls verify component authenticity via markings. Board-level encryption scrambles data at rest. Role-based access limits admin privileges. Logging modules store events in non-volatile memory. Comprehensive testing validates defenses.
Best Practices and Standards Compliance for Circuit Board Security
Adopt defense-in-depth: combine hardware, firmware, and network layers. Use multi-layer boards for trace hiding. Minimize test points; fuse them post-programming. Select components with built-in security features. Simulate attacks in design tools.
Compliance with IEC 62443 frameworks guides system-level protections. It outlines zones and conduits for secure communications. IPC-6012E specifications ensure PCB performance under stress, vital for secure operations. Regular audits verify implementations.
Prototyping includes red-team exercises. Update designs iteratively. Train teams on threats. Documentation details security features. These practices elevate remote access security.
Conclusion
Securing remote access control PCBs demands vigilant hardware design against diverse threats. From secure elements to tamper meshes, layered defenses fortify embedded system security. Engineers applying these principles alongside standards like IPC-A-610H, J-STD-001H, and IEC 62443 mitigate risks effectively. Proactive circuit board security prevents devastating hacks. Prioritize these considerations for reliable, hack-resistant systems.
FAQs
Q1: What are key hardware features for remote access security in PCBs?
A1: Secure elements provide root of trust for key storage and boot verification. Tamper meshes detect physical intrusions, erasing secrets. Shielded traces prevent side-channel leaks. These features ensure encrypted communications resist interception. Compliance with assembly standards maintains reliability.
Q2: How does network intrusion detection work on access control PCBs?
A2: Lightweight monitors analyze packet anomalies like rate spikes or malformed headers. Power sensing flags trojan activity via irregular draws. Microcontrollers trigger alerts or resets. This hardware support complements software IDS. It enables real-time access control hacking prevention in embedded environments.
Q3: Why integrate standards like IPC-A-610H in circuit board security?
A3: Standards define acceptability criteria for assemblies, ensuring joints and traces withstand tampering attempts. Reliable fabrication reduces failure points attackers exploit. They promote consistent quality across production. Electric engineers use them to validate designs against environmental stresses. This bolsters overall embedded system security.
Q4: What best practices prevent firmware hacking in remote PCBs?
A4: Enforce secure boot with signing. Fuse debug ports post-deployment. Use hardware vaults for code. Implement OTA updates with integrity checks. These steps block extraction and injection. Combined with obfuscation, they strengthen defenses.
IPC-A-610H — Acceptability of Electronic Assemblies. IPC, 2019
J-STD-001H — Requirements for Soldered Electrical and Electronic Assemblies. IPC, 2018
IPC-6012E — Qualification and Performance Specification for Rigid Printed Boards. IPC, 2017
IEC 62443-4-2:2015 — Security for industrial automation and control systems. IEC, 2015